Self-hosted agent runtimes like OpenClaw significantly widen the execution boundary by ingesting untrusted text, downloading and executing external skills, and acting with the credentials of the host, creating risks of credential exposure, persistent memory manipulation, and host compromise. Organizations should treat OpenClaw as untrusted code execution and, if evaluated, run it only in isolated environments with dedicated non-privileged credentials, continuous monitoring, and a rebuild plan. #OpenClaw #Moltbook
Keypoints
- OpenClaw (runtime) can download and execute third‑party skills and act using host credentials, shifting the trust boundary from static application code to dynamic content and plugins.
- Moltbook (platform) amplifies attacker influence by serving as a high‑volume instruction feed that multiple agents can ingest, enabling indirect prompt injection at scale.
- Three primary risks in unguarded deployments are credential/data exfiltration, persistent state/memory manipulation, and host compromise via retrieved malicious code.
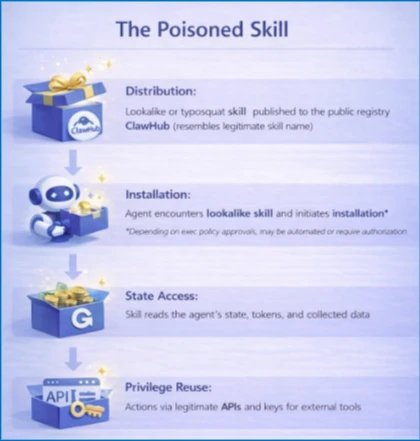
- Attack chains commonly start with a malicious skill published to ClawHub, proceed through installation and state access, and achieve persistence via configuration changes or scheduled actions.
- Minimum safe posture: run agents only in fully isolated VMs or physical systems, use dedicated non‑privileged credentials and non‑sensitive data, monitor state changes, and plan for rapid rebuilds.
- Microsoft controls (Defender for Endpoint, Defender XDR, Defender for Cloud Apps, Microsoft Purview, Entra ID) can help contain, monitor, and respond to agent-related risks when applied to identity, host, supply chain, network, and data protections.
MITRE Techniques
- [T1195] Supply Chain Compromise – The article describes malicious skills published to ClawHub that create “a direct code supply chain path into the runtime” (‘An attacker publishes a malicious skill to ClawHub…creates a direct code supply chain path into the runtime.’)
- [T1105] Ingress Tool Transfer – Attackers and skills download and execute code in the runtime: ‘download and execute skills (i.e. code) from external sources’
- [T1059] Command and Scripting Interpreter – Agents spawn shells or use scripting/tools to perform actions on hosts: ‘Agent runtimes spawning unexpected shells or download tools’
- [T1078] Valid Accounts – Compromise leverages existing tokens and identities to perform actions through legitimate APIs: ‘With valid identity material, the attacker can perform actions through standard APIs and tooling.’
- [T1053] Scheduled Task/Job – Persistence is achieved via scheduled executions and durable configuration changes: ‘Persistence frequently manifests as durable configuration changes, such as new OAuth consents, scheduled executions, modified agent tasks…’
- [T1041] Exfiltration Over C2 Channel – The writeup warns credentials and accessible data “may be exposed or exfiltrated,” describing data theft risks from the agent environment (‘Credentials and accessible data may be exposed or exfiltrated.’)
Indicators of Compromise
- [File/Process names] agent runtimes and tools – openclaw, moltbot, clawdbot
- [Command lines / installer invocations] skill installation and runtime execution – “clawhub install “, process command lines containing “openclaw” or “moltbot”
- [Folder paths / workspace files] agent state and backup paths – .openclaw/workspace (agent working state), .openclaw/ (entire runtime including tokens)
- [Editor extension locations] developer extension churn indicative of suspicious installs – .vscode/extensions/ (newly created or modified extension folders)
- [Child processes / common download tools] indicators of opportunistic execution – cmd.exe, powershell.exe, pwsh.exe, curl, wget (spawned by agent processes)