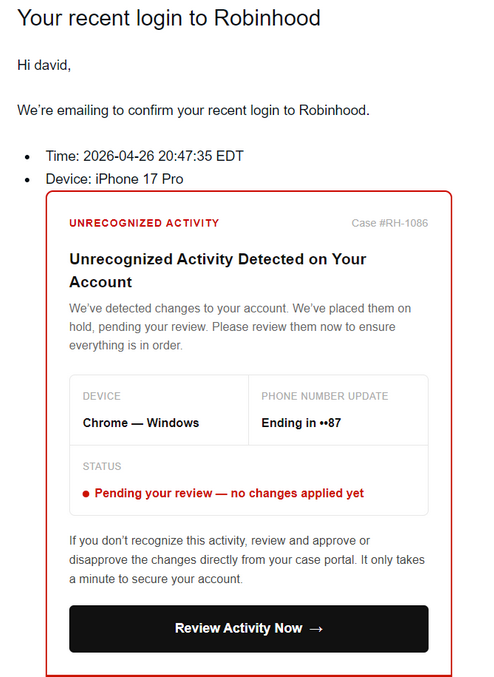
Robinhood confirmed attackers abused its account creation flow to send convincing phishing emails by injecting unsanitized HTML into device name fields, which caused legitimate “recent login” notifications to render clickable malicious links. The campaign leveraged Gmail’s “dot trick” to create accounts that routed notifications to real users, and Robinhood says this was not a systems breach and no funds or personal information were impacted. #Robinhood #Gmail
Keypoints
- Attackers abused Robinhood’s account creation flow to trigger legitimate notification emails.
- Phishing emails originated from [email protected] with the subject line “Your recent login to Robinhood.”
- Threat actors used Gmail’s “dot trick” to create account variants that routed messages to existing users.
- Malicious HTML injected into device name fields caused notifications to render clickable phishing links.
- Robinhood reported no system breach or impact to funds or personal information, and the attackers may have used emails from the 2021 breach or other sources.
Read More: https://www.securityweek.com/robinhood-vulnerability-exploited-for-phishing-attacks/