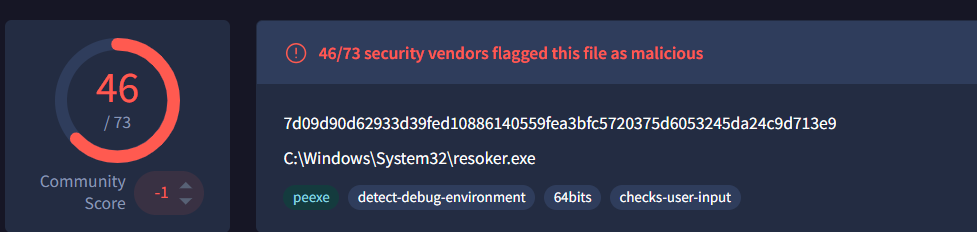
ResokerRAT is a Telegram-controlled Remote Access Trojan that uses the Telegram Bot API as its command-and-control channel to receive commands and exfiltrate data, while implementing persistence, privilege escalation, anti-analysis, and system monitoring features. It supports commands such as /screenshot, /download, /block_taskmgr, and /startup and uses hidden PowerShell execution, registry modifications, keyboard hooks, and process termination to maintain stealth. #ResokerRAT #TelegramBot
Keypoints
- ResokerRAT uses the Telegram Bot API as its C2 channel, constructing bot URLs with a bot token and chat ID to receive commands and send data back to the attacker.
- The malware establishes persistence by adding a Run registry value named “Resoker” under HKCUSoftwareMicrosoftWindowsCurrentVersionRun.
- It attempts privilege escalation by relaunching itself with administrator rights via ShellExecuteExA using the “runas” option and reports success/failure to the C2.
- ResokerRAT implements anti-analysis measures: mutex creation, IsDebuggerPresent checks, termination of analysis tools (Taskmgr.exe, Procexp.exe, ProcessHacker.exe), and a global keyboard hook that blocks key combinations like ALT+TAB and CTRL+ALT+DEL.
- Remote commands include /screenshot (hidden PowerShell capture saved to a Screenshots folder), /download (hidden PowerShell download to a Downloads folder), /block_taskmgr and /unblock_taskmgr (modify DisableTaskMgr registry value), and UAC manipulation (/uac-min and /uac-max).
- Network activity is encoded (URL encoding) and sent over HTTPS to Telegram endpoints; examples observed include api.telegram.org bot endpoints and IP 149.154.166.110, and the malware logs execution events locally.
MITRE Techniques
- [T1059.001 ] PowerShell – Uses hidden PowerShell commands to capture screenshots, download files, and execute commands (‘PowerShell starts with hidden window’).
- [T1547.001 ] Set Registry Value – Establishes persistence by adding a Run key entry “Resoker” under HKCUSoftwareMicrosoftWindowsCurrentVersionRun (‘adds its executable path to a Windows Run registry value named “Resoker”’).
- [T1134 ] Access Token Manipulation – Attempts to obtain elevated privileges and relaunch with admin rights to modify process privileges (‘relaunch the program with administrator privileges … uses ShellExecuteExA with the “runas” option’).
- [T1202 ] Indirect Command Execution – Executes indirect PowerShell commands to perform actions like capturing the screen and downloading payloads (‘runs a hidden PowerShell command … captures the screen’ and ‘uses a hidden PowerShell command … download’).
- [T1562.001 ] Impair Defences: Disable or Modify Tools – Disables Task Manager by setting DisableTaskMgr to 1 to prevent user termination of the malware (‘modifies a Windows registry value called DisableTaskMgr and sets it to 1’).
- [T1564.003 ] Hidden Window – Launches PowerShell with hidden window style so actions (screenshot, download) occur silently (‘PowerShell starts with hidden window’).
- [T1057 ] Process Discovery – Enumerates running processes and inspects process names to detect monitoring/analysis tools (‘Checks the running processes using Process32NextW and checks their names’).
- [T1056.001 ] Input Capture – Installs a global keyboard hook using SetWindowsHookExW to monitor and block specific key combinations (‘installs a global keyboard hook … monitors and blocks specific key combinations’).
- [T1071 ] Application Layer Protocol – Uses HTTPS requests to Telegram Bot API endpoints to receive commands and send collected data (‘constructs a URL containing a Telegram bot token and chat ID’ and ‘communicates with the Telegram bot’).
- [T1573 ] Encrypted Channel – Communicates with Telegram over HTTPS to protect C2 traffic (‘Establishes an encrypted HTTPS connection to Telegram Bot’).
Indicators of Compromise
- [File Hash ] Sample malware binary – 7a1d6c969e34ea61b2ea7a714a56d143 (Resoker.exe)
- [File Name ] Observed malware filename – Resoker.exe
- [Domain / URL ] Telegram C2 endpoints – hxxps://api.telegram[.]org/bot8679995457:AAHiI3UDWmJaj4etgI4fAZK_wo4KJfhXLWc/getUpdates, hxxps://api.telegram[.]org/…/sendMessage (bot API endpoints observed in C2 traffic)
- [IP Address ] Observed network host – 149[.]154[.]166[.]110 (associated with Telegram API traffic)
- [Credentials / Identifiers ] Telegram bot token and chat ID used for C2 – bot8679995457:AAHiI3UDWmJaj4etgI4fAZK_wo4KJfhXLWc, chat_id=8558596408
Read more: https://labs.k7computing.com/index.php/resoker-a-telegram-based-remote-access-trojan/