The Qilin ransomware group has been highly active, employing advanced tactics such as deploying Linux ransomware on Windows systems and targeting backup infrastructure. These sophisticated attack methods include social engineering, credential harvesting, and defense evasion techniques, highlighting the importance of robust security measures. #Qilin #RansomwareGroup
Keypoints
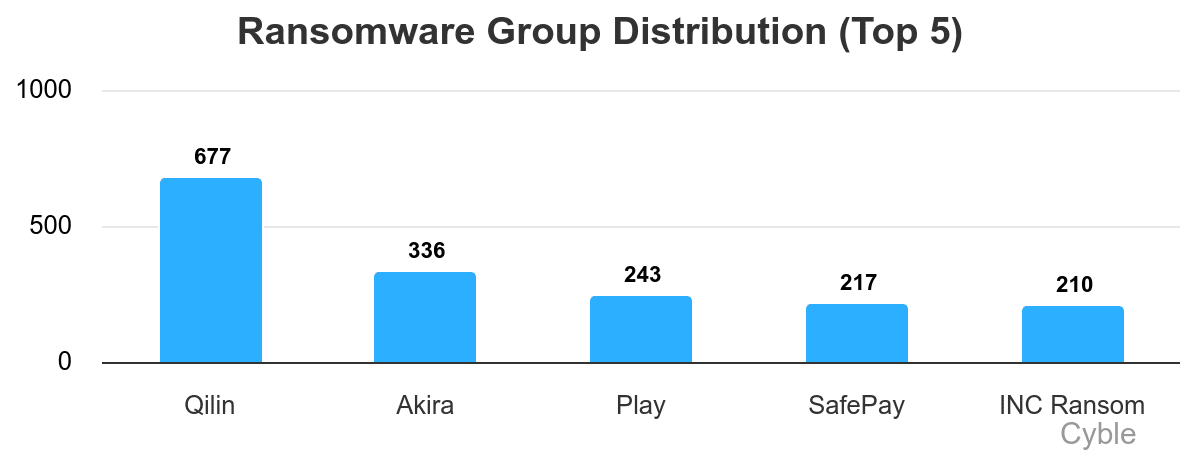
- The Qilin group is the most active ransomware entity over the past seven months, with over 677 attacks documented.
- Attacks involve deploying Linux ransomware on Windows systems using remote management tools and obfuscation techniques.
- Threat actors target backup infrastructures like Veeam to harvest credentials and facilitate lateral movement.
- Qilin employs anti-analysis, anti-AV, and defense evasion tactics such as obfuscated PowerShell and driver-based attacks.
- The use of legitimate remote tools and multi-platform execution complicates detection and requires enhanced security practices.
Read More: https://thecyberexpress.com/qilin-ransomware-group-ttps/