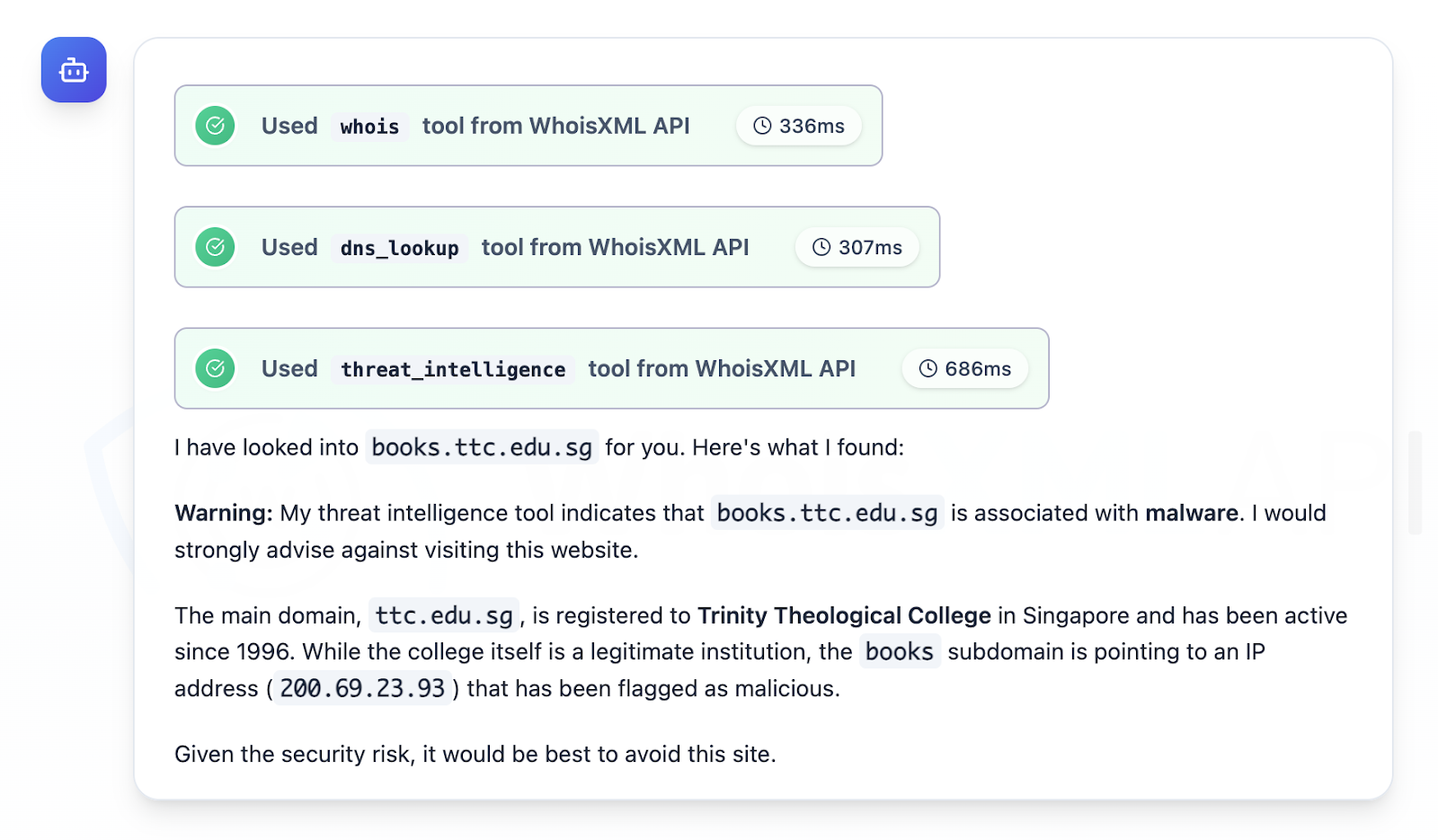
CloudSEK and follow-up research focused on QakBot as a top access trojan/loader that is commonly distributed via phishing, harvests credentials, maintains C2 access, delivers payloads, and moves laterally to enable targeted attacks and ransomware against email-reliant enterprises. The investigation analyzed Trellix IoCs (extracted 929 domains, filtered to 492, studied 125), 19 subdomains, multiple client and infrastructure IPs, and thousands of email-connected domains, identifying specific malicious artifacts (e.g., books[.]ttc[.]edu[.]sg -> 200[.]69[.]23[.]93) and providing a downloadable dataset for further hunting. #QakBot #Trellix
Keypoints
- QakBot is highlighted as a prolific access trojan/loader distributed primarily via phishing and used to harvest credentials, maintain C2, deliver payloads, and enable rapid lateral movement for ransomware and targeted attacks.
- Researchers ingested a Trellix IoC list, extracting 929 unique domains then using WhoisXML MCP Server to filter to 492 suspect domains and focusing analysis on 125 domains and 19 subdomains (144 IoCs total).
- Analysis of network telemetry showed 15 unique client IPs under seven ASNs communicating with 18 IoC domains via 275 DNS queries between 23 Dec 2025 and 20 Jan 2026.
- Eight of the 125 studied domains were registered with malicious intent from creation, while many older domains likely represent compromised legitimate sites used in attacks.
- WHOIS history revealed 360 unique historical WHOIS email addresses (105 public), which mapped to 11,325 email-connected domains; threat queries flagged nine of those as weaponized.
- Researchers identified concrete malicious artifacts including a flagged subdomain books[.]ttc[.]edu[.]sg resolving to 200[.]69[.]23[.]93 and compiled downloadable artifacts and a dataset for further threat hunting.
MITRE Techniques
- [T1566 ] Phishing – QakBot is frequently distributed via phishing emails (‘Often distributed via phishing emails’)
- [T1003 ] Credential Dumping – QakBot is noted for harvesting credentials (‘harvesting credentials’)
- [T1071 ] Application Layer Protocol (Command and Control) – used to maintain remote access and C2 communications (‘maintaining C&C access’)
- [T1021 ] Remote Services – leveraged for rapid lateral movement across enterprise networks (‘rapid lateral movement useful for targeted attacks and serving ransomware’)
- [T1105 ] Ingress Tool Transfer – used to deliver additional malicious payloads to compromised hosts (‘delivering various payloads’)
Indicators of Compromise
- [Domain ] domains extracted and analyzed from Trellix IoC list – ankitashrivastava[.]com, ansaf[.]or[.]tz, and 122 more domains from the 125-domain analysis set
- [Subdomain ] flagged malicious subdomain from the Trellix list – books[.]ttc[.]edu[.]sg (points to 200[.]69[.]23[.]93); 18 other subdomains were benign/legitimate
- [IP address ] infrastructure and client IPs observed in telemetry – 200[.]69[.]23[.]93 (malicious), and additional IPs (108 total observed, 60 identified as malicious)
- [Email‑connected domain ] domains discovered via historical WHOIS email addresses – garagedoorrepairchicopeema[.]com, alltopposts[.]com, and 11,323 other email-connected domains (11,325 total)
- [WHOIS email addresses ] historical registrant emails found in WHOIS history – 360 unique WHOIS email addresses (105 public addresses used for reverse-WHOIS pivoting; specific addresses withheld in source)
- [IP‑connected / string‑connected domains ] connections discovered via IP and string pivots – 1,595 IP-connected domains (1 malicious) and 1,404 string-connected domains (1 malicious) identified during analysis
Read more: https://circleid.com/posts/qakbot-named-a-2026-top-malware-threat-an-ioc-analysis