CloudSEK identified interconnected phishing campaigns impersonating Canadian government bodies and national brands (traffic-ticket portals, CRA, Canada Post, Air Canada) to harvest PII and financial data using SMS lures, typosquatted domains, and fake payment gateways. The activity aligns with the PayTool ecosystem and is being commoditized on underground forums by a seller advertising specialized phishing kits. #PayTool #theghostorder01
Keypoints
- Multiple interconnected fraud clusters impersonate Canadian services (traffic ticket portals, CRA, Canada Post, Air Canada) to harvest personal and financial information.
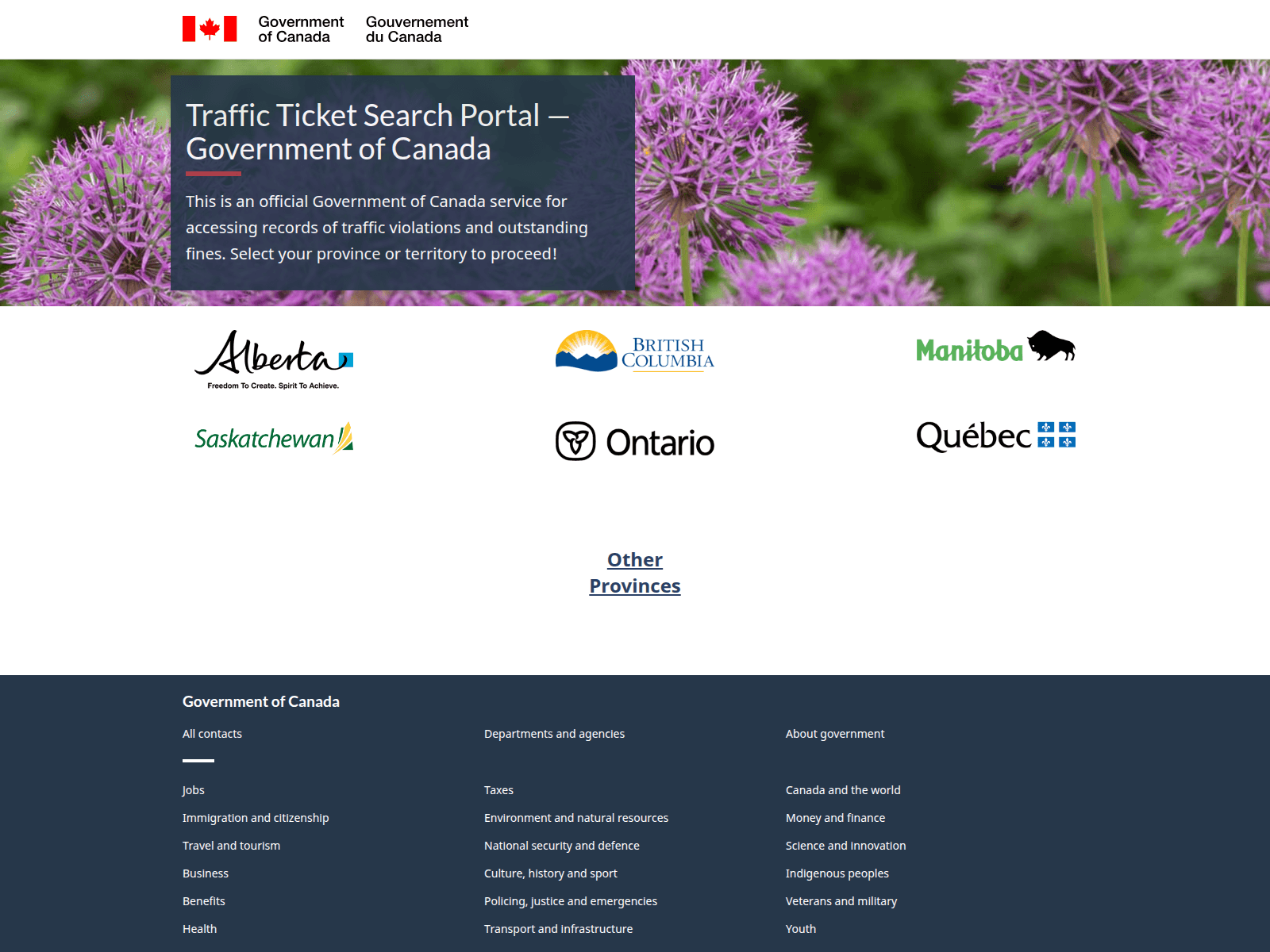
- A core portion of activity maps to the PayTool phishing ecosystem, extending provincial fine-payment scams into a centralized “Traffic Ticket Search Portal” model to increase trust and scalability.
- Attack vectors include SMS-based smishing, malicious ads, URL shorteners, typosquatted domains, and SEO-poisoned/typosquatted Air Canada clones.
- Infrastructure shows systematic domain naming and high reuse of hosting subnets (notably 45.156.87.0/24 and 198[.]23[.]156[.]130) with over 70 domains linked to shared IPs.
- Threat actors are commercializing phishing kits on underground forums (actor alias ‘theghostorder01’), lowering technical barriers by offering PhaaS-style kits and support via messaging channels.
- Mitigations recommended: proactive domain monitoring and takedowns, DNS/web gateway controls, public awareness about SMS payment requests, and threat-intel driven detections for shared hosting patterns and asset reuse.
MITRE Techniques
- [T1566 ] Phishing – SMS-based social engineering and malicious links used to lure victims into fake portals (‘a known fraud framework that specializes in traffic violation and fine payment scams targeting Canadians through SMS-based social engineering.’)
- [T1204.002 ] User Execution: Malicious Link – Victims are persuaded to click links and interact with “fake validation” forms that prime users before presenting fraudulent payment pages (‘Upon clicking, victims are not immediately asked for data. Instead, they are taken through a “fake validation” phase.’)
- [T1583 ] Acquire Infrastructure – Bulk domain registration, systematic naming patterns, and reuse of hosting subnets to deploy and rotate phishing sites (‘The domains associated with this cluster exhibit highly systematic naming conventions centered around:“ticket”“traffic”“portal”“search”“violation”’)
- [T1588 ] Obtain Capabilities – Purchasing and selling phishing kits and PhaaS offerings on underground forums to deploy high-fidelity scams (‘selling a specialized phishing kit designed to mimic the Ontario Driver’s License Renewal process on multiple dark web forums.’)
Indicators of Compromise
- [IP Address ] Hosting and phishing infrastructure – 45[.]156[.]87[.]145, 198[.]23[.]156[.]130, and other 16 IPs
- [Domain ] Phishing and typosquat domains impersonating Canadian services – paytool-bc-2025[.]com, ticket-search-portal[.]com, aircanda-booking[.]com, and other dozens of domains
- [Domain ] Canada Post / parcel redelivery lures – redeliverparcel[.]info, handlingparcel[.]info
- [Email ] Threat actor contact – theghostorder01@gmail[.]com
- [Cryptocurrency Address ] Payment / sales channels advertised on forums – USDT: TWNCawkk3NbPZsY6mdnog8Sn7rS2vue95d, BTC: bc1qvhxkqujf347apsgy65ffykste0jy6txhgejhm048ukrys7cm6d3q2v4ze7