Phishing actors exploit complex mail routing and misconfigured spoof protections to send emails that appear to originate from an organization’s own domain, increasing success of credential phishing and invoice/financial scams. Microsoft observed widespread use of PhaaS platforms like Tycoon2FA in these opportunistic campaigns and recommends enforcing strict SPF/DMARC, properly configuring third-party connectors, and deploying phishing-resistant MFA to mitigate risk. #Tycoon2FA #Office365
Keypoints
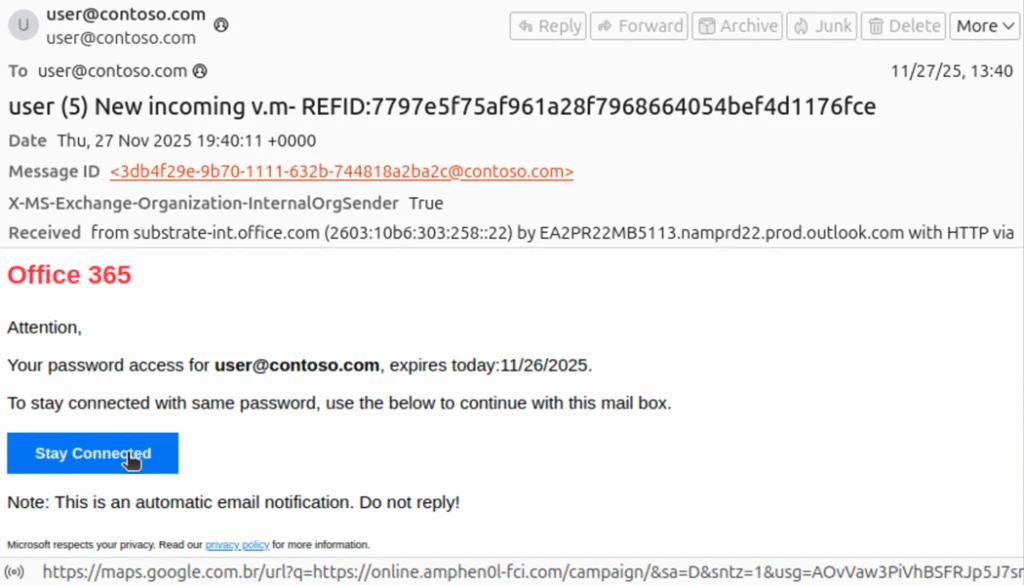
- Threat actors abuse complex routing scenarios and improperly configured spoof protections to send emails that superficially appear to be internal communications.
- Phishing-as-a-service (PhaaS) platforms—most notably Tycoon2FA—are commonly used to deliver credential-phishing and AiTM sequences that can bypass MFA protections.
- Campaigns observed since May 2025 are opportunistic across industries and include credential theft lures (voicemail, shared documents, password resets, HR) and financial invoice scams targeting accounting workflows.
- Tenants whose MX records point directly to Office 365 are protected by native spoofing detection; tenants with MX records routed via on-premises or third-party services are at higher risk if spoof protections are permissive.
- Email header artifacts (e.g., InternalOrgSender=True + MessageDirectionality=Incoming and AuthAs=Anonymous) and SPF/DMARC/DKIM failures help identify spoofed messages, but misconfigured connectors can prevent enforcement.
- Microsoft Defender for Office 365 blocks many of these messages, and recommended mitigations include enforcing DMARC reject/SPF hardfail, configuring connectors properly, enabling Safe Links, ZAP, and phishing-resistant MFA.
- Successful compromises can lead to account takeover, data theft, business email compromise (BEC), and unrecoverable financial losses, requiring extensive remediation steps (credential resets, MFA re-registration, removal of inbox rules).
MITRE Techniques
- [T1566 ] Phishing – Threat actors use credential phishing emails and lures to obtain credentials and initial access. (‘Threat actor gains access to account through phishing’)
- [T1557 ] Adversary-in-the-Middle (AiTM) – Attackers use AiTM phishing flows provided by PhaaS platforms to bypass MFA and intercept credentials. (‘adversary-in-the-middle (AiTM) phishing, which is intended to circumvent multifactor authentication (MFA) protections’)
- [T1078 ] Valid Accounts – Compromised user accounts are used in follow-on activity and detected as recognized attack patterns. (‘Compromised user account in a recognized attack pattern’)
- [T1098 ] Account Manipulation – Post-compromise, attackers create or modify inbox rules to evade detection and exfiltrate data or hide activity. (‘Threat actor creates an inbox rule post compromise’)
Indicators of Compromise
- [IPv4 ] Initiation sources for spoofed phishing emails – 162.19.196[.]13, 51.89.59[.]188, and other IPs such as 163.5.221[.]110, 51.195.94[.]194 (and other actor IPs listed).
- [Domain ] PhaaS and redirector domains used in phishing chains – 2fa.valoufroo.in[.]net, valoufroo.in[.]net, and redirectors like integralsm[.]cl, absoluteprintgroup[.]com (and additional actor-controlled domains such as scanuae[.]com, online.amphen0l-fci[.]com).
- [Spoofed/Targeted Domains ] Example spoofing targets and examples used in headers – contoso.com (used in header examples showing SPF/DKIM/DMARC failures) and other customer accepted domains referenced in detection queries.
- [Attachment / Document Names ] Files used to support financial scams and social-engineering lures – fake invoice (attached with banking details), IRS W-9 form (fake), and a fake “bank letter” (used to add believability to invoice scams).