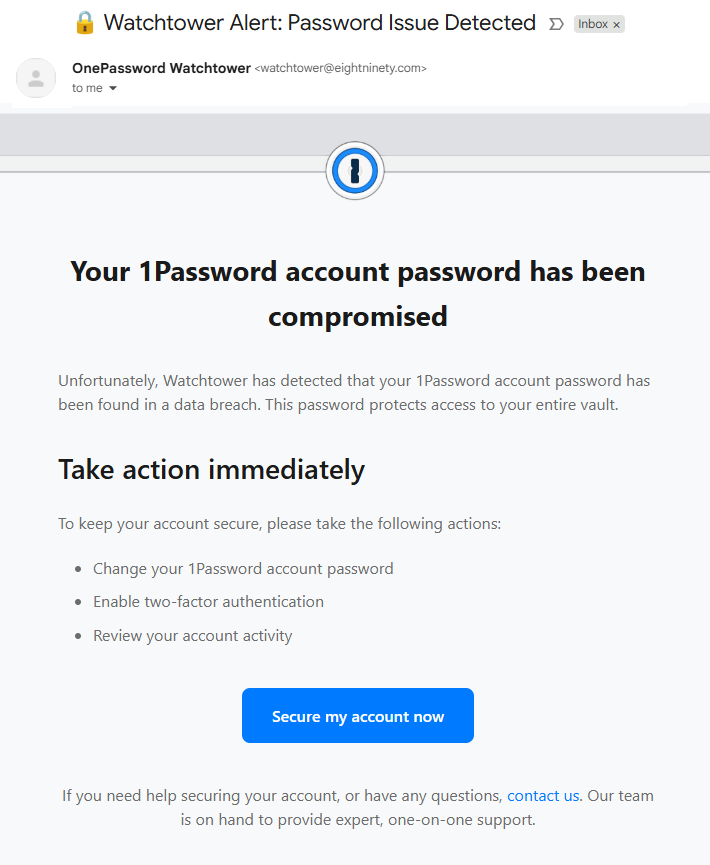
Scammers sent a targeted phishing email impersonating 1Password’s Watchtower to try to capture a Malwarebytes employee’s 1Password credentials, using a typosquatted domain and a Mandrillapp redirect. The campaign redirected victims to a phishing form on onepass-word[.]com via mandrillapp[.]com and used watchtower@eightninety[.]com as the sender. #onepass-word.com #[email protected]
Keypoints
- The phishing email impersonated 1Password’s Watchtower feature, urging the recipient to change their password and enable 2FA.
- The sender address used was watchtower@eightninety[.]com, which is not a legitimate 1Password domain.
- The “Secure my account now” button pointed to a Mandrillapp redirect that forwarded to a typosquatted domain onepass-word[.]com.
- Early clickers saw a phishing form that would capture 1Password credentials; later clicks produced a Mandrillapp “bad url” error after vendor classification.
- Mandrillapp (Mailchimp) was used as the transactional email redirect, though it does not forward to known phishing sites once classified.
- A similar phishing campaign was reported on September 25, 2025, suggesting this is part of repeated or ongoing attempts.
- Recommended defenses: do not click links in unsolicited emails, avoid providing 1Password credentials, check account status via official app/site, and use real-time web protection.
MITRE Techniques
- [T1566] Phishing – The attackers sent a targeted email impersonating 1Password Watchtower to trick the recipient into submitting credentials (“Your 1Password account has been compromised… Secure my account now”).
- [T1192] Spearphishing Link – The phishing message included a clickable button that directed via mandrillapp[.]com to a typosquatted domain onepass-word[.]com to capture vault credentials (“https://mandrillapp[.]com/track/click/…/onepass-word[.]com?p={long-identifier}”).
- [T1588.001] Establish Accounts: External Services – The campaign leveraged Mandrillapp (a Mailchimp transactional email service) to deliver and track phishing emails and redirects (“Mandrillapp is a transactional email API and delivery service provided by Mailchimp”).
Indicators of Compromise
- [Email address] phishing sender – watchtower@eightninety[.]com
- [Domain] typosquatted phishing site – onepass-word[.]com
- [Redirect service] email redirect/tracking – mandrillapp[.]com/track/click/… (used to forward clicks to the phishing domain)