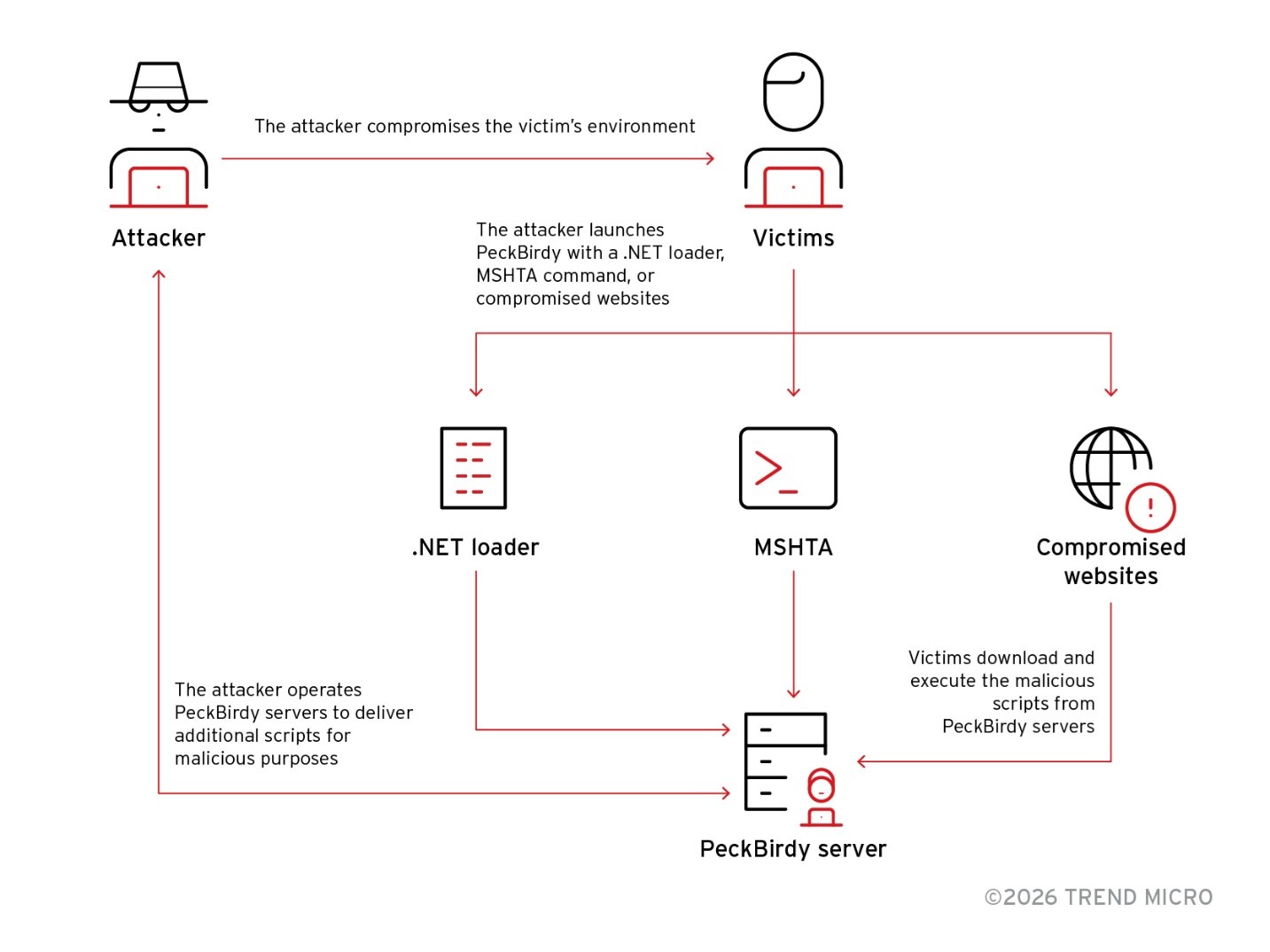
PeckBirdy is a versatile JScript-based command-and-control framework used by China-aligned APT groups since 2023 to abuse LOLBins and deliver modular backdoors across browsers, MSHTA, WScript, Classic ASP, NodeJS and .NET environments. Related campaigns SHADOW-VOID-044 and SHADOW-EARTH-045 deployed backdoors such as HOLODONUT and MKDOOR, used watering‑hole and phishing lures, exploited CVE-2020-16040, and reused infrastructure and stolen code-signing certificates. #PeckBirdy #HOLODONUT
Keypoints
- PeckBirdy is a JScript/ECMAScript-based C2 framework built for cross-environment execution via LOLBins (browsers, MSHTA, WScript, Classic ASP, NodeJS, .NET) enabling flexible deployment and multi-stage use.
- Attack campaigns SHADOW-VOID-044 and SHADOW-EARTH-045 used PeckBirdy in watering‑hole and credential-harvesting operations against Chinese gambling sites and Asian government/education targets.
- Modular backdoors HOLODONUT (.NET, NEXLOAD downloader, Donut in-memory execution) and MKDOOR (downloader + modular backdoor, Microsoft-themed URLs, Defender exclusion) extend PeckBirdy’s capabilities.
- Operators used multiple C2 delivery methods (WebSocket, Flash ActiveX/TCP, Comet/HTTP/AJAX) and AES+Base64 encrypted communications with ATTACK_ID as the AES key.
- Observed techniques include exploitation of CVE-2020-16040, DLL sideloading for GRAYRABBIT, stolen code-signing certificates for signing payloads, and reuse of infrastructure across related APTs.
- TrendAI Vision One™ detects and blocks documented IOCs and provides hunting queries and intelligence for customers to identify and mitigate these campaigns.
MITRE Techniques
- [T1218] Signed Binary Proxy Execution (LOLBins) – PeckBirdy is launched via living-off-the-land binaries such as MSHTA and WScript to execute scripts across environments (‘PeckBirdy can be executed in various environments, including browsers, MSHTA, WScript, Classic ASP, Node JS, and .NET (ScriptControl).’)
- [T1071.001] Application Layer Protocol: Web Protocols – C2 communication used WebSocket and fallback HTTP(S)/AJAX-based Comet methods for broad compatibility (‘the default method uses the WebSocket protocol… If neither of these methods are supported, PeckBirdy can use the Comet and LocalComet methods, which are based on HTTP(S) and AJAX protocols.’)
- [T1203] Exploitation for Client Execution – Actors deployed an exploitation script targeting CVE-2020-16040 in Chrome to achieve code execution (‘The scripts we found included: The exploitation script for the CVE-2020-16040 vulnerability affecting Google Chrome’)
- [T1189] Drive-by Compromise (Watering‑hole) – Malicious scripts were injected into gambling and government websites to deliver PeckBirdy landing scripts to site visitors (‘we noticed multiple Chinese gambling websites being injected with malicious scripts with links to remote servers.’)
- [T1105] Ingress Tool Transfer – Downloaders (NEXLOAD, MKDOOR downloader) retrieved backdoors and modules from remote C2 servers (‘the threat actors deployed a customized simple downloader… tracked as NEXLOAD… the downloader will connect to the C&C server and download the backdoor module.’)
- [T1562.001] Impair Defenses: Disable or Modify Tools – Backdoors attempted to disable AMSI and ETW to evade detection (‘the payload uses multiple techniques, including disabling AMSI and EtwEvent’).
- [T1539] Steal Web Session Cookie – A delivered script specifically stole cookie values from injected websites in browser contexts (‘The only one we received was a short script for stealing the cookie values of injected websites on browsers.’)
- [T1553.002] Subvert Trust Controls: Code Signing – Operators used a stolen code-signing certificate to sign a Cobalt Strike sample observed on C2 infrastructure (‘this sample was signed using a certificate (thumbprint, SHA1: bbd2b9b87f968ed88210d4261a1fe30711e8365b) stolen from a South Korean gaming company.’)
- [T1574] Hijack Execution Flow (DLL sideloading) – GRAYRABBIT variants used DLL sideloading combined with PowerShell functions to load and execute backdoor payloads (‘the GRAYRABBIT sample we observed was slightly different, using a DLL sideloading technique combined with the UuidFromStringA function of PowerShell to read, decode, and execute the backdoor payload.’)
- [T1055] Process Injection – Use of Donut to execute .NET assemblies in memory reduced visibility and avoided on-disk artifacts (‘the payload … the use of Donut, an open-source tool used to stealthily execute .NET assemblies. As a result, HOLODONUT can be executed in process memory with less visibility.’)
Indicators of Compromise
- [IP address ] C2 and infrastructure – 47[.]238[.]219[.]111, 47[.]238[.]184[.]9
- [Domain ] C2 and hosting domains observed – center[.]myrnicrosoft[.]com, mkdmcdn[.]com
- [File hash ] signed malware sample – SHA256: 162cc325ab7b6e70edb6f4d0bc0e52130c56903f (Cobalt Strike sample)
- [Certificate thumbprint ] stolen code-signing certificate – SHA1: bbd2b9b87f968ed88210d4261a1fe30711e8365b (used to sign observed sample)
- [File name ] local persistence/identifier artifacts – ___unique_id___ (temporary file used to store victim ID)
- [URL path ] masqueraded C2 paths used by MKDOOR and lures – /en-us/howtotell/default[.]aspx, /en-us/windows/activate-windows-c39005d4-95ee-b91e-b399-2820fda32227
Read more: https://www.trendmicro.com/en_us/research/26/a/peckbirdy-script-framework.html