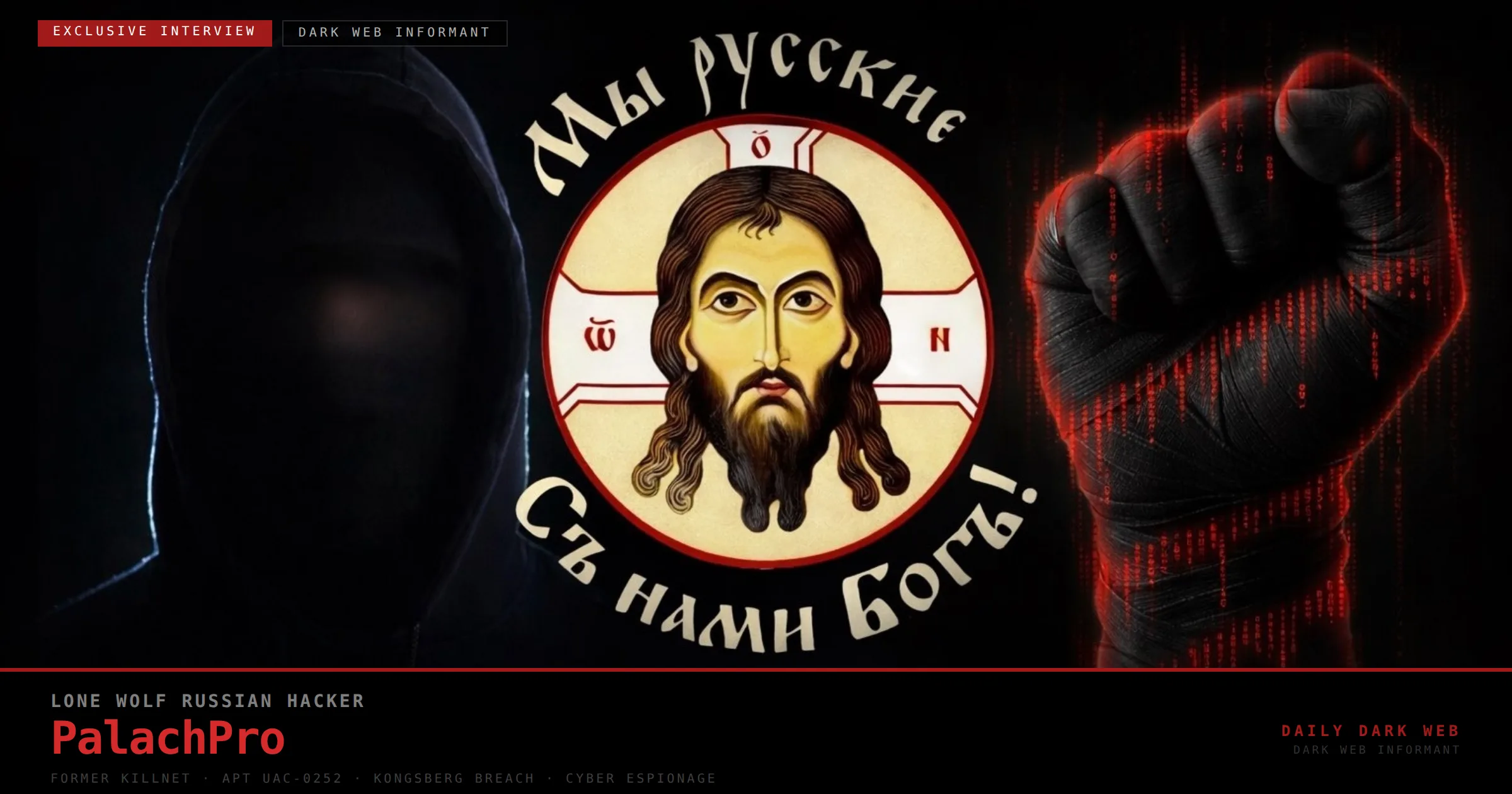
PalachPro is a solo Russian hacker with APT-level capabilities who exfiltrated classified Kongsberg documents and conducted espionage, DDoS, and tracking operations against Ukrainian military, NATO-aligned contractors, and Western infrastructure. His tools (SHADOWSNIFF, SALATSTEALER) and UAC-0252 designation have been documented by multiple intelligence firms, and data from his breaches was allegedly used to support an August 2025 Iskander strike on a Chernihiv training base. #PalachPro #NASAMS
Keypoints
- PalachPro operates solo and has demonstrated APT-level capabilities targeting military and defense sectors.
- In January 2025 he breached Kongsberg Defence & Aerospace and exfiltrated classified NASAMS-related documents tied to a $3B arms deal.
- Data from the Kongsberg breach allegedly aided an August 2025 Iskander strike on a Chernihiv training base that killed more than 50 people.
- His activity is designated UAC-0252 and documented by CERT-UA, Google Threat Intelligence, SOC Prime, Acumen Cyber, and Recorded Future.
- He employs custom tools (SHADOWSNIFF, SALATSTEALER), supply-chain and persistence tactics, and has claimed informal coordination with groups like NoName057(16).
Read More: https://dailydarkweb.net/palachpro-exclusive-interview-lone-wolf-russian-hacker/