This article discusses the latest updates to OtterCookie, a malware used by the North Korea-linked WaterPlum group in cyber-espionage campaigns. It highlights the new functionalities introduced in versions 3 and 4, and their evolving attack capabilities.
Affected: Financial institutions, cryptocurrency operators, FinTech companies.
Affected: Financial institutions, cryptocurrency operators, FinTech companies.
Keypoints
- WaterPlum is a North Korea-linked hacking group targeting financial and FinTech sectors worldwide.
- The group has been using malware called BeaverTail, InvisibleFerret, and now OtterCookie since 2023, with active updates continuing into 2025.
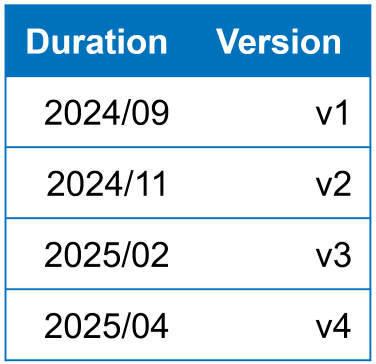
- OtterCookie has evolved through multiple versions, from v1 with basic file grabbing to v4 with advanced modules and new functionalities.
- Version 3 added support for Windows environment file collection and remote communication with command-and-control (C2) servers.
- Version 4 introduced new stealer modules capable of extracting browser credentials, passwords, and files on Windows and MacOS, with environment detection features.
- The malware targets specific file types, including documents, images, and cryptocurrency-related data, and employs encryption and different data handling methods.
- Active monitoring and analysis of OtterCookie are crucial as WaterPlum continues to update and deploy this malware in ongoing cyber campaigns.
Read More: https://jp.security.ntt/tech_blog/en-waterplum-ottercookie