This article explores the differences in OAuth 2.0 device code flow implementations between Microsoft and Google, emphasizing their impact on attack surfaces. It demonstrates how device code phishing can be powerful in Azure due to fewer restrictions, while Google’s limited scopes mitigate similar risks. #Microsoft #Azure #Google #OAuth2Flow
Keypoints
- The device code flow in OAuth 2.0 is designed for input-constrained devices like smart TVs and IoT devices.
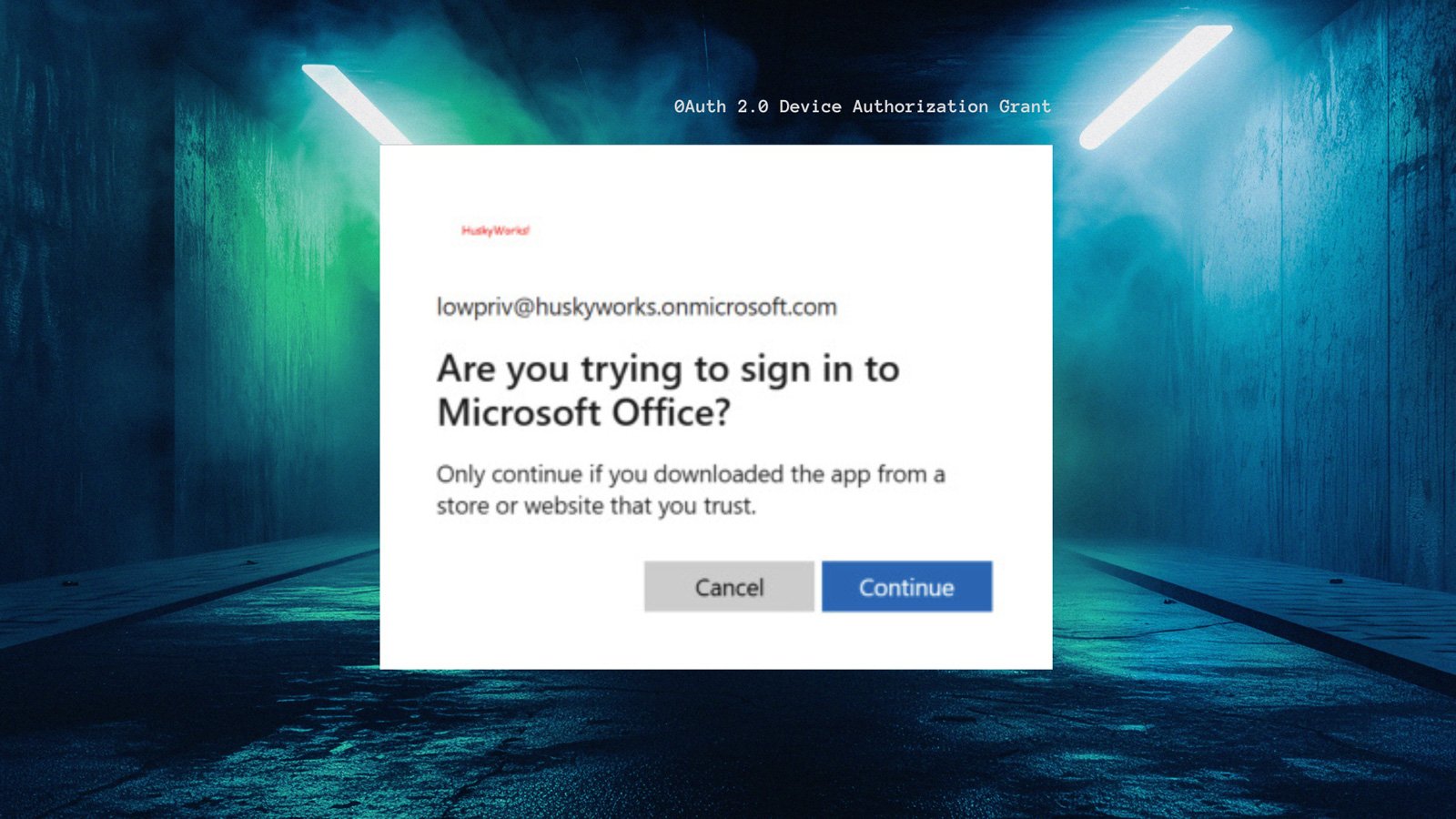
- Attacker can exploit the device code flow via phishing to obtain access tokens in Azure, leading to severe security risks.
- Azure’s implementation allows broad resource and scope control, enabling powerful attack primitives like token theft and device joining.
- Google restricts the device code flow to limited scopes, reducing the potential impact of similar phishing attacks.
- The differences highlight how variations in OAuth implementations can significantly alter attack surfaces in identity providers.
Read More: https://www.bleepingcomputer.com/news/security/oauth-device-code-phishing-azure-vs-google-compared/