March 2026 saw diverse, fast-moving campaigns that exploited trusted workflows—OAuth Device Code phishing, macOS ClickFix delivering AMOS Stealer and backdoors, registry-hidden DLL staging leading to OrcusRAT, Magecart payment skimming, SVG smuggling, and multi-vector DDoS botnets—making early detection and triage harder and increasing business impact. ANY.RUN analysts produced sandbox-backed breakdowns, IOCs, and TI queries to help defenders hunt, validate detections, and respond faster. #EvilTokens #AMOSStealer
Keypoints
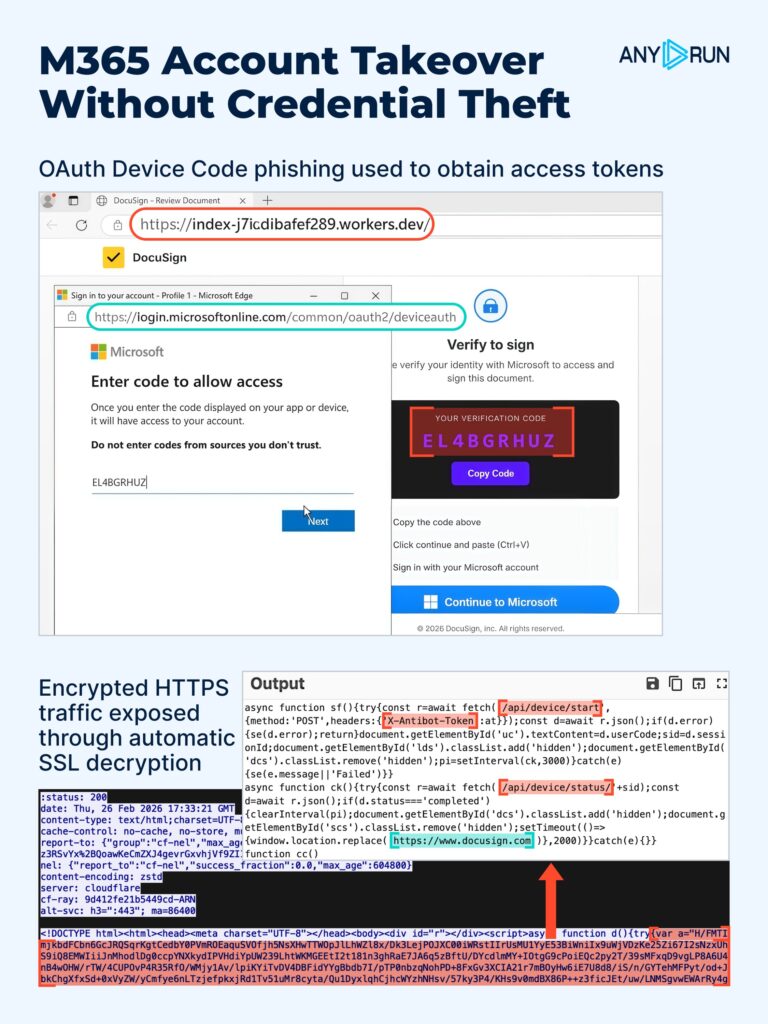
- EvilTokens leveraged Microsoft’s OAuth Device Code flow so attackers obtain OAuth tokens without stealing credentials, hiding compromises in legitimate sign-in activity.
- A macOS ClickFix campaign delivered AMOS Stealer and an updated ~/.mainhelper backdoor that provides an interactive reverse shell over WebSocket, enabling persistent hands-on access.
- RUTSSTAGER hides a DLL in the Windows registry (hex-encoded) to deploy OrcusRAT and a persistence/relaunch component, avoiding obvious on-disk artifacts.
- Phishing attachments like pdf.htm and SVG smuggling lures rebuild subsequent stages locally (blob URLs, password-protected ZIPs), reducing early network signals and slowing triage.
- A long-running Magecart skimmer campaign hijacked checkout flows (WebSocket exfiltration, staged domains, Redsys-themed contexts) and maintained over 100 domains and fallbacks to persist for 24+ months.
- Kamasers is a resilient multi-vector DDoS botnet with Dead Drop Resolver design using public services (GitHub Gist, Telegram, Dropbox, Bitbucket, Etherscan) to retrieve C2, and it can also act as a loader for follow-on payloads.
MITRE Techniques
- No MITRE ATT&CK technique IDs are explicitly named in the article; behaviors described include token abuse/valid account misuse, registry-based payload storage, credential harvesting via phishing attachments, stealer data exfiltration, and use of public services for C2 resolution.
Indicators of Compromise
- [Domains ] EvilTokens phishing infrastructure – singer-bodners-bau-at-s-account[.]workers[.]dev, dibafef289[.]workers[.]dev, and 4 more workers[.]dev domains
- [File Hashes ] RUTSSTAGER / registry-stored DLL artifacts – 57ce6187be65c1c692a309c08457290ae74a0047304de6805dbb4feb89c0d7e5, 6a581c3b6fe7847bb327f5d76e05653a1504e51023454c41835e5dc48bc13ba4, and 3 more hashes
- [File / Path Names ] macOS and phishing artifacts – pdf.htm, ~/.mainhelper (updated backdoor module), radicado.hta
- [HTTP Paths / Headers ] OAuth phishing HTTP artifacts observed in sandbox – /api/device/start, /api/device/status/*, X-Antibot-Token header
- [C2 Commands / Signals ] Vjw0rm / C2 detection commands (useful as hunting indicators) – Cl (execution termination), AW (active window data collection), Ex (PowerShell execution), and others: SF/RF, DL, DLF, Un
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/major-cyber-attacks-march-2026/