Google’s M-Trends 2026, based on Mandiant’s 500,000+ hours of incident investigations, reports that the time from initial access to handoff to secondary groups has collapsed from hours to a median of 22 seconds in 2025, often driven by automated access brokers. The report also highlights exploits as the top initial vector (notably CVE-2025-31324, CVE-2025-61882, and CVE-2025-53770), growing Linux and macOS-targeting malware families, and the prominence of GoldVein and Cl0p activity. #GoldVein #Cl0p
Keypoints
- The median time from initial access to handoff to a secondary group fell to 22 seconds in 2025.
- Exploits were the most common initial vector (32%), led by CVE-2025-31324, CVE-2025-61882, and CVE-2025-53770.
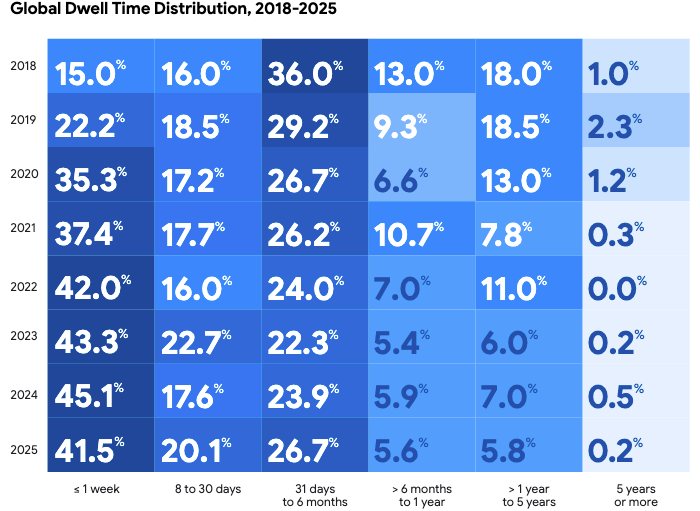
- Median dwell time rose slightly to 14 days in 2025, with more incidents remaining undetected for 1–6 months.
- Google identified 714 new malware families in 2025, with GoldVein being the most frequently observed family.
- Cloud compromises were often initiated by voice phishing, driven by actors such as ShinyHunters and Scattered Spider.
Read More: https://www.securityweek.com/m-trends-2026-initial-access-handoff-shrinks-from-hours-to-22-seconds/