Lumma Stealer resurfaced in 2025 with new variants employing heavy obfuscation, AutoIt-based loaders, anti-analysis checks, DLL unhooking, and persistence via Startup shortcuts; Netskope detected a specific NSIS-signed sample (hash 87118baadfa7075d7b9d2aff75d8e730) using a transformer-based ML model on runtime process trees and behavioral features. #LummaStealer #AutoIt
Keypoints
- Lumma Stealer saw global use across multiple industries in early 2025 and re-emerged with new variants after a brief law-enforcement disruption.
- Netskope analyzed sample 87118baadfa7075d7b9d2aff75d8e730, an NSIS installer that unpacks an obfuscated NSIS script and AutoIt-based payload stages.
- Malware employs strong obfuscation (NSIS, Base blobs, obfuscated AutoIt scripts) and runtime decompression (RtlDecompressFragmentWindows) to load a PE in memory.
- Evasion techniques include environment checks (COMPUTERNAME/USERNAME, presence of VM/analysis processes), anti-debug timing checks, fake-domain ping checks, and DLL unhooking to bypass security hooks.
- Persistence is achieved by creating a .url shortcut in the Windows Startup folder that launches JScript to invoke the AutoIt payload via Wscript.Shell.
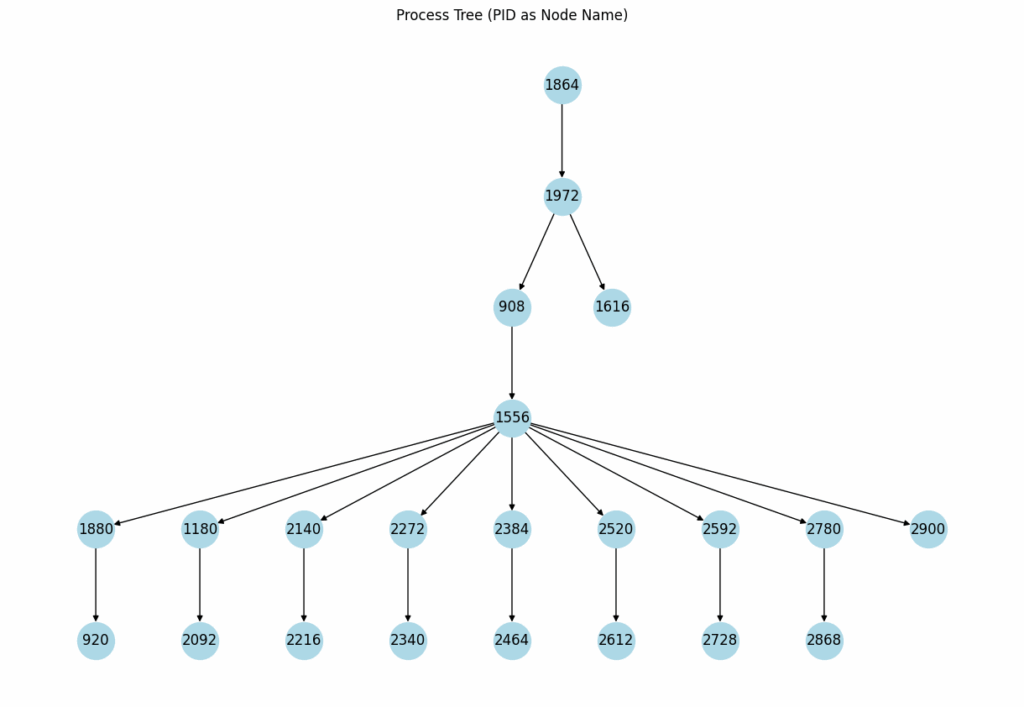
- Netskope’s Cloud Sandbox uses process-tree embeddings and runtime feature vectors in a transformer-based ML model to detect previously unseen variants; it flagged this sample (detection Gen.Detect.By.NSCloudSandbox.tr).
- IOCs provided include the sample hash, additional hashes, and multiple domains associated with C2 or staged payloads.
MITRE Techniques
- [T1027] Obfuscated Files or Information – Malware used NSIS installer and obfuscated AutoIt scripts to conceal functionality and payloads. Quote: ‘Obfuscated NSIS script, will invoke Parish.m4a to initiate the chain’.
- [T1059] Command and Scripting Interpreter – AutoIt and Windows batch/JScript were used to execute and chain payloads. Quote: ‘the sample leverages AutoIt for illicit purposes’ and ‘this shortcut launches a JScript, which then uses an ActiveXObject to instantiate a Wscript.Shell object’.
- [T1204] User Execution – Infection chains relied on user actions to run the NSIS installer and extracted payloads. Quote: ‘many infection chains rely on users opening malicious attachments or clicking on suspicious links’.
- [T1497] Virtualization/Sandbox Evasion – The sample checks for VM/process indicators (vmtoolsd.exe, VboxTray.exe, SandboxieRpcSs.exe) to detect analysis environments. Quote: ‘Ensure the following process is not present: vmtoolsd.exe VboxTray.exe SandboxieRpcSs.exe’.
- [T1620] Reflective Code Loading / In-memory Execution – The malware decompresses and executes a PE from memory using RtlDecompressFragmentWindows to avoid writing the PE to disk. Quote: ‘the decompression process unveils a portable executable (PE) file within memory’.
- [T1547] Boot or Logon Autostart Execution – Persistence via creating a .url file in the Windows Startup folder to launch JScript that executes the payload at user logon. Quote: ‘creates an internet shortcut (.url) in the Windows Startup folder, thereby establishing persistence’.
- [T1499] Impair Defenses (DLL Unhooking) – Malware restores original function bytes to counter security product API hooks. Quote: ‘Malware can bypass this by restoring the original, unhooked function bytes, thereby nullifying the security control’.
- [T1112] Modify Registry – Runtime behavioral features included registry modifications recorded by the sandbox. Quote: ‘Runtime behavioral features, such as registry modifications, file operations, and network communications, are also encoded’.
Indicators of Compromise
- [File hash] analyzed sample and additional hashes – 87118baadfa7075d7b9d2aff75d8e730 (NSIS sample), and 2 more hashes: 78da004e332be8eaa5e111c34d6db3a28abb9767, ff7a1388fa59a9e1b43c5c88a1ee30e4abcec21a39882812a045aa9d9b865170.
- [Domains] potential C2/staging domains – annwt[.]xyz, ungryo[.]shop, and additional domains: vervzv[.]xyz, sorrij[.]top, prvqhm[.]shop, bardj[.]xyz, greqjfu[.]xyz.
- [File names/artefacts] unpacked files and loader components – Parish.m4a (obfuscated batch), *.m4a blobs, and a renamed AutoIt executable (Autoit3.exe / u.a3x) used to execute the AutoIt script.
Read more: https://www.netskope.com/blog/beyond-signatures-detecting-lumma-stealer-with-an-ml-powered-sandbox