Keypoints
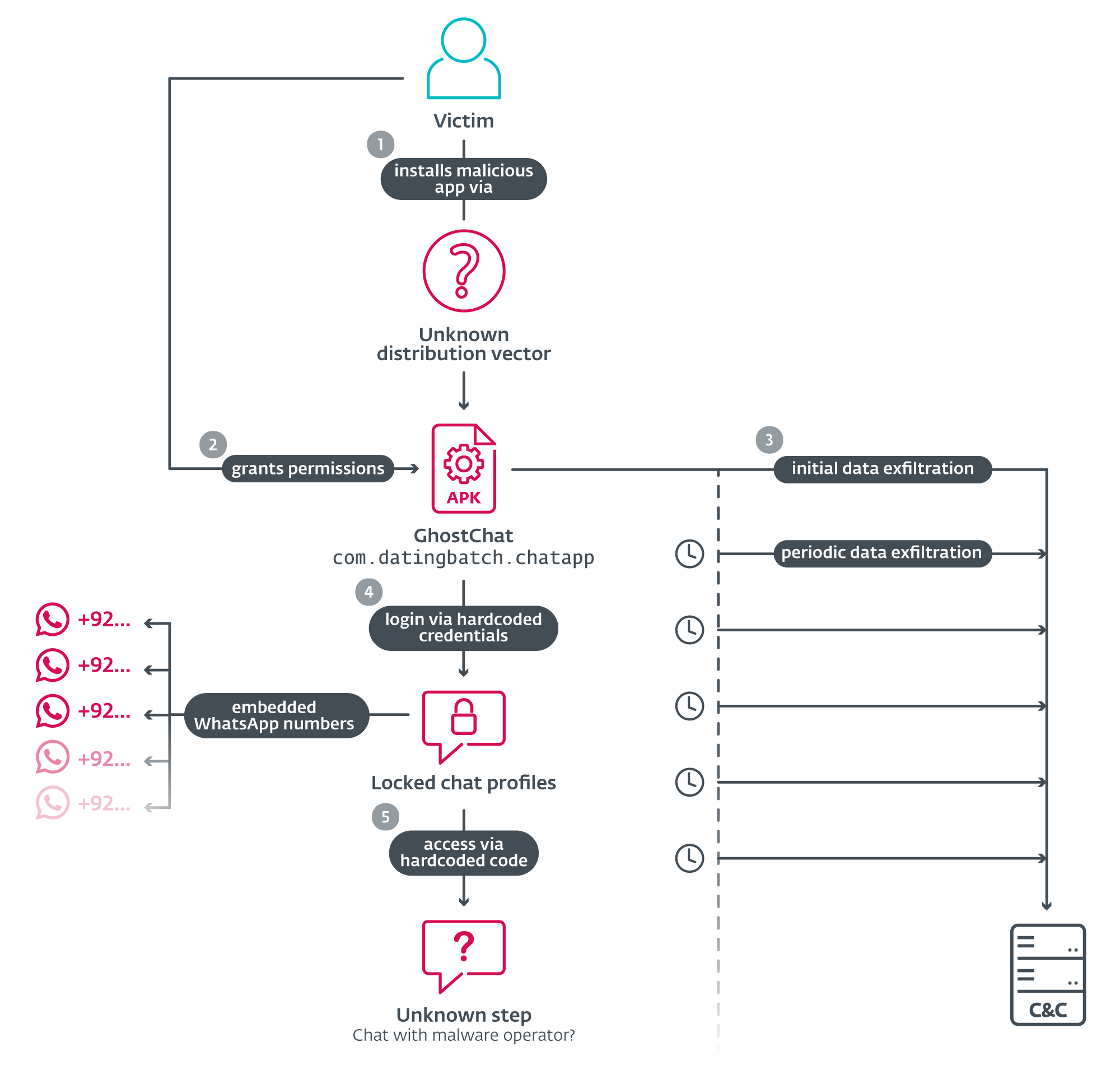
- ESET discovered GhostChat, an Android spyware app disguised as a dating/chat platform that targets individuals in Pakistan using romance-scam lures and “locked” profiles with hardcoded unlock codes.
- GhostChat requires sideloading (never on Google Play) and requests permissions to run background services, then exfiltrates device ID, contacts, and files upon first run and continuously (images uploaded as created; documents scanned every five minutes).
- Each fake profile maps to a hardcoded Pakistani WhatsApp number; entering a code redirects victims to WhatsApp to contact numbers likely controlled by the operator, reinforcing the social-engineering lure.
- Related infrastructure includes batch scripts and a Windows DLL communicating with the same C&C (hitpak[.]org); the ClickFix social-engineering lure impersonated PKCERT to trick users into executing a DLL payload.
- The Windows DLL communicates with the C&C and polls every five minutes for base64-encoded PowerShell commands, enabling remote code execution and ongoing control.
- A mobile WhatsApp-linking technique (GhostPairing) used a fake Pakistan Ministry of Defence site to present a QR code that, when scanned, links victims’ WhatsApp accounts to the attacker’s device.
MITRE Techniques
- [T1398 ] Boot or Logon Initialization Scripts – GhostChat activates at device startup by receiving the BOOT_COMPLETED broadcast intent. (‘GhostChat receives the BOOT_COMPLETED broadcast intent to activate at device startup.’)
- [T1541 ] Foreground Persistence – GhostChat uses foreground persistence to keep a service running and maintain surveillance. (‘GhostChat uses foreground persistence to keep a service running.’)
- [T1426 ] System Information Discovery – GhostChat extracts device identifiers such as the device ID for profiling. (‘GhostChat can extract the device ID.’)
- [T1533 ] Data from Local System – GhostChat collects and exfiltrates files and other local data from the device. (‘GhostChat can exfiltrate files from a device.’)
- [T1636.003 ] Protected User Data: Contact List – GhostChat extracts the device’s contact list and uploads it to the C&C. (‘GhostChat can extract the device’s contact list.’)
- [T1437.001 ] Application Layer Protocol: Web Protocols – GhostChat communicates with its C&C over HTTPS to send harvested data. (‘GhostChat can communicate with the C&C using HTTPS requests.’)
- [T1646 ] Exfiltration Over C2 Channel – GhostChat exfiltrates harvested data to the operator via the C&C channel (HTTPS). (‘GhostChat exfiltrates data using HTTPS.’)
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – The Windows DLL executes base64-encoded PowerShell commands delivered by the C&C, enabling remote code execution. (‘Windows agent can execute PowerShell commands received from the C&C server.’)
- [T1082 ] System Information Discovery – The Windows agent collects the computer name as part of its initial handshake with the C&C. (‘Windows agent collects the computer name.’)
- [T1033 ] System Owner/User Discovery – The Windows agent collects the username for identification when contacting the C&C. (‘Windows agent collects the username.’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – The Windows agent uses HTTPS requests to communicate with its C&C server. (‘Windows agent can communicate with the C&C using HTTPS requests.’)
- [T1132.001 ] Data Encoding: Standard Encoding – The Windows agent receives base64-encoded PowerShell payloads from the C&C which it decodes and executes. (‘Windows agent receives base64 encoded PowerShell commands to execute.’)
Indicators of Compromise
- [File Hash ] GhostChat and Windows payload samples – B15B1F3F2227EBA4B69C85BDB638DF34B9D30B6A (Live Chat.apk), 8B103D0AA37E5297143E21949471FD4F6B2ECBAA (file.dll)
- [File Name ] Malware and payload filenames observed – Live Chat.apk (Android/Spy.GhostChat.A), file.dll (Win64/Agent.HEM)
- [Domain ] Distribution and C&C or lure sites – hitpak[.]org (distribution & C&C), buildthenations[.]info (fake PKCERT/Ministry of Defence lure), and 1 more domain (foxy580.github[.]io)
- [IP ] Hosting IP for C&C – 188.114.96[.]10 (Cloudflare-hosted C&C observed on 2024-12-16)
- [URL ] Downloader and payload URLs used in related activity – https://hitpak[.]org/notepad2.dll (DLL delivery), https://foxy580.github[.]io/koko/file.dll (ClickFix DLL payload)