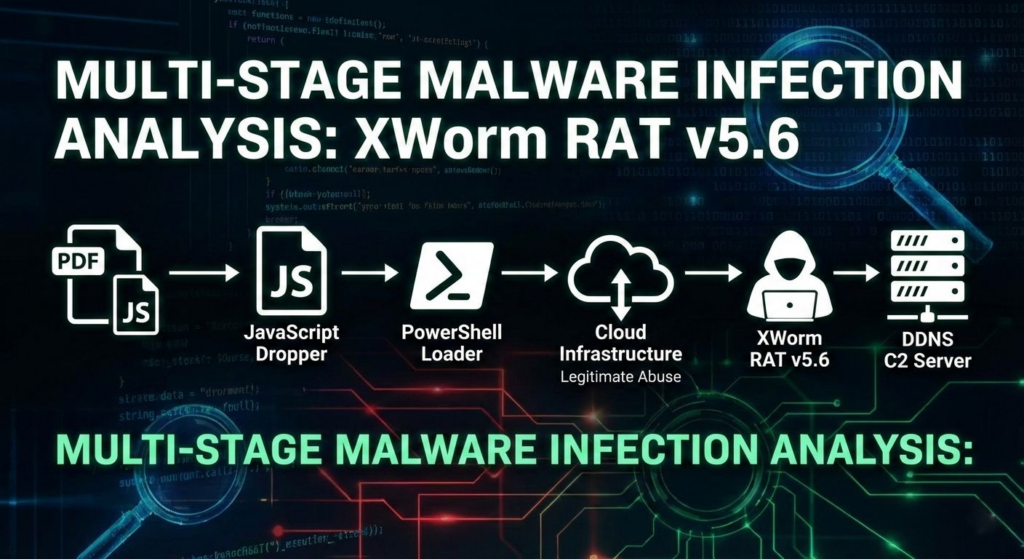
A multi-stage campaign targeting Brazilian users delivers XWorm via a deceptive “banking receipt” WSH dropper that uses obfuscated JavaScript, WMI-spawned PowerShell, Cloudinary-hosted steganography, and in-memory .NET loading to minimize early detection. The infection establishes persistence by registering a Scheduled Task via .NET APIs and injects the XWorm payload into CasPol.exe, enabling stealthy C2 communications to 152[.]249[.]17[.]145 on port 7000. #XWorm #CasPol
Keypoints
- The initial lure is a tampered “Comprovante-Bradesco… .pdf.js” WSH dropper that inflates file size and uses Unicode junk/emoji obfuscation to evade static scanners.
- The dropper reconstructs and launches a PowerShell loader via WMI (hidden window and sleep delays) to reduce sandbox and user visibility.
- Stage 2 abuses Cloudinary-hosted images containing steganographic Base64 blobs; the embedded .NET assembly is extracted and loaded directly into memory ([Reflection.Assembly]::Load).
- Stage 3 is a dedicated VB.NET persistence DLL that registers a Scheduled Task via .NET COM Task Scheduler APIs (avoiding schtasks.exe) to re-run the PowerShell loader at logon.
- The final Stage 4 XWorm binary is retrieved as reversed Base64 from voulerlivros[.]com[.]br, decrypted using a weak AES-ECB/MD5 scheme, and injected into CasPol.exe for execution and C2 connectivity.
- Confirmed runtime indicators include mutex V2r1vDNFXE1YLWoA, C2 jholycf100.ddns.com.br (152.249.17.145) on port 7000, and network streams containing the protocol delimiter.
MITRE Techniques
- [T1047 ] Windows Management Instrumentation – Used to spawn a hidden PowerShell process via WMI to execute the loader and avoid visible shells (‘it leverages WMI (Windows Management Instrumentation) via GetObject(“winmgmts:rootcimv2”) and Win32_Process.’)
- [T1059.001 ] PowerShell – PowerShell is constructed and executed as the main downloader/bridge that fetches the stego image and loads the in-memory assembly (‘the deobfuscated payload constructs a PowerShell command responsible for downloading the next stage.’)
- [T1027.005 ] Steganography (Obfuscated Files or Information) – The loader extracts a Base64-encoded .NET assembly hidden inside a JPEG hosted on Cloudinary between “BaseStart” and “BaseEnd” markers (‘The downloaded file (optimized_MSI_lpsd9p.jpg) carries a hidden payload… The data between these markers is a Base64-encoded .NET assembly (Stage 3).’)
- [T1620 ] Reflective Code Load – The Stage 3 .NET assembly is loaded directly into memory using reflection to avoid disk writes (‘the script extracts this blob and loads it directly into memory using [Reflection.Assembly]::Load().’)
- [T1053.005 ] Scheduled Task/Job – Persistence is achieved by registering a Scheduled Task via .NET Task Scheduler COM interfaces to re-run the PowerShell loader at logon (‘the payload… register[s] a Scheduled Task’ and ‘the created task ensures the PowerShell loader runs at logon’).
- [T1218 ] Living off the Land Binaries (LOLBIN) – The campaign abuses the legitimate CasPol.exe binary to host and run the XWorm payload, blending activity with trusted system tooling (‘it injects itself into CasPol.exe… the legitimate CasPol.exe binary is hollowed out to host the malicious payload’).
- [T1055 ] Process Injection – The XWorm payload is injected/hollowed into CasPol.exe to execute under a legitimate process context (‘the legitimate CasPol.exe binary is hollowed out to host the malicious payload’).
Indicators of Compromise
- [IP Address ] C2 server – 152[.]249[.]17[.]145
- [Domain / URL ] payload and C2 infrastructure – voulerlivros[.]com[.]br/arquivo_20260116064120.txt, res[.]cloudinary[.]com/…/optimized_MSI_lpsd9p.jpg
- [Port ] C2 communication port – 7000
- [File hash ] XWorm payload hash – 7befeacf0b3480fb675d0cab7767b5b9697edc9d0e05982025a06ead0054afd5
- [File path ] install directory / drop location – C:UsersPublicDownloads
- [Process name ] targeted/host process – CasPol.exe
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/xworm-latam-campaign/