Kyber is a cross-platform ransomware family that targets VMware ESXi datastores and Windows file systems with coordinated Tor-based infrastructure, campaign identifiers, and destructive anti-recovery features. The ESXi variant (C++ ELF) actually uses ChaCha8 with RSA-4096 and partial in-place encryption while the Windows variant (Rust PE) implements the advertised hybrid Kyber1024 scheme and includes elevated service termination and experimental Hyper-V shutdown. #Kyber #VMwareESXi
Keypoints
- Kyber deploys dual-platform ransomware that targets VMware ESXi datastores and Windows file systems.
- Both variants share a campaign ID and Tor-based infrastructure, indicating coordinated operations across platforms.
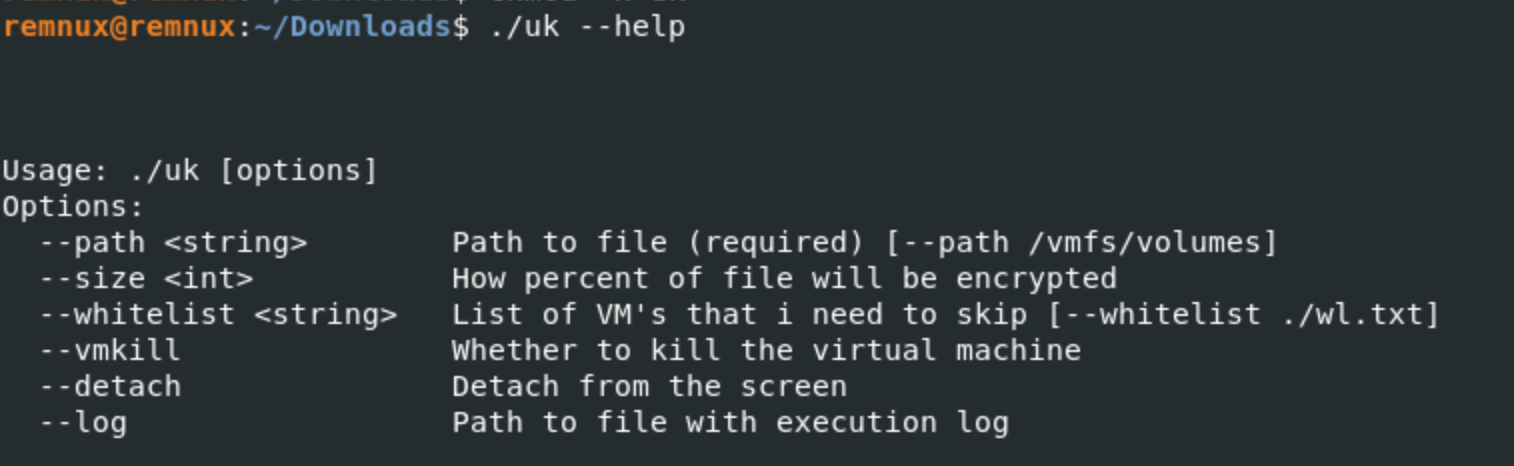
- The ESXi ELF (C++) uses ChaCha8 with RSA-4096, performs partial in-place encryption of datastores, and can terminate VMs via esxcli.
- The Windows PE (Rust) implements the advertised hybrid crypto (including Kyber1024), runs anti-recovery commands when elevated, and has an experimental Hyper-V shutdown feature.
- Both variants deface management interfaces and use partial-file encryption to speed operations while rendering large files unusable.
Read More: https://www.rapid7.com/blog/post/tr-kyber-ransomware-double-trouble-windows-esxi-attacks-explained/