Summary: The ChoiceJacking techniques exploit vulnerabilities in Android and Apple devices, allowing a malicious charger to impersonate user input and gain unauthorized file access. These attacks bypass existing juice-jacking mitigations, establishing input and file access connections to the targeted phone. All but one tested phone model can be compromised, granting attackers prolonged access to files while connected to the charger.
Affected: Android and Apple devices
Keypoints :
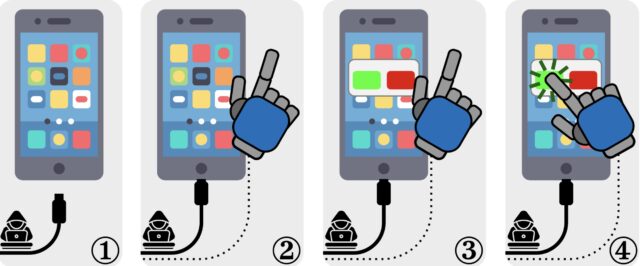
- ChoiceJacking techniques defeat existing juice-jacking protections by allowing chargers to act as USB hosts.
- The charger can autonomously inject input and spoof user consent to gain access to the device.
- One variant utilizes Bluetooth connections and USB Power Delivery to enhance the attack, impacting multiple phone models.