Researchers analyzing Hudson Rock cybercrime telemetry found a suspected DPRK IT worker’s machine infected with the LummaC2 infostealer, and its exfiltrated logs revealed an undocumented Indonesian proxy node tied to a broad “Vueyi” fraud operation. The case exposed synthetic identities, deepfake tooling, CDN infrastructure laundering via Funnull, large-scale crypto scams, and a catastrophic OPSEC failure when a local facilitator downloaded game hacks that delivered the infostealer. #LummaC2 #DPRK
Keypoints
- LummaC2 infection revealed an Indonesian proxy node and corporate CDN credentials linked to DPRK operators.
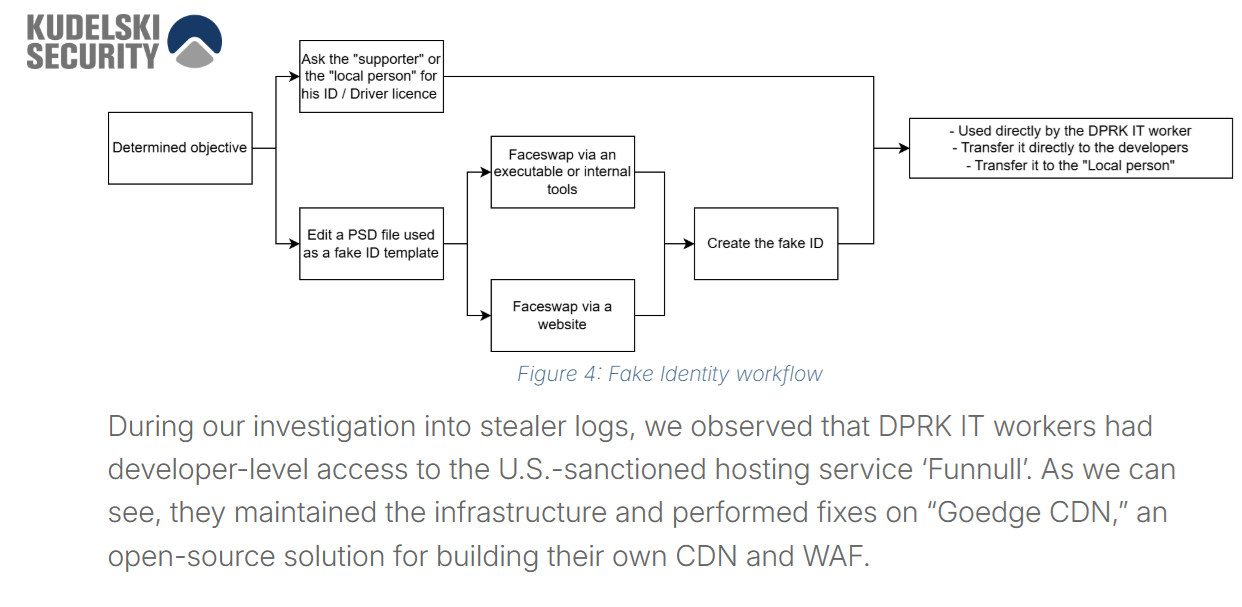
- Operators used synthetic identities, OBS/VirtualCam deepfakes, and localized personas to pass interviews and season IPs.
- Funnull and similar CDNs were abused for infrastructure laundering to mask the origin of malicious servers.
- Exfiltrated logs show industrial-scale scams including exchange cloning, smart-contract drainers, task scams, and segregated crypto wallets.
- A local facilitator downloading GTA V cheats from MediaFire likely triggered the infostealer infection, causing the OPSEC collapse.