Summary: Hunt’s ongoing scanning of the public IPV4 space has uncovered a significant repository of malicious files, including two SuperShell payloads and a Cobalt Strike beacon, originating from an exposed server. This discovery highlights the proactive measures necessary for detecting hidden threats and understanding malicious infrastructures. The investigation emphasizes the importance of open directories in revealing potentially dangerous tools for cybercriminals.
Affected: Hunt platform, Cybersecurity Infrastructure
Keypoints :
- Hunt’s scanning identifies over 41 million files, revealing often-overlooked web areas.
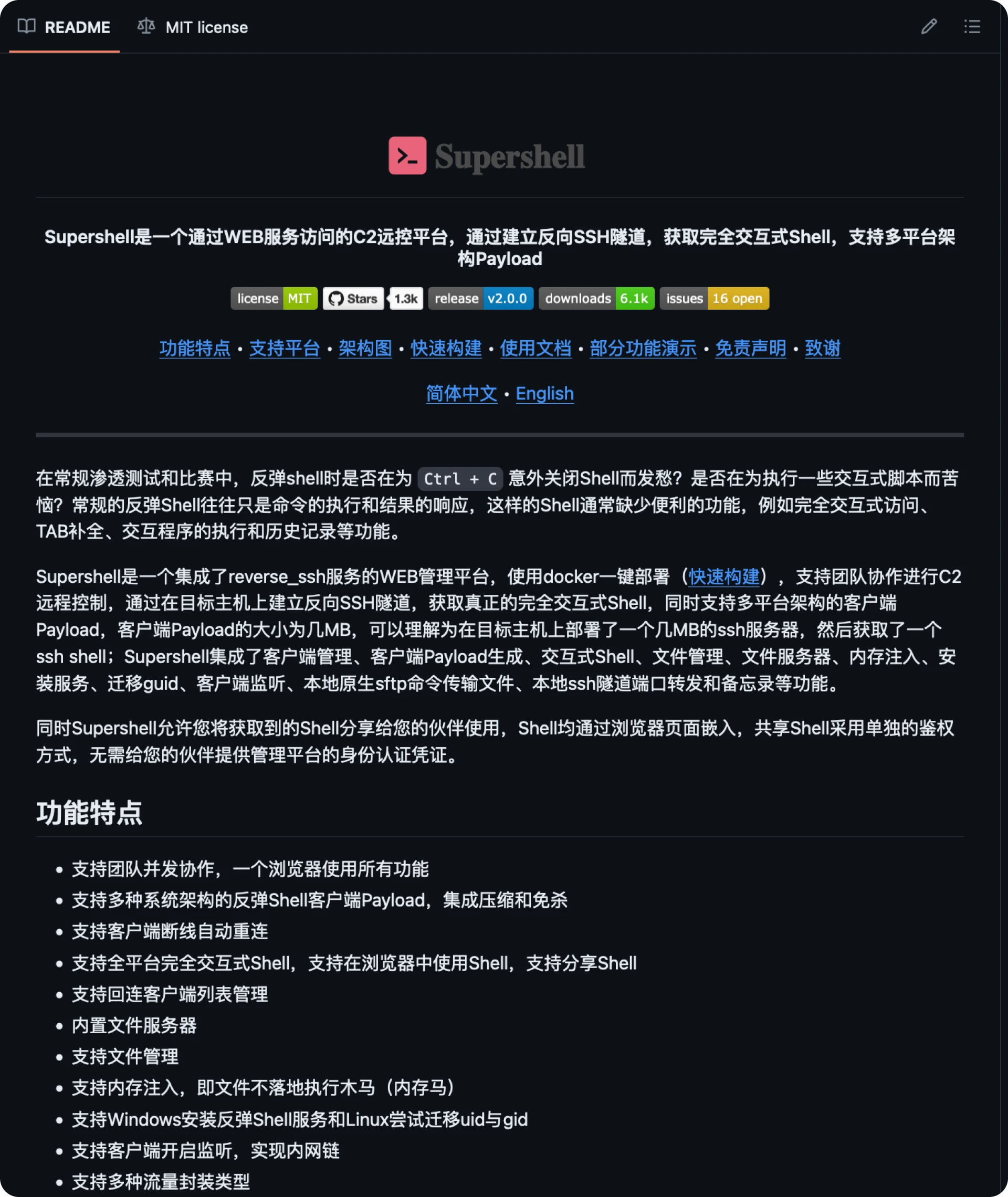
- SuperShell, an open-source C2 framework, and its capabilities warrant attention from defenders and researchers alike.
- Malicious files including SuperShell and Cobalt Strike indicate potential reconnaissance activities on victim systems after initial access.
Source: https://hunt.io/blog/uncovering-supershell-and-cobalt-strike-from-an-open-directory