CloudSEK STRIKE’s HUMINT uncovered a false-flag campaign by an actor using the alias “RedLineCyber” who distributes a PyInstaller-packed clipboard hijacker via Discord and Telegram, targeting cryptocurrency streamers and gambling communities. The malware, distributed as Pro.exe (also peeek.exe), monitors the Windows clipboard and silently replaces copied crypto addresses with attacker-controlled wallets for six cryptocurrencies while persisting via an HKCU Run key. #RedLineCyber #Pro.exe
Keypoints
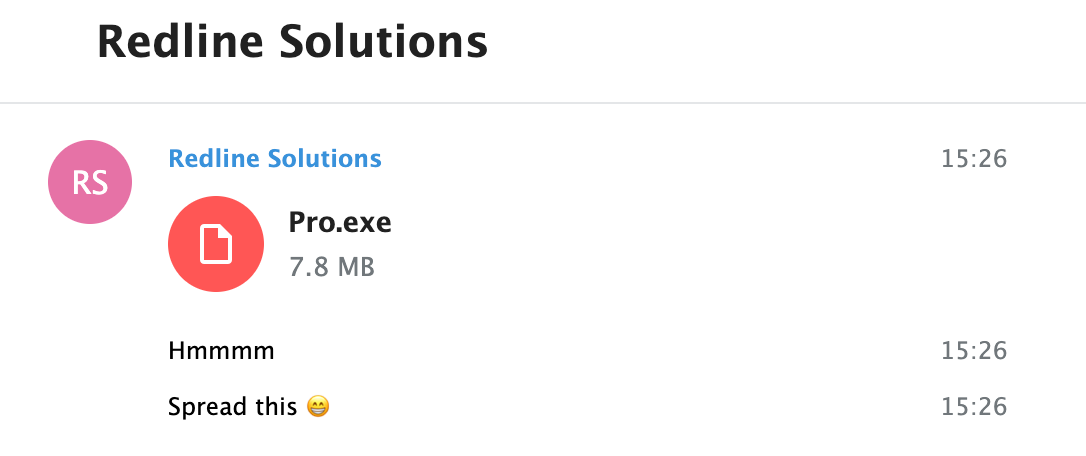
- CloudSEK HUMINT identified an actor using the alias “RedLineCyber” posing as “RedLine Solutions” to gain credibility within Discord communities focused on gaming, streaming, and gambling.
- Distribution uses targeted social engineering over Discord and Telegram, cultivating relationships with streamers and influencers and offering the executable as a “security tool” or “streaming utility.”
- The primary malware (Pro.exe / peeek.exe) is a PyInstaller-packaged Python clipboard hijacker that detects crypto addresses via base64-encoded regex patterns and replaces them with attacker-controlled wallets for BTC, ETH, SOL, DOGE, LTC, and TRX.
- Persistence is achieved through a Registry Run key (HKCUSoftwareMicrosoftWindowsCurrentVersionRunCryptoClipboardGuard) and a %APPDATA%CryptoClipboardGuard directory containing activity logs.
- The malware operates without network communication, minimizing detection risk, and has successfully diverted funds to attacker wallets across multiple blockchains, indicating measurable financial impact.
- Detection and hunting opportunities include monitoring Registry Run key creations, high-frequency clipboard API usage (OpenClipboard/GetClipboardData/SetClipboardText), process behavior for persistent clipboard monitoring, and regex patterns for crypto addresses.
MITRE Techniques
- [T1566.001 ] Phishing: Spearphishing Attachment – Actor used Discord-based social engineering and distributed the executable as a streaming/security utility (‘Discord-based social engineering in crypto/gaming communities; malware distributed as “streaming tool”‘)
- [T1204.002 ] User Execution: Malicious File – Victims manually executed the EXE believing it provided cryptocurrency protection functionality (‘Victims manually execute the EXE believing it provides cryptocurrency protection functionality’)
- [T1547.001 ] Boot or Logon Autostart Execution: Registry Run Keys – Malware writes a Run key to HKCU to persist across reboots (‘Writes autostart entry to Windows Registry: Key: HKCUSoftwareMicrosoftWindowsCurrentVersionRun Value Name: CryptoClipboardGuard’)
- [T1115 ] Clipboard Data – Continuous 300ms polling of the clipboard via win32clipboard APIs to detect and act on cryptocurrency addresses (‘Continuous 300ms polling of clipboard via win32clipboard API; captures cryptocurrency addresses via regex patterns for BTC, ETH, SOL, DOGE, LTC, TRX’)
- [T1565.001 ] Data Manipulation: Stored Data Manipulation – Real-time replacement of clipboard contents with attacker-controlled wallet addresses during transaction attempts (‘Replaced crypto address: [original_victim_address] -> [attacker_address]’)
Indicators of Compromise
- [File Hash ] primary and related sample hashes – 0d6e83e240e41013a5ab6dfd847c689447755e8b162215866d7390c793694dc6, d011068781cfba0955258505dbe7e5c7d3d0b955e7f7640d2f1019d425278087
- [File Name ] observed malicious executables – Pro.exe, peeek.exe
- [File Path / Directory ] persistence and logging locations – %APPDATA%CryptoClipboardGuard, %APPDATA%CryptoClipboardGuardactivity.log
- [Registry Key ] autostart persistence – HKCUSoftwareMicrosoftWindowsCurrentVersionRun (CryptoClipboardGuard)
- [Cryptocurrency Wallet ] attacker-controlled addresses used for theft – bc1qz7jvkt7ex47x2nqm5mzkpaetff6sxmr75uyez (BTC), 0x43726m3E8C97d8A9F0cdE1B1ad77A63E1c2Ef41c (ETH), and 4 more addresses
- [Discord Invites ] distribution channels used for targeting – discord.gg/pkle, discord.gg/watchgamestv, and 6 more invite links
- [API Calls / Behavioral ] clipboard API usage indicative of clipper activity – win32clipboard.OpenClipboard, GetClipboardData, SetClipboardText (300 ms polling pattern)