Huntress has added an Incident Report Timeline to Managed ITDR to provide a detailed, chronological view of identity-driven incidents, showing both attacker actions and Huntress remediation steps. The timeline improves visibility into potential data exfiltration, speeds impact assessment, and helps MSPs clearly communicate incident impact and response. #Huntress #ManagedITDR
Keypoints
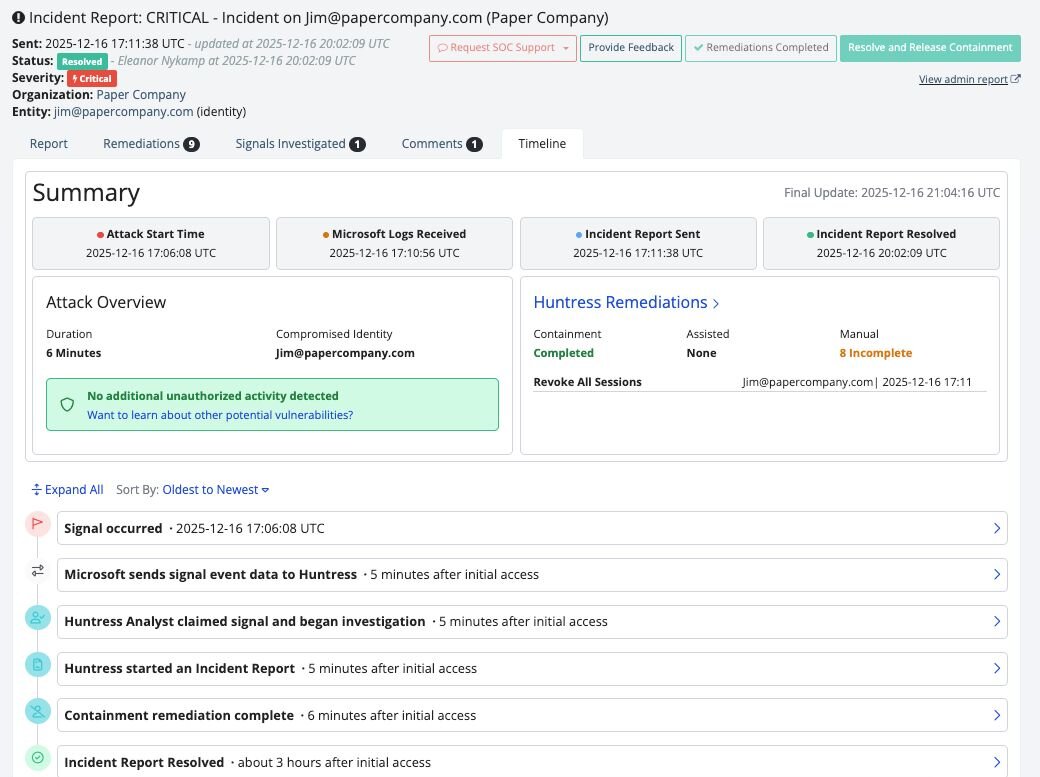
- Huntress introduced the Incident Report Timeline within Managed ITDR to give customers a chronological narrative of identity-driven incidents from detection through remediation.
- The timeline shows attacker activity (enumeration, suspicious sessions, potential data access/movement) alongside Huntress analyst validation and containment actions.
- This capability addresses gaps caused by fragmented logs and scattered alerts, providing clarity that speeds decision-making and response.
- Organizations can use the timeline to rapidly determine whether sensitive data was accessed, whether additional remediation is needed, and whether legal or compliance actions are required.
- MSPs gain a professional, easy-to-consume artifact to explain incident impact and response to business stakeholders, strengthening customer trust and demonstrating security value.
- The feature is designed for modern identity-driven attacks, enabling teams to validate response effectiveness and prioritize access reviews, credential resets, and conditional access policies.
MITRE Techniques
- [N/A ] No MITRE ATT&CK techniques were explicitly mentioned in the article – ‘No MITRE techniques mentioned in the article.’
Indicators of Compromise
- [None ] No indicators of compromise (IP addresses, file hashes, domains, or file names) were provided in the article – ‘No indicators of compromise were included in the article.’
Read more: https://www.huntress.com/blog/huntress-managed-itdr-incident-report-timeline-response