A new wave of cyberattacks exploits legitimate Remote Monitoring and Management (RMM) tools like LogMeIn Resolve and PDQ Connect to gain unauthorized remote access. Attackers deceive users into installing these trusted programs, allowing them to evade detection and maintain persistent control over infected systems. #LogMeInResolve #PDQConnect
Keypoints
- Cybercriminals are using compromised legitimate RMM tools to evade traditional security measures.
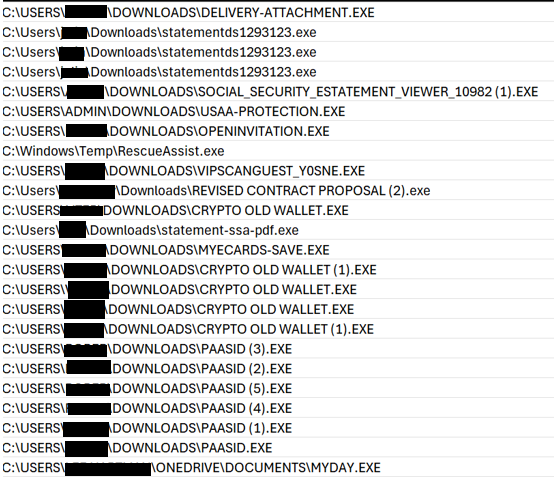
- Attackers spread malicious downloads through fake websites and emails mimicking trusted utilities.
- Pre-configured RMM installers connect directly to attacker control panels using unique identifiers.
- Security software often overlooks RMM traffic because it appears as normal admin communication.
- Users are advised to download software only from official sources and verify file integrity to stay protected.