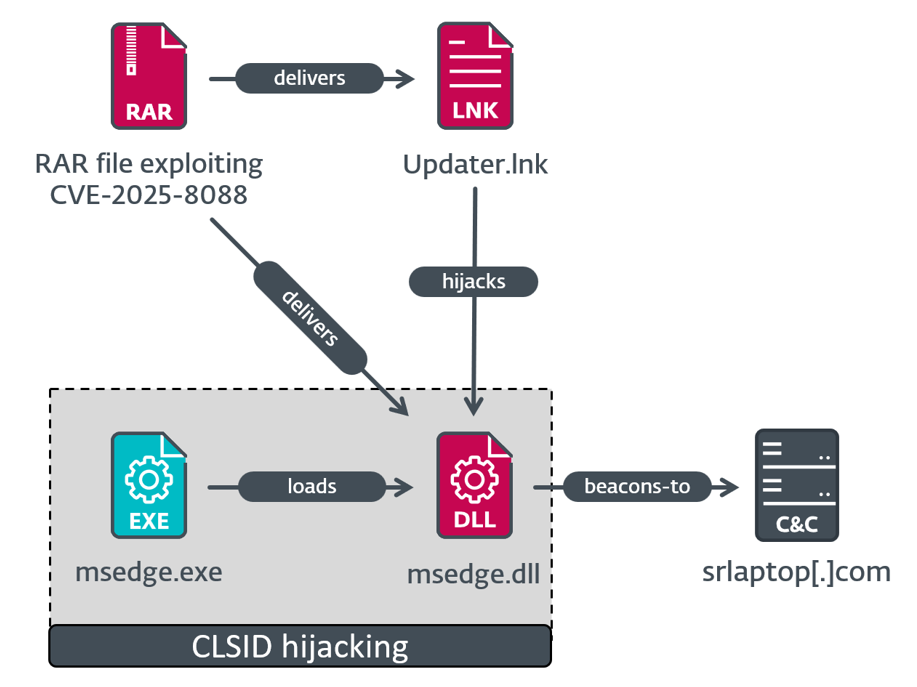
Paper Werewolf exploited email attachments in July and August to install malware through vulnerabilities. The attack chains involved deploying Mythic Agent, SnipBot, RustyClaw, and Melting Claw malware, exploiting WinRAR and other weaknesses. #PaperWerewolf #MythicAgent #RomCom #WinRARZeroDay
Keypoints
- Paper Werewolf delivered exploits via email archives impersonating Russian research institute employees.
- They aimed to install malware giving them access to infected systems.
- ESET identified three different execution chains using various malware, including Mythic Agent and RomCom variants.
- WinRAR vulnerabilities, especially a zero-day, were exploited over several months before detection.
- Older WinRAR versions prior to 7.13 remain vulnerable, posing ongoing security risks.
Read More: https://arstechnica.com/security/2025/08/high-severity-winrar-0-day-exploited-for-weeks-by-2-groups/