GTIG tracked a Vietnam-based cluster UNC6229 that uses fake job postings on legitimate platforms and abused CRM/SaaS services to socially engineer digital advertising workers into downloading RATs or entering credentials on phishing pages to steal corporate ad/social accounts. The campaign leverages personalized follow-ups, password-protected attachments, and convincing phishing kits (including MFA-capable pages) to monetize access by selling ad inventory or compromised accounts. #UNC6229 #staffvirtual.website
Keypoints
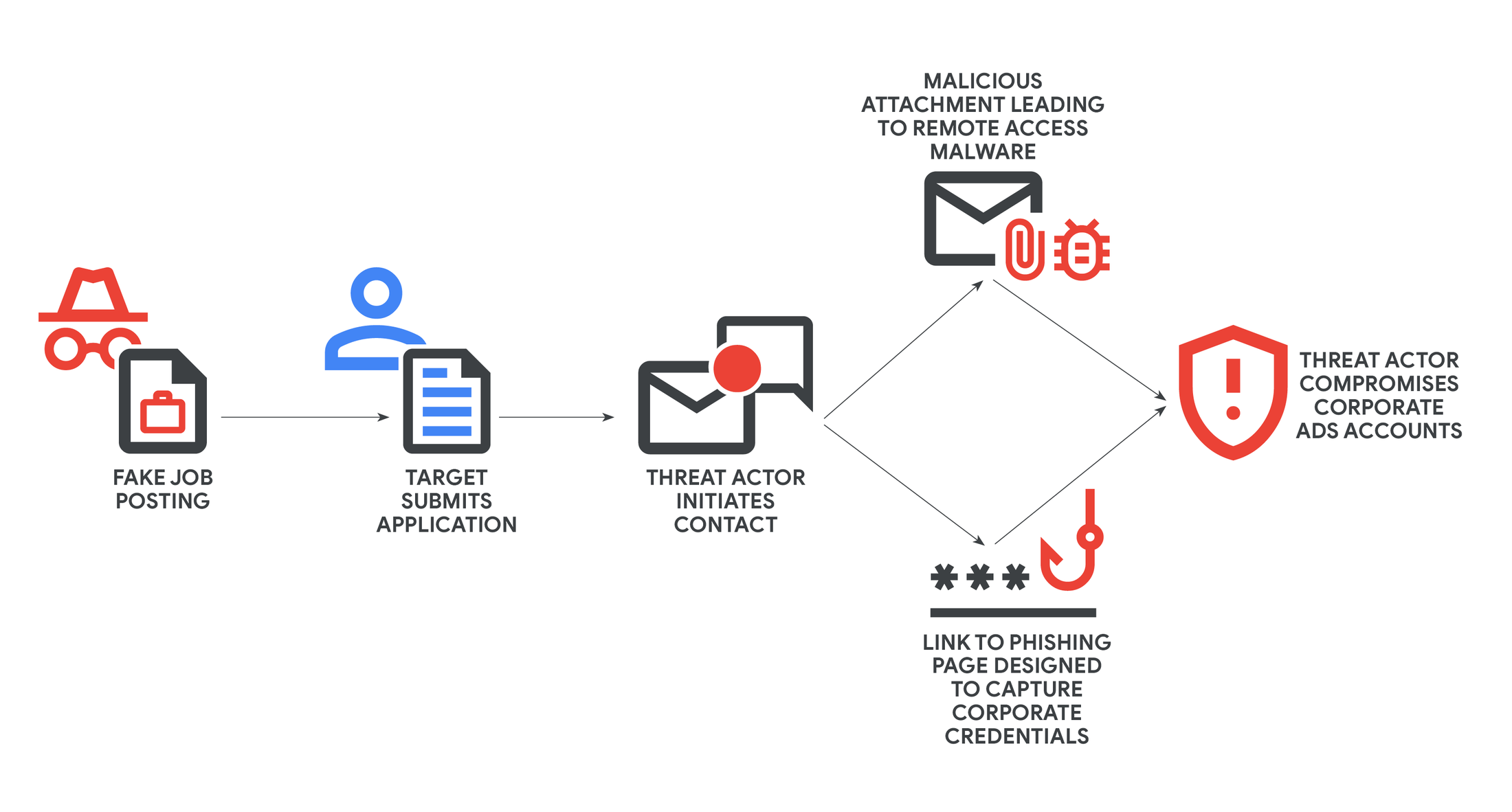
- UNC6229 operates fake job postings on legitimate employment and freelance platforms and on attacker-controlled websites to target digital advertising and marketing workers.
- Victim-initiated applications establish trust; attackers follow up with personalized messages that often use abused CRM platforms to increase legitimacy and bypass filters.
- Payload delivery includes password-protected ZIP attachments containing remote access trojans (RATs) and links to highly convincing phishing pages for credential harvesting.
- Phishing kits observed can target corporate email credentials and handle various MFA schemes, including Okta and Microsoft.
- Compromise of personal devices or personal accounts used on work machines enables access to corporate advertising and social media accounts, which are then monetized or sold.
- GTIG added identified malicious sites, domains, and files to Safe Browsing blocklists and shared findings with affected CRM vendors (e.g., Salesforce) to disrupt misuse.
- GTIG attributes the cluster to individuals operating from Vietnam and expects tactics to expand to other industries and continue abusing legitimate SaaS/CRM services.
MITRE Techniques
- [T1204] User Execution – Victim downloads and executes malware from a password-protected ZIP or opens attachments as part of a “mandatory” hiring step; “…the actor sends an attachment, often a password-protected ZIP file… The victim is instructed that opening the file is a mandatory step in the hiring process.”
- [T1192] Spearphishing Link – Actors send obfuscated links or shortened URLs to phishing pages used to harvest credentials and schedule interviews; “…the actor sends a link, sometimes obfuscated with a URL shortener, directing the victim to a phishing page.”
- [T1531] Account Discovery (abuse of CRM/SaaS) – Adversary abuses legitimate CRM and SaaS platforms to send bulk personalized emails and manage campaigns, increasing deliverability and trust; “…abusing a wide range of legitimate business and customer relationship management (CRM) platforms to send these initial emails and manage their campaigns.”
- [T1078] Valid Accounts – Phishing pages harvest corporate credentials (including MFA-capable flows) to gain access to corporate advertising/social accounts; “…configured to specifically target corporate email credentials and can handle various multi-factor authentication (MFA) schemes, including those from Okta and Microsoft.”
- [T1219] Remote Access Tools – Delivered remote access trojans (RATs) allow full control of victim devices to take over online accounts; “…payload often includes remote access trojans (RATs) that allow the actor to gain full control of the victim’s device and subsequently take over their online accounts.”
Indicators of Compromise
- [Domain] Fake job site used in lure – staffvirtual[.]website
- [File hash] Malware payload hashes – 137a6e6f09cb38905ff5c4ffe4b8967a45313d93bf19e03f8abe8238d589fb42, 33fc67b0daaffd81493818df4d58112def65138143cec9bd385ef164bb4ac8ab, and 3 more hashes