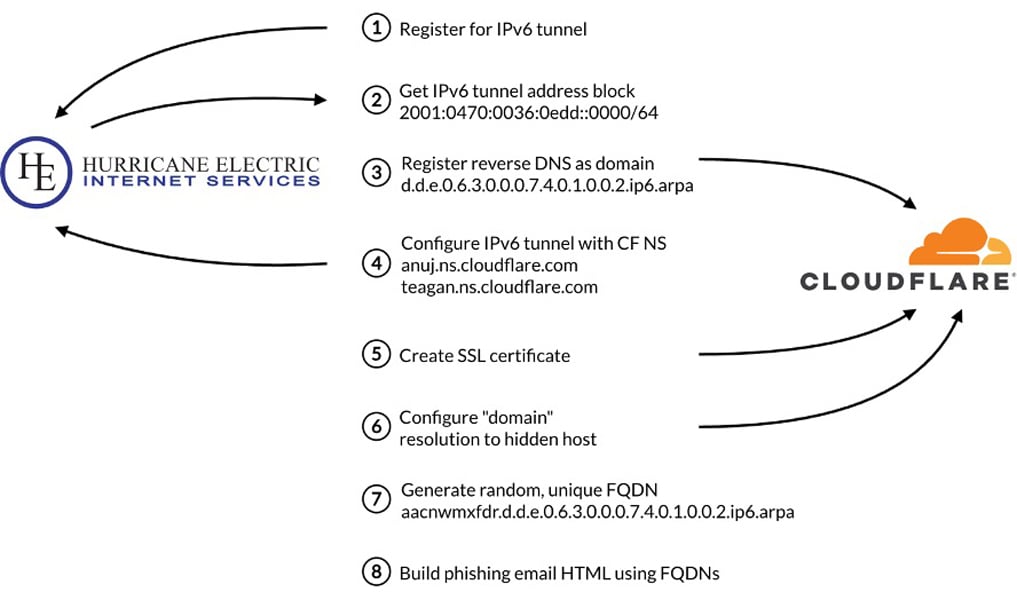
Threat actors are abusing the special-use .arpa TLD—especially ip6.arpa reverse DNS—by reserving IPv6 address space and creating nonstandard DNS records that point reverse-hostnames to phishing infrastructure. By leveraging reputable providers like Cloudflare and Hurricane Electric, using short-lived randomized ip6.arpa hostnames and TDS redirects, attackers can bypass domain reputation checks and email security filters, researchers at Infoblox warn. #Infoblox #Cloudflare
Keypoints
- Attackers register IPv6 blocks and create ip6.arpa reverse DNS names that map to A records hosting phishing sites.
- They exploit trusted DNS providers like Cloudflare and Hurricane Electric to inherit good reputations and mask backend infrastructure.
- Phishing emails embed image links pointing to ip6.arpa hostnames, which resolve transparently and evade domain-reputation checks.
- Short-lived links and traffic distribution systems (TDS) validate targets and redirect only eligible visitors to phishing pages, complicating analysis.
- Absence of WHOIS/domain-age metadata for .arpa names, plus CNAME hijacking and subdomain shadowing, hinders traditional email-gateway detection.