ESET observed a new wave of Operation DreamJob attributed to Lazarus targeting European defense and UAV-related companies using trojanized open-source projects and the ScoringMathTea RAT to steal proprietary information and manufacturing know-how. The campaign used DLL side-loading, reflective loading, and compromised WordPress sites for C2 infrastructure, suggesting a link to North Korea’s effort to scale up its drone program. #ScoringMathTea #Lazarus
Keypoints
- Lazarus targeted three European defense-sector companies (metal engineering, aircraft components manufacturer, and defense company), with at least two involved in UAV development.
- Initial access relied on Operation DreamJob social-engineering lures: faux job offers and trojanized PDF readers or trojanized open-source projects from GitHub.
- Main payload across observed incidents was ScoringMathTea, a RAT used by Lazarus since 2022, providing extensive remote control and exfiltration capabilities.
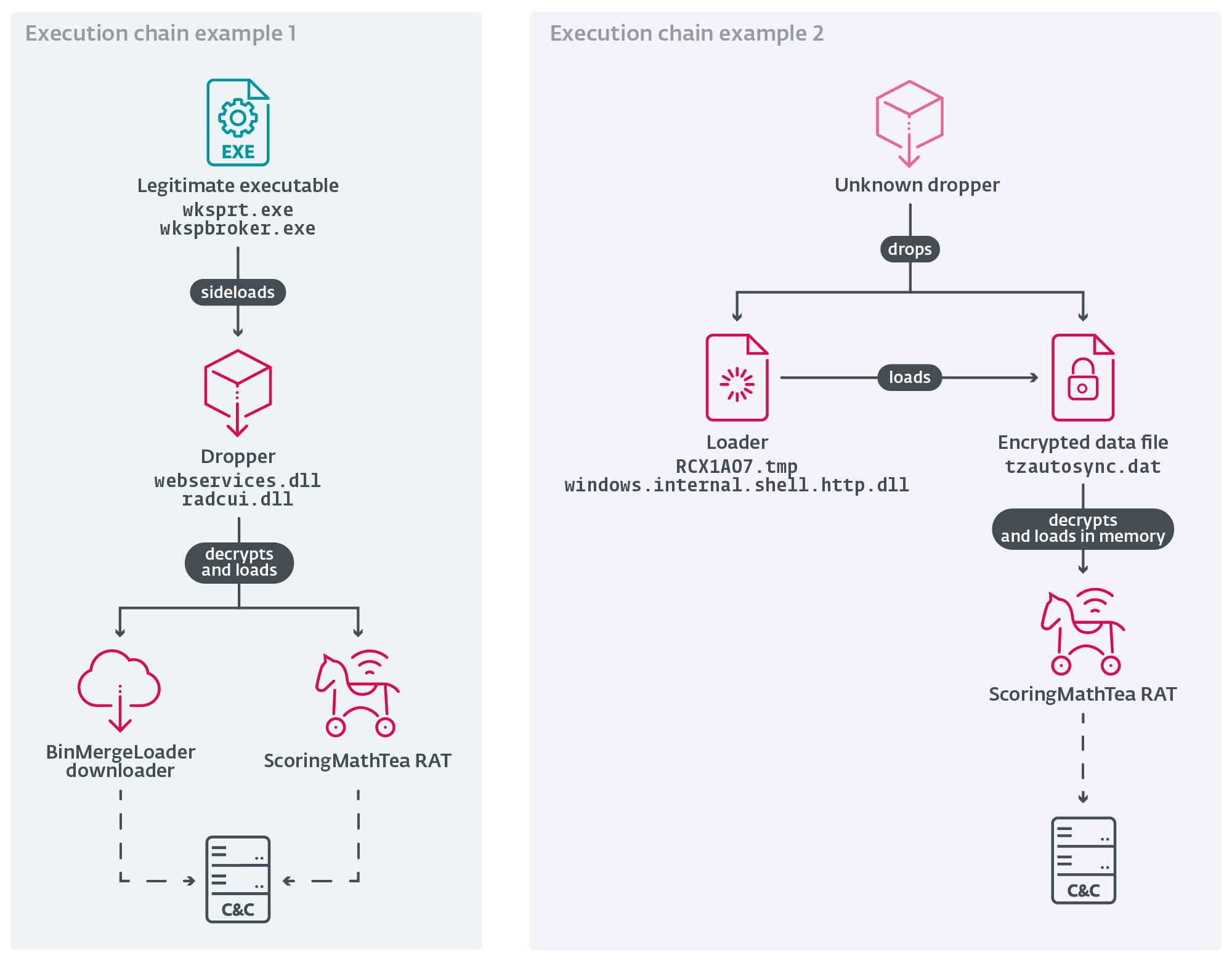
- Attackers trojanized various open-source projects (MuPDF, Notepad++ plugins, libpcre, DirectX wrappers) and used DLL proxying/side-loading to evade detection.
- Infrastructure used compromised WordPress sites and multiple C2 domains/IPs; BinMergeLoader and other loaders leveraged Microsoft Graph API and tokens in some cases.
- Toolset implements reflective DLL loading, dynamic API resolution, AES/ChaCha20 encryption for payload stages, and encrypted C2 channels (IDEA/AES + base64 encoding).
- Geopolitical context suggests the campaign may aim to gather UAV-related IP to assist North Korea’s drone development, possibly tied to observed DPRK-Russia cooperation and battlefield-relevant systems.
MITRE Techniques
- [T1584.004 ] Compromise Infrastructure: Server – ScoringMathTea uses compromised servers for C&C. Quote: ‘ScoringMathTea uses compromised servers for C&C.’
- [T1587.001 ] Develop Capabilities: Malware – All stages in the attack were likely developed by the attackers. Quote: ‘All stages in the attack were likely developed by the attackers.’
- [T1106 ] Native API – Windows APIs are essential for ScoringMathTea to function and are resolved dynamically at runtime. Quote: ‘Windows APIs are essential for ScoringMathTea to function and are resolved dynamically at runtime.’
- [T1129 ] Shared Modules – ScoringMathTea is able to load a downloaded DLL with the exports fun00 or exportfun00. Quote: ‘ScoringMathTea is able to load a downloaded DLL with the exports fun00 or exportfun00.’
- [T1204.002 ] User Execution: Malicious File – Lazarus attackers relied on the execution of trojanized PDF readers. Quote: ‘Lazarus attackers relied on the execution of trojanized PDF readers.’
- [T1574.002 ] Hijack Execution Flow: DLL Side-Loading – Trojanized droppers (webservices.dll, radcui.dll) use legitimate programs (wksprt.exe, wkspbroker.exe) for their loading. Quote: ‘Trojanized droppers (webservices.dll, radcui.dll) use legitimate programs (wksprt.exe, wkspbroker.exe) for their loading.’
- [T1134.002 ] Access Token Manipulation: Create Process with Token – ScoringMathTea can create a new process in the security context of the user represented by a specified token. Quote: ‘ScoringMathTea can create a new process in the security context of the user represented by a specified token.’
- [T1140 ] Deobfuscate/Decode Files or Information – The main payload, ScoringMathTea, is always encrypted on the file system. Quote: ‘The main payload, ScoringMathTea, is always encrypted on the file system.’
- [T1027.007 ] Obfuscated Files or Information: Dynamic API Resolution – ScoringMathTea resolves Windows APIs dynamically. Quote: ‘ScoringMathTea resolves Windows APIs dynamically.’
- [T1027.009 ] Obfuscated Files or Information: Embedded Payloads – The droppers of all malicious chains contain an embedded data array with an additional stage. Quote: ‘The droppers of all malicious chains contain an embedded data array with an additional stage.’
- [T1620 ] Reflective Code Loading – The droppers and loaders use reflective DLL injection. Quote: ‘The droppers and loaders use reflective DLL injection.’
- [T1055 ] Process Injection – ScoringMathTea and BinMergeLoader can reflectively load a DLL in the process specified by the PID. Quote: ‘ScoringMathTea and BinMergeLoader can reflectively load a DLL in the process specified by the PID.’
- [T1083 ] File and Directory Discovery – ScoringMathTea can locate a file by its name. Quote: ‘ScoringMathTea can locate a file by its name.’
- [T1057 ] Process Discovery – ScoringMathTea can list all running processes. Quote: ‘ScoringMathTea can list all running processes.’
- [T1082 ] System Information Discovery – ScoringMathTea can mimic the ver command. Quote: ‘ScoringMathTea can mimic the ver command.’
- [T1071.001 ] Application Layer Protocol: Web Protocols – ScoringMathTea and BinMergeLoader use HTTP and HTTPS for C&C. Quote: ‘ScoringMathTea and BinMergeLoader use HTTP and HTTPS for C&C.’
- [T1573.001 ] Encrypted Channel: Symmetric Cryptography – ScoringMathTea encrypts C&C traffic using the IDEA algorithm and BinMergeLoader using the AES algorithm. Quote: ‘ScoringMathTea encrypts C&C traffic using the IDEA algorithm and BinMergeLoader using the AES algorithm.’
- [T1132.001 ] Data Encoding: Standard Encoding – ScoringMathTea adds a base64-encoding layer to its encrypted C&C traffic. Quote: ‘ScoringMathTea adds a base64-encoding layer to its encrypted C&C traffic.’
- [T1041 ] Exfiltration Over C2 Channel – ScoringMathTea can exfiltrate data to its C&C server. Quote: ‘ScoringMathTea can exfiltrate data to its C&C server.’
Indicators of Compromise
- [File Hash ] Trojanized loaders/droppers and ScoringMathTea – 03D9B8F0FCF9173D2964CE7173D21E681DFA8DA4 (webservices.dll, DroneEXEHijackingLoader), 0CB73D70FD4132A4FF5493DAA84AAE839F6329D5 (libpcre.dll trojanized)
- [File Hash ] ScoringMathTea samples and decrypted payloads – 71D0DDB7C6CAC4BA2BDE679941FA92A31FBEC1FF (ScoringMathTea), AC16B1BAEDE349E4824335E0993533BF5FC116B3 (cache.dat decrypted ScoringMathTea)
- [Filename ] Trojans/disguised libraries – webservices.dll (dropper disguised as Microsoft Web Services Runtime), libmupdf.dll (loader disguised as MuPDF rendering library)
- [Domain ] C2 domains hosted on compromised WordPress sites – coralsunmarine[.]com (https://coralsunmarine[.]com/wp-content/themes/flatsome/inc/functions/function-hand.php), kazitradebd[.]com (https://kazitradebd[.]com/wp-content/themes/hello-elementor/includes/customizer/customizer-hand.php)
- [IP Address ] C2 hosting examples – 23.111.133[.]162 (coralsunmarine[.]com C2 first seen 2024-06-06), 104.21.80[.]1 (kazitradebd[.]com C2 first seen 2025-01-11)
Read more: https://www.welivesecurity.com/en/eset-research/gotta-fly-lazarus-targets-uav-sector/