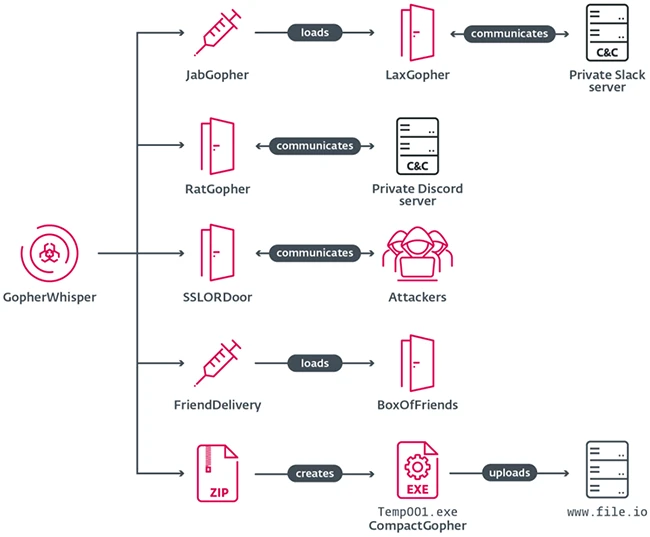
A newly identified China-aligned APT named GopherWhisper runs custom Go-based backdoors and loaders that hide command-and-control traffic inside popular collaboration platforms such as Slack, Discord, and Outlook drafts while exfiltrating data via file.io. ESET recovered thousands of Slack and Discord messages and Outlook drafts tied to a Mongolian government intrusion, revealing development logs, UTC+8 timestamps that support a China-aligned attribution and published indicators of compromise. #GopherWhisper #LaxGopher
Keypoints
- GopherWhisper is a China-aligned APT linked to an intrusion at a Mongolian governmental entity.
- The group’s toolset is largely written in Go and includes backdoors LaxGopher, RatGopher, BoxOfFriends, plus a C++ backdoor SSLORDoor.
- Each backdoor uses a different legitimate service for C2: Slack for LaxGopher, Discord for RatGopher, Outlook drafts via Microsoft Graph for BoxOfFriends, and SSLORDoor communicates over port 443.
- Supporting tools JabGopher and FriendDelivery load backdoors in memory and CompactGopher exfiltrates files through the file.io sharing service.
- ESET recovered operator messages and drafts that exposed development logs, UTC+8 timestamps matching China Standard Time, operational mistakes, and published IoCs.
Read More: https://www.helpnetsecurity.com/2026/04/23/gopherwhisper-apt-group/