Manufacturing companies are being actively targeted with localized invoice-themed phishing that leverages CVE-2024-43451 and WebDAV-based shortcuts to deliver AsyncRAT and XWorm. Proactive, industry- and region-specific threat hunting using ANY.RUN’s sandbox and Threat Intelligence Lookup can identify fresh samples, file hashes, malicious filenames, and hosting infrastructure (Dropbox/WebDAV) before widespread detection occurs. #AsyncRAT #CVE-2024-43451
Keypoints
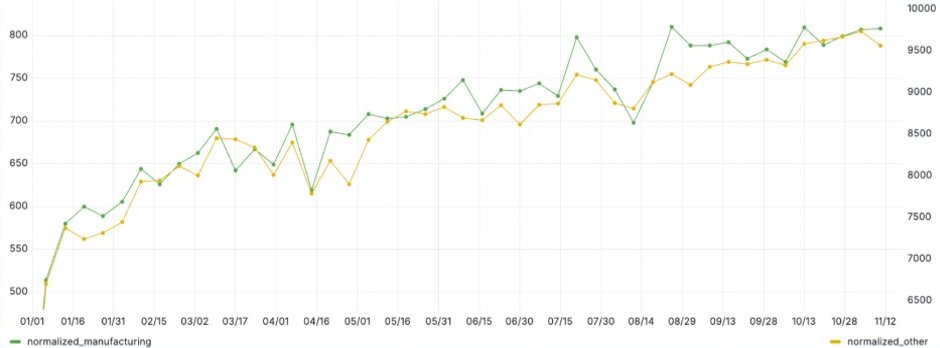
- Manufacturing is a top target for targeted phishing and ransomware campaigns, with a higher-than-average attack rate in some regions, notably Germany.
- Adversaries use localized, invoice- and supplier-themed lures with sender spoofing to increase credibility and click-through rates within manufacturing organizations.
- Attackers delivered a ZIP containing a .url shortcut hosted via Dropbox and WebDAV, using double extensions and a .lnk disguised as a PDF to trick users.
- The campaign exploited CVE-2024-43451 to force automatic WebDAV connections, enabling remote resource access without explicitly opening the .url file.
- Two RAT families, AsyncRAT and XWorm, were deployed, and many samples showed WebDAV connections, indicating standardized attack logic and campaign reuse.
- Fresh samples often show low vendor detection on VirusTotal, highlighting the need for sandbox analysis and rapid IOC enrichment for early detection.
- Filtering threat intelligence by industry and country (e.g., industry:”Manufacturing” AND submissionCountry:”DE”) improves relevance and enables proactive defensive actions before production impact.
MITRE Techniques
- [T1566.002 ] Spearphishing Link – Attackers sent invoice-themed phishing emails containing a link that redirected victims to a Dropbox-hosted ZIP archive (‘Clicking the link redirected victims to Dropbox, where a file named “COMPANY_NAME -Rechnung Nr. 21412122025.pdf.zip” awaited download’).
- [T1204.002 ] User Execution: Malicious File – The archive contained a .url and a .lnk disguised as a PDF to trick users into executing the payload (‘Archive contained “COMPANY_NAME-Rechnung Nr. 21412122025.pdf.url”, a shortcut file masquerading as a PDF’).
- [T1203 ] Exploitation for Client Execution – The campaign exploited CVE-2024-43451 to trigger automatic WebDAV connections during archive processing, enabling remote retrieval without explicitly opening the .url (‘leveraged CVE-2024-43451, a vulnerability that enables automatic WebDAV connections without actually opening the .url file’).
- [T1102 ] Web Service – Adversaries used cloud file hosting (Dropbox) to deliver the malicious ZIP archive and lure victims to download the payload (‘Clicking the link redirected victims to Dropbox, where a file … awaited download’).
- [T1105 ] Ingress Tool Transfer – Attackers retrieved additional malicious files and shortcuts via WebDAV/network resources after the automatic connection was initiated (‘Remote resource displays as a network directory; Contains .lnk file disguised as a PDF’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – WebDAV and web-based connections were used consistently across samples for delivery and C2-style interactions, indicating standardized communication channels (‘WebDAV connections are present in all samples, indicating standardized attack logic’).
Indicators of Compromise
- [File Hash ] malicious document used in campaign – 8af19a103fbab4d5a2b9f59098e78e61df1721508e2d148fe9ba2b29e72900ca
- [File Name ] lure archive and shortcut – “COMPANY_NAME-Rechnung Nr. 21412122025.pdf.zip”, “COMPANY_NAME-Rechnung Nr. 21412122025.pdf.url”
- [Email Address ] phishing sender used for spoofing – g.bader-gmbh@gmx[.]de (display name shown as “COMPANY_NAME eG”)
- [Domain/Service ] file hosting and delivery infrastructure – dropbox[.]com (Dropbox-hosted ZIP), gmx[.]de (email provider domain)
- [Vulnerability ] exploited CVE used to force WebDAV connections – CVE-2024-43451
- [Malware ] deployed remote access tools observed in analyses – AsyncRAT, XWorm
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/german-manufacture-attack/