JA3 TLS fingerprints are still useful as durable, tool-level behavioral indicators that can reveal new malicious tooling and enable clustering of related activity when enriched with context. ANY.RUN shows how JA3 frequency analysis and TI Lookup link specific JA3 hashes to malware and exfiltration channels, e.g., Remcos and Skuld. #Remcos #Skuld
Keypoints
- JA3 fingerprints represent a tool-level indicator (Tools level in the Pyramid of Pain) rather than disposable IOCs like IPs or domains.
- Frequency analysis of JA3 hashes can surface new malicious tooling early, before signatures exist.
- JA3 is rarely useful in isolation; contextual data (SNI, JA3S, URI, host telemetry) is critical to avoid false positives.
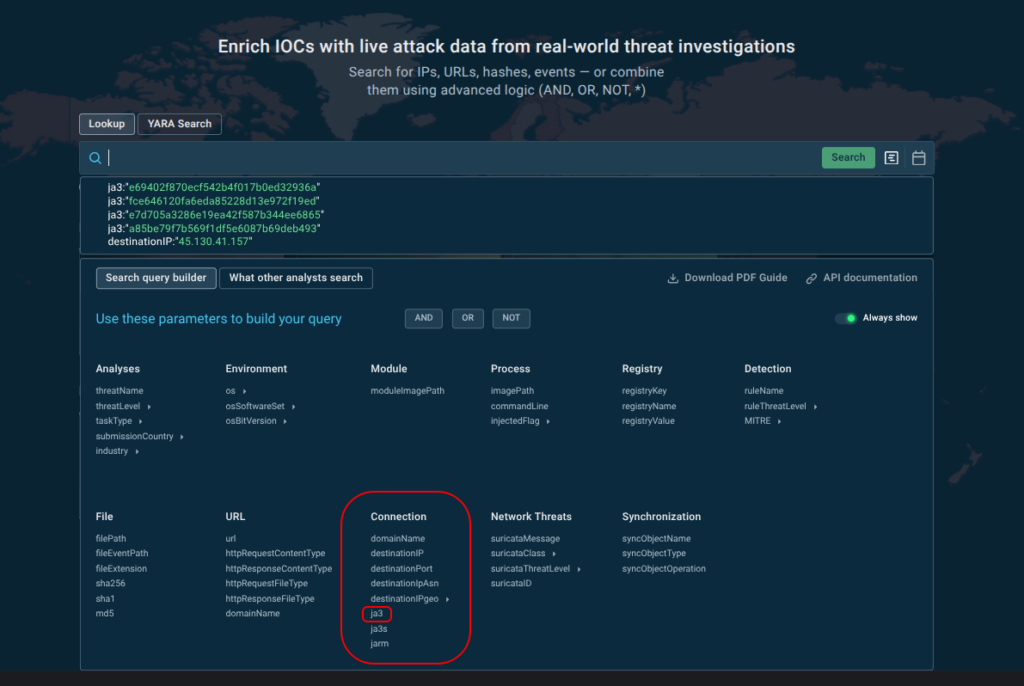
- ANY.RUN’s Threat Intelligence Lookup makes JA3 searchable and pivotable, linking hashes to malware samples, infrastructure, and session data.
- Specific JA3 hashes were associated with Remcos, an old TOR client linked to WannaCry, and LogMeIn Rescue riskware in the sandbox analyses.
- JA3-based hunting enabled clustering of activity for the Skuld family and revealed exfiltration channels via Discord, Telegram, and GoFile.
MITRE Techniques
- [T1071 ] Application Layer Protocol – JA3/ TLS ClientHello fingerprints describe client-side application-layer protocol characteristics used for C2 and communication profiling (‘JA3 fingerprints are built from TLS ClientHello parameters (version, cipher suites, extensions, supported groups/elliptic curves, EC point formats)’)
- [T1573 ] Encrypted Channel – Attackers and tools use TLS/SSL to secure C2 and exfiltration traffic, necessitating JA3-based detection of encrypted profiles (‘JA3 describes a long-term network profile of a tool that tends to repeat across many samples using the same network module.’)
- [T1567 ] Exfiltration Over Web Service – Analysts observed data exfiltration via web services/platforms (Discord, Telegram, GoFile) tied to JA3 fingerprints (‘Data exfiltration via Discord’; ‘Data exfiltration via Telegram’; ‘GoFile – in this analysis: Data exfiltration via GoFile’)
Indicators of Compromise
- [JA3 hash ] Sandbox and TI associations – a85be79f7b569f1df5e6087b69deb493 (Remcos), e7d705a3286e19ea42f587b344ee6865 (TOR/WannaCry), and 3 more hashes
- [Domain ] Exfiltration and infrastructure – gofile.io, discord.com, and other domains such as ip-api.com
- [SHA256 ] Sample hashes observed in analyses – B86f00212f8c04cef7e360e309b1b54648335f7c61099d4677889513166555ef, 72fa3ff5c1f473698df243455b7741b7a63ace3ce2903f65c8fe407d4ce9b435
- [Dropped file paths ] Exfiltrated data artifacts – %TEMP%browsers.zip, %TEMP%commonfiles.zip
- [HTTP parameter ] Exfiltration metadata – request body parameter “username”:”necrograbber”
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/ja3-hashes-threat-intelligence/