Cybercriminals are becoming more sophisticated in social engineering, using legitimate tools and tactics like tunneling utilities to evade detection. The attack speed has increased, with lateral movement in networks occurring in less than 60 minutes on average. #ClickFix #LummaStealer
Keypoints
- Cybercriminals are increasingly using social engineering combined with legitimate tools to breach networks.
- The time between initial compromise and lateral movement has decreased significantly, often under 60 minutes.
- Attacks frequently rely on Remote Desktop Protocol and multiple RMM tools to maintain stealthy access.
- Fake CAPTCHA scams and help desk impersonation are driving a rise in social engineering-based initial access methods.
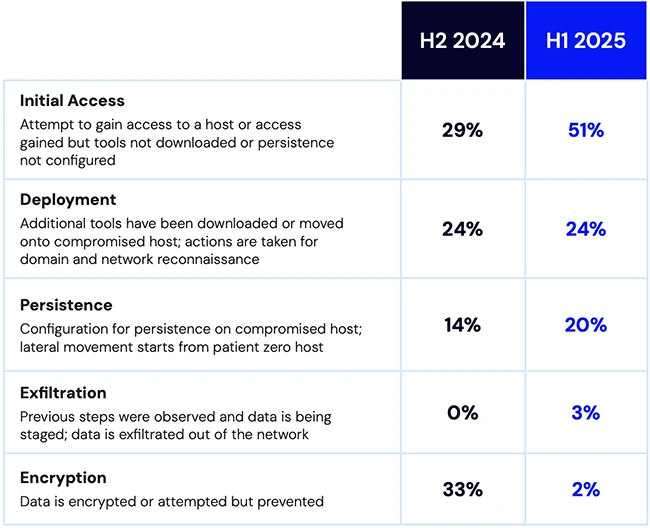
- While ransomware incidents have declined, threat actors continue to focus on data theft and credential harvesting.
Read More: https://www.helpnetsecurity.com/2025/08/08/cyber-deception-threat-trends-2025/