The blog analyzes a multistage campaign that weaponized Visual Studio Code extensions to deliver the Evelyn information stealer, using a DLL downloader, a process-hollowing injector, and a final payload that harvests developer credentials and cryptocurrency data. The malware uses AES-256-CBC encryption, multiple anti-analysis checks, and FTP-based C2/exfiltration to evade detection and persist in developer environments. #EvelynStealer #VisualStudioCode
Keypoints
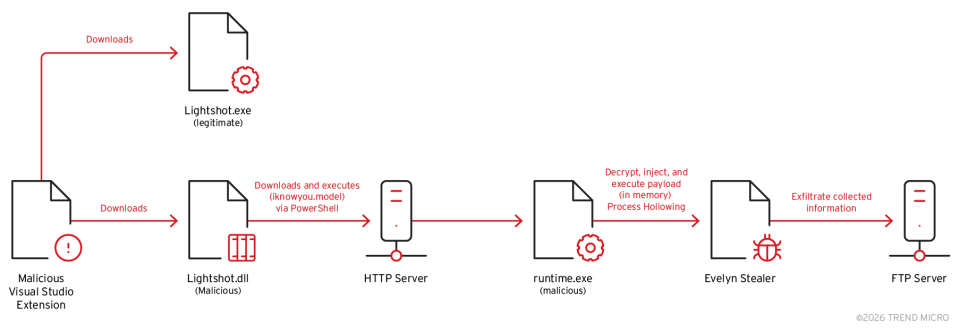
- The campaign abused the Visual Studio Code extension ecosystem to install a multistage loader that begins as a malicious Lightshot DLL.
- The first-stage downloader (Lightshot.dll) launches a hidden PowerShell command to retrieve and save a second-stage injector (runtime.exe / iknowyou.model).
- The second-stage is a process-hollowing injector that decrypts an AES-256-CBC–protected final payload and injects Evelyn Stealer into a suspended grpconv.exe process.
- Evelyn Stealer uses DLL injection to harvest browser credentials, capture screenshots, collect clipboard and Wi‑Fi data, and steal cryptocurrency wallet information.
- The malware implements numerous anti-analysis techniques (VM/Hyper-V detection, debugger checks, GPU/hostname/disk/process/registry checks) to evade sandboxes and researchers.
- Command-and-control and exfiltration use FTP, with stolen data archived into a detailed, metadata-rich ZIP filename and uploaded to attacker-controlled servers.
MITRE Techniques
- [T1055 ] Process Injection – Used to inject code into browser and other processes to harvest credentials and run components (‘…harvests browser credentials through DLL injection…’)
- [T1055.012 ] Process Hollowing – The second-stage injector decrypts and injects the final payload into a suspended legitimate process (“grpconv.exe”) and then resumes it (‘…process hollowing injector, designed to decrypt and inject a third-stage payload into the legitimate Windows process, “grpconv.exe”.’)
- [T1071.004 ] Application Layer Protocol: FTP – The malware communicates with C2 and downloads components over FTP (‘…communicates with its command-and-control (C&C) server over FTP.’)
- [T1041 ] Exfiltration Over C2 Channel – Collected data is archived and uploaded to attacker servers via FTP (‘…sends it to the attacker’s C&C server over FTP.’)
- [T1027 ] Obfuscated Files or Information – The final payload is stored encrypted and decrypted at runtime using AES-256-CBC to hinder analysis (‘…uses AES-256-CBC encryption to decrypt the final payload…’)
- [T1497 ] Virtualization/Sandbox Evasion – The stealer performs multiple anti-VM and sandbox checks (GPU, hostname, disk size, processes, registry) to avoid analysis environments (‘…implements different virtual machine detection methods, debugger detection, and specialized checks for analysis environments like Remote Desktop Protocol (RDP) sessions and Hyper-V.’)
- [T1113 ] Screen Capture – The malware captures desktop screenshots as part of its data collection routine (‘…can also capture screenshots…’)
- [T1115 ] Clipboard Data – The malware harvests clipboard contents to capture sensitive information such as wallet keys (‘…as well as files and information such as clipboard and Wi-Fi credentials.’)
Indicators of Compromise
- [File hashes ] First-stage, injector, and final payload hashes – Lightshot.dll (SHA256: 369479bd9a248c9448705c222d81ff1a0143343a138fc38fc0ea00f54fcc1598), iknowyou.model (SHA256: 92af258d13494f208ccf76f53a36f288060543f02ed438531e0675b85da00430), and 2 more hashes.
- [File names ] Stage and component names observed on disk or in Temp – Lightshot.dll (first-stage downloader), EvelynStealer.exe (final payload), and other components such as abe_decrypt.dll (browser injection component).
- [Domains ] C2 and distribution hosts – server09.mentality.cloud (FTP C2 / component downloads), syn1112223334445556667778889990.org (HTTP server used in the campaign).
Read more: https://www.trendmicro.com/en_us/research/26/a/analysis-of-the-evelyn-stealer-campaign.html