Researchers mapped additional network infrastructure and indicators linked to the February 2026 Notepad++ update-channel compromise, identifying C2 domains, Cobalt Strike beacon IPs, and likely malicious file-hosting addresses. Analysis shows the attackers used access to a shared hosting account to selectively redirect update traffic and deliver malicious payloads. #Notepad++ #CobaltStrike
Keypoints
- The Notepad++ upgrade distribution channel was compromised from June 2025 until between November 10 and December 2, 2025, enabling malicious updates to be served to users.
- Rapid7 reported C2 and beacon indicators including api[.]skycloudcenter[.]com (61.4.102[.]97), api[.]wiresguard[.]com, and beacon IPs 59.110.7[.]32 and 124.222.137[.]114.
- Validin scanning uncovered additional related IPs and domains: initial download IP 95.179.213[.]0, an additional likely malicious download IP 45.32.144[.]255, and a pivot-linked IP 160.250.93[.]48 resolving to api.cloudtrafficservice[.]com.
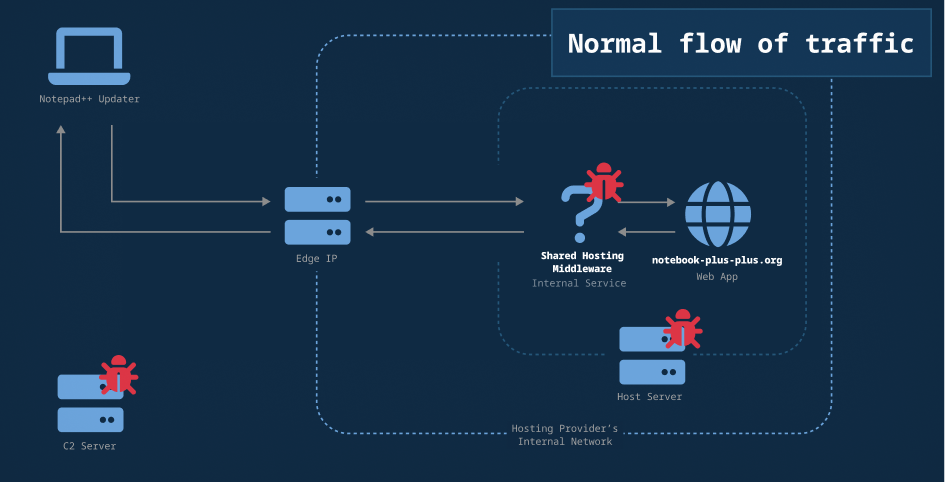
- Evidence suggests selective redirection on a compromised shared hosting account (Hostinger or reseller) was used to serve malicious updates rather than broad compromise across all accounts.
- Certificate and host-response data pointed to a likely origin IP for the Cobalt Strike beacon (103.159.133[.]178) and an observed self-signed certificate with CN wiresguard[.]com.
- Some malicious infrastructure remained active at the time of reporting, and DNS/history pivots revealed brief use and reuse of domains registered via Namecheap.
MITRE Techniques
- [T1195 ] Supply Chain Compromise – Actor delivered malicious updates by abusing the software distribution/update mechanism (‘The threat actor used their access to provide malicious updates by selectively redirecting users to an attacker-controlled server.’)
- [T1078 ] Valid Accounts – Actor maintained access on a shared hosting account to manipulate update delivery (‘the Notepad++ account was the only account targeted despite the attackers potentially having access to many other accounts.’)
- [T1105 ] Ingress Tool Transfer – Malicious payloads were hosted for initial download from attacker-controlled IPs (‘95.179.213[.]0 – provided the first suspicious file downloaded in the infection chain’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – C2 and beacon communications used HTTP/HTTPS over non-standard ports for Cobalt Strike beacons and C2 (‘api[.]skycloudcenter[.]com – Command and Control (C2) provider (HTTPS, port 443)’; ‘59.110.7[.]32 – IP hosting Cobalt Strike beacon (HTTP, port 8880)’)
Indicators of Compromise
- [IP address ] initial/malicious hosts and beacons – 95.179.213[.]0, 59.110.7[.]32, and other 6 IPs (61.4.102[.]97, 124.222.137[.]114, 103.159.133[.]178, 160.250.93[.]48, 45.32.144[.]255, 45.32.144[.]255 listed in report)
- [Domain ] C2 and beacon domains – api[.]skycloudcenter[.]com, api[.]wiresguard[.]com, and other 3 domains (api[.]cloudtrafficservice[.]com, cloudtrafficservice[.]com, wiresguard[.]com)
- [TLS certificate CN ] certificate-based pivot – self-signed certificate with Common Name wiresguard[.]com observed on 103.159.133[.]178
- [SHA1 response hash ] host response identifier – ‘Service is unavailable.’ response SHA1 23ce73454ebf289b2c25c3885887ac3d6055fa63 used to link similar hosts
- [Host header hash ] response header pivot – host header hash f400115bf3326edba086 used to correlate the confirmed C2 with other IPs
Read more: https://www.validin.com/blog/exploring_notepad_plus_plus_network_indicators/