This article explores a rare glimpse into the operations of North Korean threat actors involved in a major cryptocurrency heist, revealing their use of sophisticated malware infrastructure. An interactive forensic dashboard allows users to explore the infected machine and understand the tactics, techniques, and tools used by these APT actors. #LazarusGroup #NorthKoreanCyberThreats
Keypoints
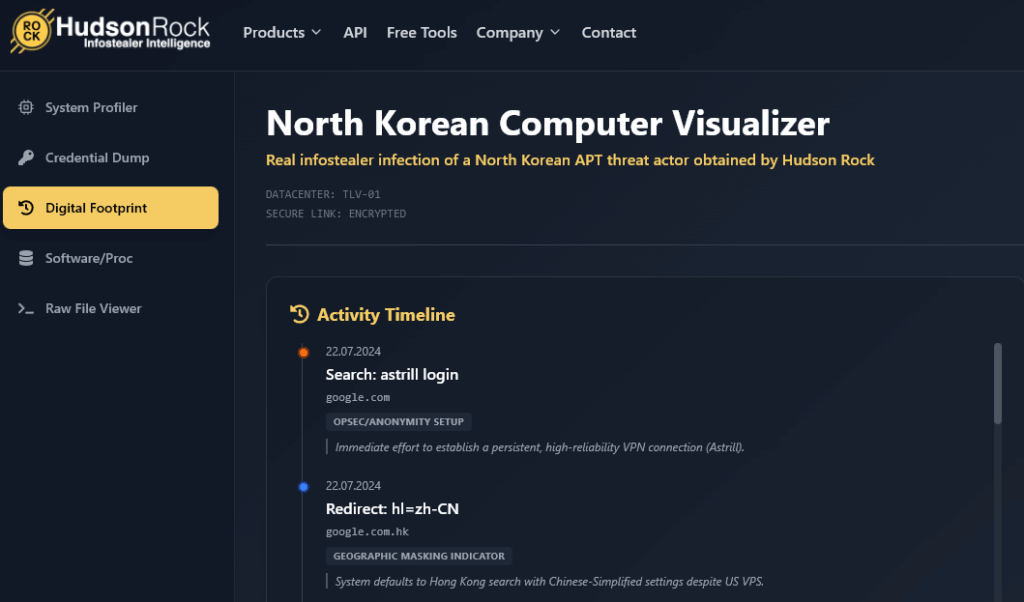
- A North Korean threat actor was infected using LummaC2 infostealer malware, revealing operational vulnerabilities.
- The infected machine is linked to the broader Lazarus cyber ecosystem involved in the $1.4 billion ByBit crypto heist.
- Tools like Visual Studio and Enigma Protector indicate professional malware development and evasion techniques.
- Use of Dropbox, Slack, and Telegram suggests multiple channels for data exfiltration and command-and-control activities.
- Domain registration and phishing setups involve impersonation to distribute malware and facilitate financial theft.