EvilTokens is a Phishing-as-a-Service (PhaaS) that provides turnkey Microsoft device code phishing pages, a centralised affiliate administration panel, and a custom browser to weaponise harvested access and refresh tokens for mailbox access and persistence. Its backend integrates an AI-driven pipeline that uses Microsoft Graph API and chained LLM prompts to automatically identify exploitable payment threads and draft tailored BEC emails, dramatically accelerating post-compromise fraud. #EvilTokens #MicrosoftGraphAPI
Keypoints
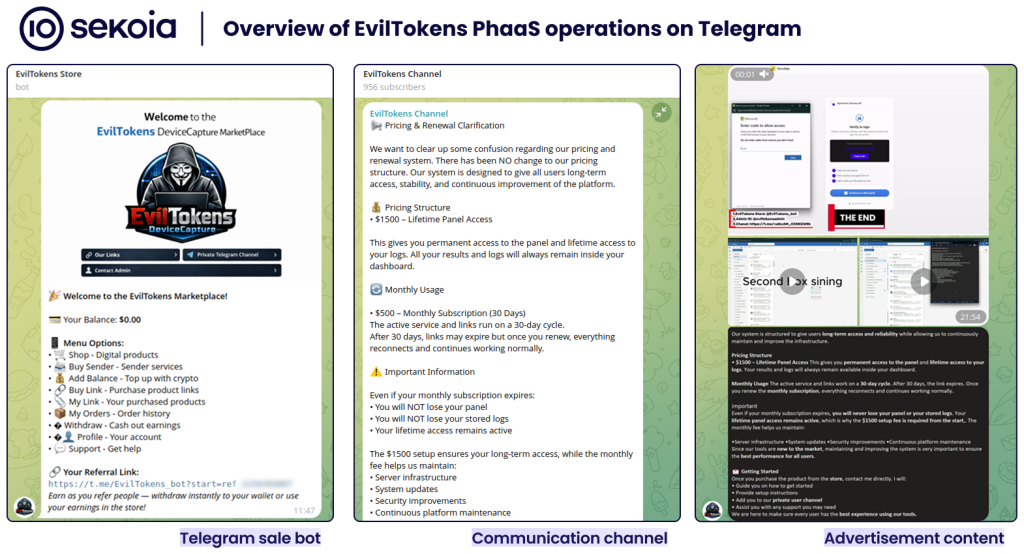
- EvilTokens is sold via Telegram (eviltokensadmin) as a PhaaS offering device code phishing kits, deployment bots, anti-bot pages, and affiliate management tools.
- The Office 365 capture link kit enables affiliates (one-time $1500 + $500/month) to capture Microsoft access and refresh tokens through the OAuth device code flow and view them in a centralised admin panel.
- The platform includes a custom “Portal Browser” (ET Browser) to simultaneously access multiple Microsoft 365 accounts using stolen tokens, and a built-in webmail interface that impersonates Outlook for direct mailbox access.
- Affiliate PHP code relays victim interactions to a central backend via endpoints (api/device/start, api/device/status/{sessionId}, api/ext/link/create) and forwards X-Real-IP and X-Tenant-Secret headers for authentication and attribution.
- The EvilTokens backend performs reconnaissance via Microsoft Graph API (emails, contacts, events, folders, manager/directReports, organization) and exchanges tokens for a Primary Refresh Token (PRT) to establish persistence.
- An AI-driven pipeline ingests up to 5,000 emails in batches, uses LLM models (llama-3.1-8b-instant, llama-3.3-70b-versatile, Groq API, and gpt-4o-mini) to identify financial exposure, synthesize risk reports, and automatically draft realistic BEC email scenarios.
MITRE Techniques
- [T1566 ] Phishing – Device code phishing pages are used to trick victims into submitting device codes (“device code phishing”)
- [T1078 ] Valid Accounts – Harvested “access and refresh tokens” are used to access mailboxes and services without passwords (“access and refresh tokens”)
- [T1114 ] Email Collection – The backend “harvests victims’ emails” and mailbox contents for analysis and exfiltration (“harvest victims’ emails”)
- [T1567 ] Exfiltration Over Web Service – Microsoft Graph API requests are executed to perform reconnaissance and retrieve emails, contacts, events and files (“execute parallel Microsoft Graph API requests to perform reconnaissance”)
Indicators of Compromise
- [Domain ] PhaaS storefront and tooling – machinemind-market[.]com (Portal Browser sales), railway.app (hosting/deployment), and NOWPayments gateway references
- [Telegram handle ] PhaaS administration and sales – eviltokensadmin (advertising, bots, private channel/group)
- [File name ] Phishing kit files and server script – index.php (affiliate phishing script rendering device code pages)
- [API endpoints ] Backend device code relay and registration – api/device/start, api/device/status/{sessionId}, api/ext/link/create (used by affiliate PHP to interact with central backend)
- [Repository/platform ] Affiliate deployment artifacts – public GitHub repositories (phishing kit configuration and index.php) used to deploy on Railway.app