Summary: The Evil Corp cybercrime syndicate faces new sanctions from the US, UK, and Australia, targeting additional members and entities linked to its operations. The US has also indicted Aleksandr Ryzhenkov for his involvement in BitPaymer ransomware attacks against multiple victims.
Threat Actor: Evil Corp | Evil Corp
Victim: Multiple organizations | multiple organizations
Key Point :
- The US Treasury sanctioned seven individuals and two entities associated with Evil Corp, freezing their assets and prohibiting transactions with US, UK, and Australian businesses.
- Aleksandr Ryzhenkov was indicted for conducting ransomware attacks using BitPaymer, which has been linked to multiple victims since 2017.
- Evil Corp has a history of creating various ransomware families and has adapted its tactics to evade sanctions, including using LockBit ransomware.

The Evil Corp cybercrime syndicate has been hit with new sanctions by the United States, United Kingdom, and Australia. The US also indicted one of its members for conducting BitPaymer ransomware attacks.
In 2019, the United States sanctioned seventeen individuals and seven entities linked to the Evil Corp gang, including the group’s leader, Maksim Yakubets.
Today, the US Treasury’s Office of Foreign Assets Control (OFAC) sanctioned an additional seven individual and two entities associated with the cybercrime operation.
In a trilateral action, the UK and Australia are also sanctioning some of the Evil Corp suspects designated by OFAC today or in its 2019 sanctions.
The sanctioned individuals are Eduard Benderskiy (Maksim’s father-in-law), Viktor Grigoryevich Yakubets (Maksim’s father), Aleksandr Viktorovich Ryzhenkov, Sergey Viktorovich Ryzhenkov, Aleksey Yevgenevich Shchetinin, Beyat Enverovich Ramazanov, and Vadim Gennadievich Pogodin.
The two sanctioned entities are Vympel-Assistance LLC and Solar-Invest LLC, which are owned by Benderskiy, the reported father-in-law of Evil Corp’s leader Maksim Yakubets.
“Eduard Benderskiy (Benderskiy), a former Spetnaz officer of the Russian Federal Security Service (FSB), which is designated under numerous OFAC sanctions authorities, current Russian businessman, and the father-in-law of Evil Corp’s leader Maksim Viktorovich Yakubets (Maksim), has been a key enabler of Evil Corp’s relationship with the Russian state,” alleges the U.S. Department of the Treasury announcement.
“Benderskiy was a key enabler of their relationship with the Russian Intelligence Services who, prior to 2019, tasked Evil Corp to conduct cyber attacks and espionage operations against NATO allies,” alleges a joint NCA announcement.
As part of these sanctions, the individual’s assets have been frozen and businesses in the US, UK, and Australia can no longer transact with them.
This also means that organizations that suffer ransomware attacks by Evil Corp will no longer be able to make ransom payments without approval by OFAC or risk facing sanction violations.
Evil Corp member identified and indicted
The United States also unsealed an indictment today against suspected Evil Corp member Aleksandr Ryzhenkov for conducting ransomware attacks on multiple victims in the US.
Ryzhenkov is charged with utilizing the BitPaymer ransomware in multiple attacks against companies in the United States. BitPaymer is the first ransomware encryptor created by Evil Corp, which they began using in attacks in 2017.
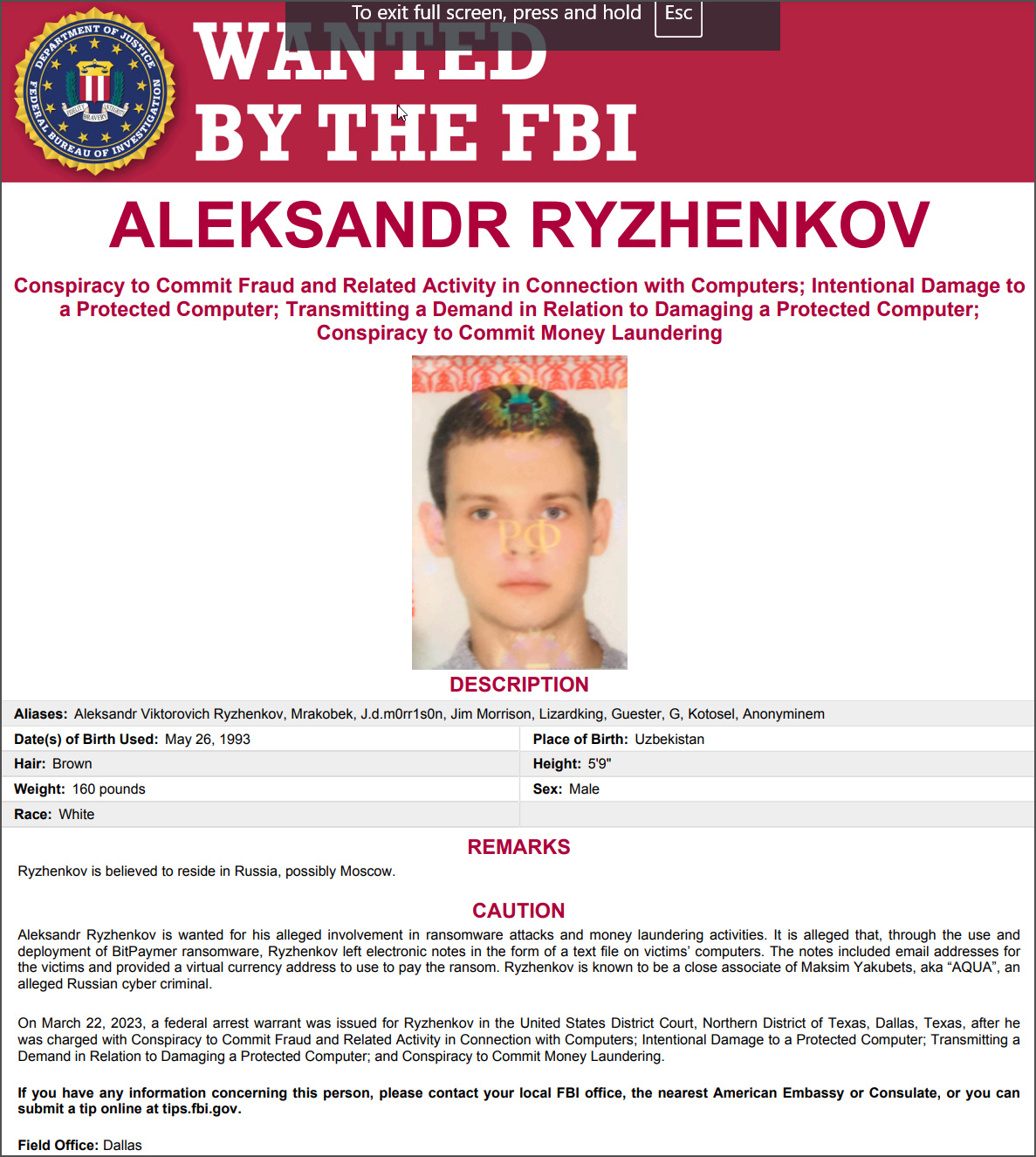
“According to the indictment, beginning in at least June 2017, Ryzhenkov allegedly gained unauthorized access to the information stored on victims’ computer networks,” reads the DOJ announcement.
“Ryzhenkov and his conspirators then allegedly deployed the strain of ransomware known as BitPaymer and used it to encrypt the files of the victim companies, rendering them inaccessible. An electronic note left on the victims’ systems contained a ransom demand and instructions on how to contact the attackers to begin ransom negotiations.
“Ryzhenkov and his conspirators allegedly demanded that victims pay a ransom to obtain a decryption key and prevent their sensitive information from being made public online.”
As part of Operation Cronos, the NCA also identified Ryzhenkov as a LockBit affiliate, under which he attacked numerous organizations.
“He has also been identified as a LockBit affiliate as part of Operation Cronos – the ongoing NCA-led international disruption of the group,” reads the NCA announcement.
“Investigators analysing data obtained from the group’s own systems found he has been involved in LockBit ransomware attacks against numerous organisations.”
Ryzhenkov is part of those sanctioned today by OFAC, the UK, and Australia and is believed to live in Russia.
Who is Evil Corp
Evil Corp is a cybercrime syndicate known for creating and distributing the Dridex banking Trojan and various ransomware families used in attacks worldwide.
When first started, the cybercrime gang used the Dridex trojan to conduct financial fraud by stealing online banking credentials and then using them to transfer funds to bank accounts under their control.
In 2017, as enterprise-targeting ransomware attacks began emerging, the gang created BitPaymer ransomware to use in attacks against companies worldwide.
In 2019, Evil Corp split, with some members creating a new ransomware operation known as DoppelPaymer, which shared much of the same code as BitPaymer. DoppelPaymer continued to attack organizations through 2022, rebranding twice as Grief (a.k.a. Pay or Grief) and Entropy ransomware.
After the US charged members of the Evil Corp for stealing over $100 million, it added the gang’s leader, Maksim Yakubets, and other members of the cybercrime gang to the Office of Foreign Assets Control (OFAC) sanction list.
Due to these sanctions, many ransomware negotiation firms refused to conduct payments with Evil Corp operations due to the risks of violating sanctions.
Evil Corp deployed new ransomware variants under different names to evade US sanctions, such as WastedLocker, Hades, Phoenix CryptoLocker, PayLoadBin, and Macaw.
However, as all of these encryptors shared a common code base, they were easily identified as belonging to Evil Corp. This led some of the gang’s affiliates to utilize the LockBit ransomware in attacks to evade sanctions further.