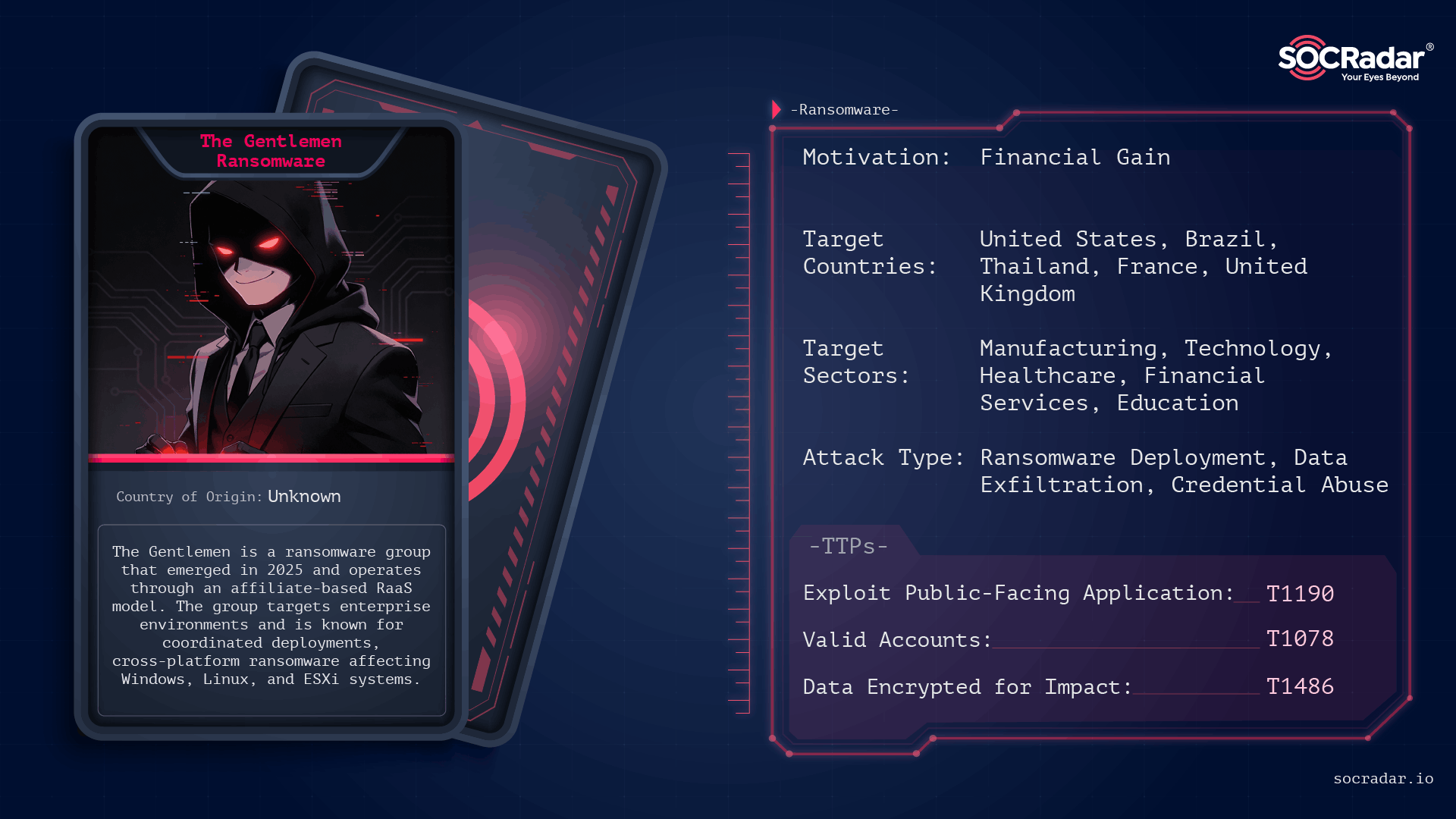
The Gentlemen is an operationally disciplined ransomware group first observed in mid-to-late 2025 that conducts double‑extortion attacks across Windows, Linux, NAS, BSD, and ESXi environments using password‑protected, operator-driven builds. Their campaigns leverage exposed internet-facing services and compromised administrative credentials, and victims have been publicly listed on a Dark Web leak site. #TheGentlemen #ESXi
Keypoints
- The Gentlemen emerged in mid-to-late 2025 and exhibits technical maturity with cross-platform ransomware families written in Go and C, including an ESXi-optimized locker.
- The group operates a double-extortion RaaS model (affiliate program offering ~90% payouts), combining data exfiltration with encryption and public leak site pressure.
- Targets are primarily medium-to-large enterprises across at least 17 countries, with manufacturing, technology, and healthcare among the most affected industries.
- Initial access commonly leverages internet-exposed services and compromised administrative credentials—examples include exposed VPN/firewall management interfaces such as FortiGate.
- Operators use legitimate utilities (PowerRun.exe), custom tools/drivers (All.exe, ThrottleBlood.sys), PsExec over SMB for lateral movement, and deploy password-protected payloads via domain resources like NETLOGON.
- Mitigations emphasize reducing external exposure, enforcing MFA and strong identity controls, monitoring Active Directory and NETLOGON activity, hardening against driver abuse, restricting common staging paths, and maintaining offline backups; SOCRadar offers monitoring and intelligence to support these defenses.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Initial access via internet-exposed services and appliance interfaces, e.g., exploiting exposed firewall/VPN management (‘exploiting internet-exposed services or compromised administrative credentials, including exposed firewall and VPN management interfaces such as FortiGate appliances.’)
- [T1078 ] Valid Accounts – Use of compromised administrative credentials for access to victim environments (‘compromised administrative credentials’)
- [T1078.002 ] Valid Accounts: Domain Accounts – Use of domain accounts and targeting domain administrators to operate within enterprise AD environments (‘Domain administrators’)
- [T1059 ] Command and Scripting Interpreter – Use of command interpreters and scripting for execution and administration tasks (‘Command and Scripting Interpreter’)
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – PowerShell used as part of execution and post-access activity (‘Command and Scripting Interpreter: PowerShell’)
- [T1059.003 ] Command and Scripting Interpreter: Windows Command Shell – Windows command shell used for execution and lateral commands (‘Command and Scripting Interpreter: Windows Command Shell’)
- [T1547 ] Boot or Logon Autostart Execution – Persistence via autostart mechanisms to maintain access (‘Boot or Logon Autostart Execution’)
- [T1136 ] Create Account – Creation of accounts to maintain access or persistence (‘Create Account’)
- [T1068 ] Exploitation for Privilege Escalation – Abuse of utilities to bypass UAC and obtain SYSTEM privileges (e.g., PowerRun.exe for UAC bypass and SYSTEM execution) (‘abuse legitimate utilities such as PowerRun.exe to bypass User Account Control (UAC) and execute processes with SYSTEM-level privileges.’)
- [T1562 ] Impair Defenses – Disabling or defeating security products via BYOVD, signed drivers, and custom terminator tools to stop antivirus/EDR processes (‘Bring Your Own Vulnerable Driver (BYOVD) abuse using signed drivers… custom tools (e.g., All.exe with ThrottleBlood.sys) to terminate antivirus and EDR processes’)
- [T1112 ] Modify Registry – Use of registry modifications as part of evasion or persistence (‘Modify Registry’)
- [T1027 ] Obfuscated Files or Information – Use of obfuscation and protected builds to hinder analysis and accidental execution (‘Obfuscated Files or Information’)
- [T1484.001 ] Domain Policy Modification: Group Policy Modification – Modification of Group Policy or NETLOGON resources to enable deployment and persistence (‘monitoring Active Directory activity, especially mass account enumeration, GPO changes, and NETLOGON modifications’)
- [T1046 ] Network Service Discovery – Network mapping using tools like Advanced IP Scanner to identify services and targets (‘maps the environment using tools like Advanced IP Scanner’)
- [T1087 ] Account Discovery – Enumeration of accounts and privileged identities to locate domain admins and privileged accounts (‘identify: Domain administrators Privileged accounts’)
- [T1087.002 ] Account Discovery: Domain Account – Discovery focused on domain accounts to support lateral movement and privilege escalation (‘Account Discovery: Domain Account’)
- [T1482 ] Domain Trust Discovery – Identification of domain trust relationships to expand access across enterprise domains (‘Domain Trust Discovery’)
- [T1021 ] Remote Services – Lateral movement using remote services such as PsExec over SMB admin shares (‘move laterally using PsExec over SMB admin shares’)
- [T1021.001 ] Remote Services: Remote Desktop Protocol – Use of RDP for remote access and lateral control (‘Remote Desktop Protocol’)
- [T1021.002 ] Remote Services: SMB/Windows Admin Shares – Use of SMB and admin shares for propagation and centralized deployment (‘PsExec over SMB admin shares’)
- [T1021.004 ] Remote Services: SSH – Use of SSH as an option for remote access in some environments (‘SSH’)
- [T1074 ] Data Staged – Staging of data prior to exfiltration to maximize extortion leverage (‘Data Staged’)
- [T1074.001 ] Data Staged: Local Data Staging – Local staging of exfiltrated data on compromised systems or shares (‘Data Staged: Local Data Staging’)
- [T1039 ] Data from Network Shared Drive – Collection of data from network shares and critical servers for exfiltration (‘Network shares and critical servers’)
- [T1048 ] Exfiltration Over Alternative Protocol – Use of non-standard or alternative channels for data exfiltration and communication (affiliates and operators coordinate through alternative channels) (‘Communication is handled primarily through TOX’)
- [T1048.001 ] Exfiltration Over Alternative Protocol: Unencrypted/Obfuscated Non-C2 Protocol – Use of non-C2 protocols for exfiltration or communication to evade detection (‘Exfiltration Over Alternative Protocol: Unencrypted/Obfuscated Non-C2 Protocol’)
- [T1071 ] Application Layer Protocol – Use of application-layer protocols for C2 and leak site communications, including web-based leak sites (‘data leak site’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – Use of web protocols for leak sites and possibly for C2/data transfer (‘Application Layer Protocol: Web Protocols’)
- [T1219 ] Remote Access Software – Use of remote-access tools and protocols for managing access and affiliate communications (‘Communication is handled primarily through TOX’)
- [T1486 ] Data Encrypted for Impact – Encryption of files across platforms to disrupt operations, using the .7mtzhh extension and dropping ransom notes (‘Encrypted files are appended with the .7mtzhh extension, and ransom notes named README-GENTLEMEN.txt are dropped’)
- [T1489 ] Service Stop – Stopping backup, database, virtualization, and security services to prevent recovery (‘Terminates backup, database, virtualization, and security services’)
- [T1552 ] Unsecured Credentials – Use and abuse of compromised or exposed credentials for access and lateral movement (‘compromised administrative credentials’)
Indicators of Compromise
- [File extension ] Encrypted files extension observed on impacted systems – .7mtzhh
- [Ransom note filename ] Ransom notes dropped across affected systems – README-GENTLEMEN.txt
- [Executable / tool names ] Tools and utilities used for escalation and lateral movement – PowerRun.exe, PsExec
- [Driver filename ] Signed/custom drivers abused for BYOVD and EDR termination – ThrottleBlood.sys
- [Network resource ] Deployment and staging via domain resources and shares – NETLOGON shares, network shares
- [Communication platforms/protocols ] Affiliate and operator communications and leak coordination – TOX, Dark Web forum posts (leak site/forum)
- [Victim names ] Organizations publicly claimed on the group’s leak site – Dongguan HYX Industrial, Rogers Capital, and other victims (e.g., Warka Bank, Solumek)
Read more: https://socradar.io/blog/dark-web-profile-the-gentlemen-ransomware/