APT28 is a long-running, GRU-linked espionage group that prioritizes stealthy credential access, targeted phishing, and long-term intelligence collection across Europe, North America, and Ukraine. Recent reporting through 2025 highlights new tooling like the LAMEHUG AI-assisted malware and sustained credential/token harvesting campaigns against services such as UKR[.]net. #APT28 #LAMEHUG
Keypoints
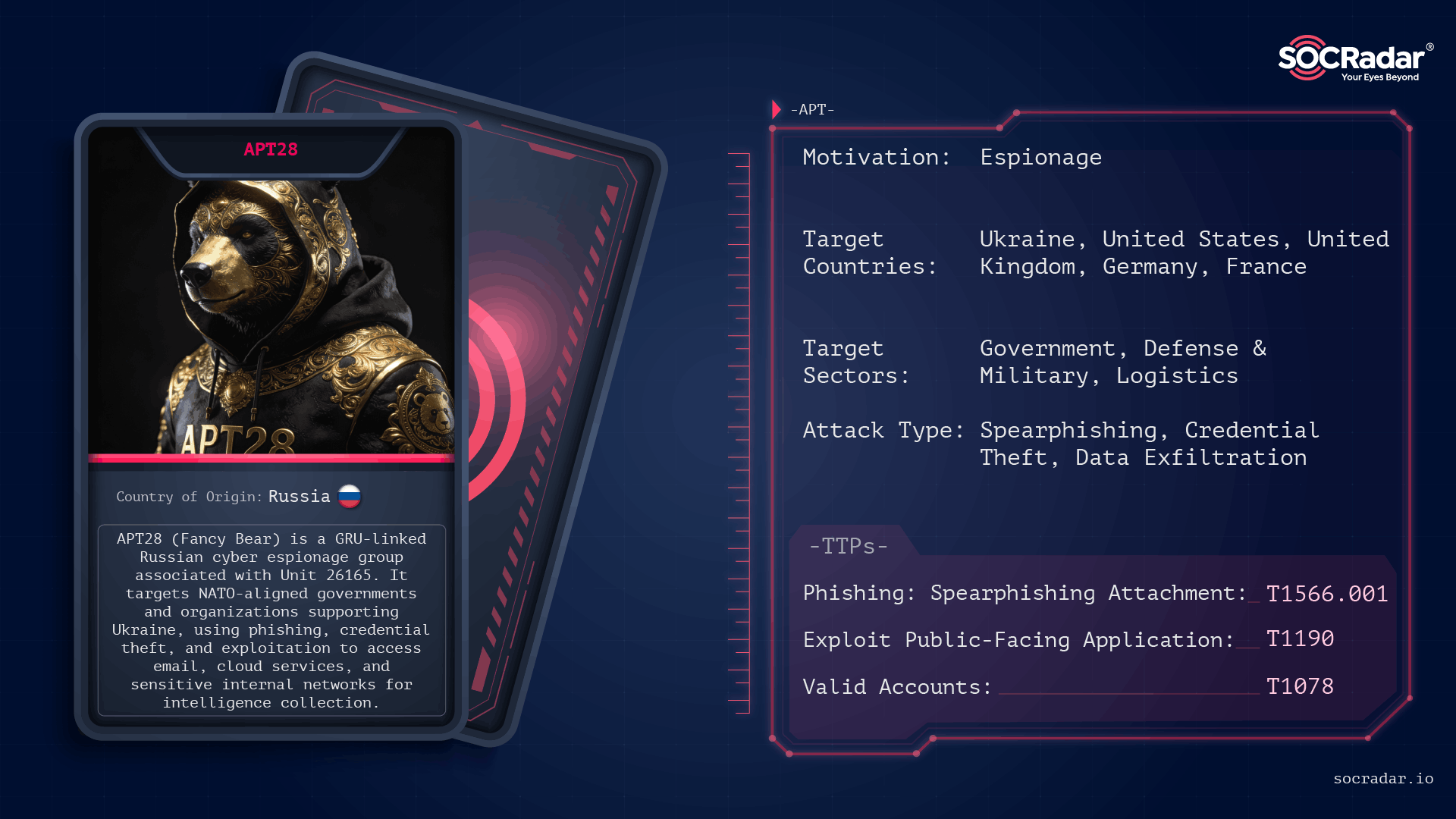
- APT28 (aka Fancy Bear, Sofacy, STRONTIUM) is widely attributed to Russia’s GRU Unit 26165 and has operated since the mid-2000s with persistent focus on intelligence collection.
- The group targets NATO members, Western supporters of Ukraine, government and diplomatic organizations, defense and logistics firms, and media/research institutions to harvest strategic intelligence.
- Initial access methods include spearphishing, malicious links/attachments, exploitation of public-facing applications, compromised accounts, and abused remote services.
- Operational tradecraft emphasizes credential theft (including OAuth tokens), covert persistence, built-in tool abuse (PowerShell, rundll32), and low-volume exfiltration over web services to avoid detection.
- Notable campaigns include LAMEHUG (2025 AI-assisted malware), credential/token theft against UKR[.]net and Microsoft cloud accounts (2024–2025), and router compromise/ reconnaissance targeting Cisco devices (2021).
- Mitigations center on identity protection (MFA, account hygiene), phishing defenses, patching exposed services and devices, monitoring for low-noise C2 and persistence, and applying threat intelligence.
MITRE Techniques
- [T1189 ] Drive-by Compromise – Used to gain initial access via web-based content and browser/client-side vectors (‘drive-by’ implied by browser- or email-based attacks and client-side exploitation).
- [T1190 ] Exploit Public-Facing Application – Exploited internet-facing services and known CVEs for entry (‘exploitation of public-facing applications, particularly webmail and edge infrastructure’).
- [T1566.001 ] Phishing: Spearphishing Attachment – Delivered ZIP archives and PyInstaller-packed executables via spearphishing attachments (‘phishing emails delivering ZIP archives with a PyInstaller-packed executable’).
- [T1598.003 ] Spearphishing Link – Phishing emails routed victims to fake login pages to harvest credentials (‘phishing emails that routed victims to fake login pages hosted on legitimate services’).
- [T1204.001 ] User Execution: Malicious Link – Users were prompted to click malicious links in targeted spearphishing (‘phishing, malicious links or attachments’).
- [T1204.002 ] User Execution: Malicious File – Malicious files (PyInstaller executables, disguised documents) required user execution to run payloads (‘a PyInstaller-packed executable disguised as a document’).
- [T1133 ] External Remote Services – Abuse of external remote services and compromised accounts to access environments (‘abused trusted relationships and compromised accounts, including cloud and email credentials’).
- [T1199 ] Trusted Relationship – Leveraged trusted third-party relationships and compromised partner accounts to appear legitimate (‘abused trusted relationships and compromised accounts’).
- [T1586.002 ] Compromise Accounts: Email Accounts – Compromised email accounts for access and phishing operations (‘compromise accounts: email accounts’ and email collection and theft repeatedly referenced).
- [T1584.008 ] Compromise Infrastructure: Network Devices – Compromised routers and network devices (Cisco) for reconnaissance and follow-on malware (‘activity against poorly maintained Cisco routers’ and ‘reconnaissance against routers globally’).
- [T1078 ] Valid Accounts – Use of valid user accounts to maintain access and blend with normal activity (‘reuse of compromised credentials’ and ‘valid accounts’).
- [T1078.004 ] Valid Accounts: Cloud Accounts – Targeting and use of cloud/email credentials and OAuth tokens to persist in cloud services (‘prompted for Microsoft cloud logins and captured credentials and OAuth tokens’).
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – Use of PowerShell to execute payloads and scripts while blending with normal activity (‘PowerShell … commonly used to run payloads and scripts’).
- [T1059.003 ] Command and Scripting Interpreter: Windows Command Shell – Use of the Windows command shell for command execution (‘the Windows command shell … commonly used to run payloads and scripts’).
- [T1203 ] Exploitation for Client Execution – Client-side exploitation in browser- or email-based attacks to execute code (‘client-side exploitation allows code to execute as soon as malicious content is rendered’).
- [T1218.011 ] System Binary Proxy Execution: Rundll32 – Abused trusted binaries such as rundll32 to run payloads (‘trusted binaries such as rundll32 are commonly used to run payloads’).
- [T1137.002 ] Office Application Startup: Office Test – Abuse of Office application startup features to execute malicious content (‘in browser- or email-based attacks, client-side exploitation’ and use of office features implied for execution patterns).
- [T1559.002 ] Inter-Process Communication: Dynamic Data Exchange – Used inter-process communication techniques in client exploitation or lateral activity (‘Inter-Process Communication … Dynamic Data Exchange’ mapping in table aligns with described client-side and execution tradecraft).
- [T1221 ] Template Injection – Use of templates or document-based injection vectors in spearphishing/document payloads (‘disguised as a document’ delivery and exploitation for client execution).
- [T1547.001 ] Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder – Persistence via registry run keys and startup entries (‘modifying logon scripts, registry run keys, scheduled tasks’).
- [T1037.001 ] Boot or Logon Initialization Scripts: Logon Script – Persistence through logon scripts and initialization scripts (‘modifying logon scripts’).
- [T1098.002 ] Account Manipulation: Additional Email Delegate Permissions – Manipulated email delegation and permissions to maintain access and stealth (‘additional email delegate permissions’ mapping and ‘account manipulation’ in persistent email-focused campaigns).
- [T1546.015 ] Event Triggered Execution: Component Object Model Hijacking – Achieved persistence and evasion via COM hijacking (‘COM objects’ modification used for persistence).
- [T1505.003 ] Server Software Component: Web Shell – Deployment of web shells on compromised infrastructure to maintain remote access (‘server-side follow-on malware deployment on devices and web-facing infrastructure’).
- [T1542.003 ] Pre-OS Boot: Bootkit – Use of advanced persistence like bootkits/rootkits as observed capability (‘Pre-OS Boot: Bootkit’ listed and capability to deploy rootkits noted in techniques).
- [T1014 ] Rootkit – Use or capability to deploy rootkits for stealth and persistence (‘Rootkit’ cited in MITRE mapping and references to deep persistence techniques).
- [T1068 ] Exploitation for Privilege Escalation – Exploited vulnerabilities to escalate privileges in target environments (‘privilege escalation may involve exploiting vulnerabilities’).
- [T1134.001 ] Access Token Manipulation: Token Impersonation/Theft – Theft and reuse of tokens and access material to escalate or impersonate users (‘captured credentials and OAuth tokens’ and ‘access token theft’).
- [T1211 ] Exploitation for Defense Evasion – Used exploitation techniques to evade detection and disable defenses (‘exploitation for defense evasion’ mapping and described avoidance of detection).
- [T1562.004 ] Impair Defenses: Disable or Modify System Firewall – Efforts to modify or impair defensive controls during intrusions (‘impair defenses’ listed and described activity to remove indicators and hamper detection).
- [T1070.001 ] Indicator Removal: Clear Windows Event Logs – Clearing logs to remove traces of activity (‘actively removes indicators of compromise, clears logs’).
- [T1070.004 ] Indicator Removal: File Deletion – Deleting artifacts and files to reduce forensic evidence (‘deletes artifacts’).
- [T1070.006 ] Indicator Removal: Timestomp – Use of timestomping or file timestamp manipulation to hide activity (‘Indicator Removal and timestomp techniques listed’).
- [T1564.001 ] Hide Artifacts: Hidden Files and Directories – Hiding files and directories to evade discovery (‘Hide Artifacts and hidden files and directories listed as evasion tactics’).
- [T1564.003 ] Hide Artifacts: Hidden Window – Use of hidden windows or UI techniques to run malicious code stealthily (‘Hidden Window’ included among defense-evasion mappings).
- [T1027.013 ] Obfuscated Files or Information: Encrypted/Encoded File – Obfuscation and encoding of payloads and staged data to avoid detection (‘Collected data is staged … often compressed and obfuscated’).
- [T1140 ] Deobfuscate/Decode Files or Information – On-host decoding/deobfuscation of stored payloads during execution (‘deobfuscate/decode files or information’ mapping supporting staged obfuscated payloads).
- [T1006 ] Direct Volume Access – Low-level access techniques for destructive or covert operations (‘Direct Volume Access’ mapped within impact/defense-evasion capabilities and disk manipulation discussion).
- [T1036 ] Masquerading – Masquerading malicious files or processes as legitimate resources to blend in (‘disguises malicious files as legitimate resources’).
- [T1036.005 ] Masquerading: Match Legitimate Resource Name or Location – Naming and placement of resources to mimic legitimate items (‘Match Legitimate Resource Name or Location’ matches the described practice of disguising artifacts).
- [T1001.001 ] Data Obfuscation: Junk Data – Use of junk data and obfuscation in exfiltration or staging to evade detection (‘Data obfuscation and compressed/obfuscated staging referenced’).
- [T1110 ] Brute Force – Brute-force and credential-guessing against webmail and services (‘brute-force activity against webmail’ described in French CERT reporting).
- [T1110.001 ] Brute Force: Password Guessing – Password guessing approaches used in account compromise efforts (‘password guessing’ category within brute-force targeting webmail/services).
- [T1110.003 ] Brute Force: Password Spraying – Password spraying employed against multiple accounts to gain access (‘password spraying’ listed as credential theft technique used by the group).
- [T1003 ] OS Credential Dumping – Dumping credentials from system memory and stores to harvest account data (‘dumping credentials from memory and directory services’).
- [T1003.001 ] OS Credential Dumping: LSASS Memory – Extraction of credentials from LSASS memory (‘OS credential dumping: LSASS memory’ listed and memory dumping described).
- [T1003.002 ] OS Credential Dumping: Security Account Manager – Harvesting credentials from the Security Account Manager (‘Security Account Manager’ listed among credential dumping variants).
- [T1003.003 ] OS Credential Dumping: NTDS – Dumping NTDS/Active Directory database for credential harvesting (‘NTDS’ included in credential dumping techniques referenced).
- [T1056.001 ] Input Capture: Keylogging – Keylogging to capture typed credentials and sensitive data (‘keylogging’ included among credential theft techniques).
- [T1040 ] Network Sniffing – Network sniffing to capture credentials and network traffic (‘network sniffing’ listed as a credential access technique).
- [T1557.004 ] Adversary-in-the-Middle: Evil Twin – Use of adversary-in-the-middle approaches like evil twin Wi‑Fi to steal credentials or intercept communications (‘Adversary-in-the-Middle: Evil Twin’ listed and Wi‑Fi reconnaissance noted).
- [T1528 ] Steal Application Access Token – Theft of application access tokens (OAuth) to maintain cloud access (‘captured credentials and OAuth tokens’ explicitly described).
- [T1550.001 ] Use Alternate Authentication Material: Application Access Token – Use of stolen tokens to authenticate and persist in cloud environments (‘captured … OAuth tokens to maintain access while blending into normal account activity’).
- [T1550.002 ] Use Alternate Authentication Material: Pass the Hash – Use of alternate authentication materials such as pass-the-hash in lateral movement and privilege operations (‘pass the hash’ mapping within credential access techniques).
- [T1589.001 ] Gather Victim Identity Information: Credentials – Targeted gathering of credentials and identity information via phishing and harvesting pages (‘aiming to capture both credentials and 2FA codes’).
- [T1083 ] File and Directory Discovery – Discovery of files and directories to locate intelligence-rich content for exfiltration (‘targeted discovery to map users, systems, processes’ and file discovery mapping).
- [T1057 ] Process Discovery – Process enumeration to understand running applications and plan actions (‘targeted discovery to map … processes’).
- [T1120 ] Peripheral Device Discovery – Discovery of peripheral devices when mapping systems during reconnaissance (‘Peripheral Device Discovery’ listed among discovery techniques).
- [T1016.002 ] System Network Configuration Discovery: Wi-Fi Discovery – Wi‑Fi discovery and mapping of network configuration as part of reconnaissance (‘Wi-Fi Discovery’ and Wi‑Fi networks listed in reconnaissance).
- [T1596 ] Search Open Technical Databases – Searching open technical databases to gather target information (‘Search Open Technical Databases’ listed and discovery includes open-source information collection).
- [T1591 ] Gather Victim Org Information – Collection of organizational information to inform targeting and follow-on operations (‘Gather Victim Org Information’ aligns with intelligence-driven targeting described).
- [T1669 ] Wi-Fi Networks – Reconnaissance and exploitation of Wi‑Fi networks as part of environmental mapping (‘Wi‑Fi Networks’ included in discovery/reconnaissance mapping).
- [T1210 ] Exploitation of Remote Services – Exploiting remote services (RDP, SMB, other remote services) for lateral movement (‘Lateral movement is typically achieved through remote services such as RDP or SMB’).
- [T1021.001 ] Remote Services: Remote Desktop Protocol – Use of RDP for lateral movement and pivoting (‘Remote Desktop Protocol’ explicitly referenced as a lateral movement method).
- [T1021.002 ] Remote Services: SMB/Windows Admin Shares – Use of SMB and admin shares to move laterally and access data (‘SMB’ and Windows admin shares used for lateral movement).
- [T1091 ] Replication Through Removable Media – Use of removable media for replication or data transfer in certain campaigns (‘Replication Through Removable Media’ included among lateral movement techniques and data staging).
- [T1119 ] Automated Collection – Automated collection of emails, documents, and repositories for targeted intelligence gathering (‘Data collection focuses on emails, documents, shared repositories, screenshots’).
- [T1213 ] Data from Information Repositories – Targeted collection from information repositories like shared drives and cloud stores (‘collection focuses on … shared repositories’).
- [T1213.002 ] Data from Information Repositories: Sharepoint – Targeting SharePoint and similar repositories to harvest documents (‘Data from Information Repositories: Sharepoint’ explicitly listed).
- [T1005 ] Data from Local System – Collection of local system files and documents for exfiltration (‘Data from Local System’ and staging described for local collection).
- [T1039 ] Data from Network Shared Drive – Harvesting files from network shares and shared drives (‘Data from Network Shared Drive’ listed and network share collection described).
- [T1025 ] Data from Removable Media – Collection of data from removable media when applicable (‘Data from Removable Media’ included in collection mappings).
- [T1113 ] Screen Capture – Use of screenshots to capture contextual information from compromised systems (‘Screen Capture’ listed among collection techniques used to gather intelligence).
- [T1114.002 ] Email Collection: Remote Email Collection – Remote collection of email via compromised accounts or mail access (‘Email Collection: Remote Email Collection’ and repeated focus on email access and exfiltration).
- [T1560 ] Archive Collected Data – Archiving and compressing collected data prior to exfiltration (‘Collected data is staged locally or remotely, often compressed and obfuscated before exfiltration’).
- [T1560.001 ] Archive via Utility – Use of utilities to archive and compress data for staging and exfiltration (‘Archive via Utility’ implied by compressed staging behavior described).
- [T1074.001 ] Data Staged: Local Data Staging – Local staging of collected documents prior to exfiltration (‘Collected data is staged locally or remotely’).
- [T1074.002 ] Data Staged: Remote Data Staging – Remote staging on infrastructure controlled by the actor for later exfiltration (‘staged locally or remotely’ described in collection/exfiltration section).
- [T1071.001 ] Application Layer Protocol: Web Protocols – Use of standard web protocols for C2 and exfiltration to blend with legitimate traffic (‘Communications often occur over standard web and mail protocols’).
- [T1071.003 ] Application Layer Protocol: Mail Protocols – Use of mail protocols for command-and-control or data movement to blend in (‘Communications often occur over … mail protocols’).
- [T1102.002 ] Web Service: Bidirectional Communication – Use of web services and cloud channels for bidirectional C2 and control (‘cloud-based or proxy infrastructure’ and ‘Web Service: Bidirectional Communication’ mapped to C2 patterns).
- [T1090.001 ] Proxy: Internal Proxy – Use of internal proxying to obscure traffic flows (‘internal proxy’ mapping and use of layered proxies to obscure malicious traffic).
- [T1090.002 ] Proxy: External Proxy – Use of external proxies and rented infrastructure to hide origin (‘external proxy’ and rented servers/VPNs/free hosting used to stay flexible and harder to track’).
- [T1090.003 ] Proxy: Multi-hop Proxy – Multi-hop proxying through chained infrastructure to complicate attribution (‘Multi-hop Proxy’ referenced by use of layered proxies and rented infrastructure).
- [T1573.001 ] Encrypted Channel: Symmetric Cryptography – Use of encrypted channels for C2 and exfiltration to avoid inspection (‘encrypted channels’ and controlled, low-volume exfiltration described).
- [T1105 ] Ingress Tool Transfer – Transfer of tools and malware into target environments following reconnaissance (‘follow-on malware deployment on some devices’ and ingress tool transfer mapping).
- [T1092 ] Communication Through Removable Media – Use of removable media as a comms or transfer mechanism in some lateral/collection contexts (‘Communication Through Removable Media’ included in C2/exfiltration mappings).
- [T1048.002 ] Exfiltration Over Alternative Protocol – Exfiltration using alternative protocols or channels to bypass controls (‘exfiltration typically occurs over web services or alternative encrypted channels’).
- [T1567 ] Exfiltration Over Web Service – Use of web services for data exfiltration to blend with normal traffic (‘exfiltration typically occurs over web services’).
- [T1030 ] Data Transfer Size Limits – Controlled, low-volume exfiltration to avoid detection by size-based thresholds (‘low-volume manner to avoid detection’ in exfiltration description).
- [T1561.001 ] Disk Content Wipe: Disk Content Wipe – Capability to wipe or destroy disk content when objectives require disruption (‘the group has demonstrated the capability to wipe disks’).
- [T1498 ] Network Denial of Service – Ability to perform network denial or disruption when aligned with operational objectives (‘Network Denial of Service’ listed under impact capabilities).
- [T1595.002 ] Active Scanning: Vulnerability Scanning – Active scanning and reconnaissance for vulnerable services and devices (‘reconnaissance against routers globally’ and vulnerability scanning mapping).
- [T1598 ] Phishing for Information – Use of phishing to harvest credentials, 2FA codes, and information (‘phishing for information’ and credential harvesting via fake login pages documented).
- [T1583.001 ] Acquire Infrastructure: Domains – Acquisition of domains for phishing and hosting landing pages (‘acquire infrastructure: domains’ and use of domains and hosted pages for credential collection).
- [T1583.003 ] Acquire Infrastructure: Virtual Private Server – Use of VPS and rented servers to host infrastructure and C2 (‘rented servers, VPN services, and free hosting to stay flexible and harder to track’).
- [T1583.006 ] Acquire Infrastructure: Web Services – Use of web services and legitimate hosting for phishing and staging (‘fake login pages hosted on legitimate services’ and ‘web services’ for C2/exfiltration).
- [T1588.002 ] Obtain Capabilities: Tool – Development or acquisition of tooling (e.g., LAMEHUG, AUTHENTIC ANTICS) to support dynamic collection and operations (‘LAMEHUG … malware framework’ and ‘AUTHENTIC ANTICS’ attribution).
Indicators of Compromise
- [Malware ] campaign-specific samples – LAMEHUG (AI-assisted malware framework used in 2025), AUTHENTIC ANTICS (credential-capturing malware attributed to APT28).
- [Domain ] credential-phishing landing pages – UKR[.]net impersonation and fake login pages hosted on legitimate services used to harvest credentials and 2FA codes.
- [Vulnerability ] exploited for initial access – CVE-2017-6742 (Cisco router issue exploited in 2021), CVE-2023-23397 (exploitation path cited in French CERT reporting).
- [File ] delivery artifacts – PyInstaller-packed executable inside ZIP archives disguised as documents, and malicious attachments used in spearphishing campaigns.
- [Infrastructure ] hosting & proxies – Rented servers, VPN services, and free hosting used as flexible C2 and phishing infrastructure.
- [Network device ] router reconnaissance/compromise – Poorly maintained Cisco routers abused via SNMP and known vulnerabilities to collect device/network details (and follow-on malware on some devices).
- [Account/credentials ] targeted account types – Cloud and email credentials plus OAuth tokens harvested (example: Microsoft cloud logins and captured OAuth tokens), and stolen credentials for UKR[.]net users.