0APT surfaced in late January 2026 as a Ransomware-as-a-Service operation claiming hundreds of high-profile victims worldwide but rapid analysis has cast doubt on its technical capability. Evidence such as 0-byte dummy files, low-quality code and developer comments in Hindi/Urdu suggest 0APT may be a scam-as-a-service rather than a sophisticated ransomware cartel. #0APT #SolsticeEnergyGrid
Keypoints
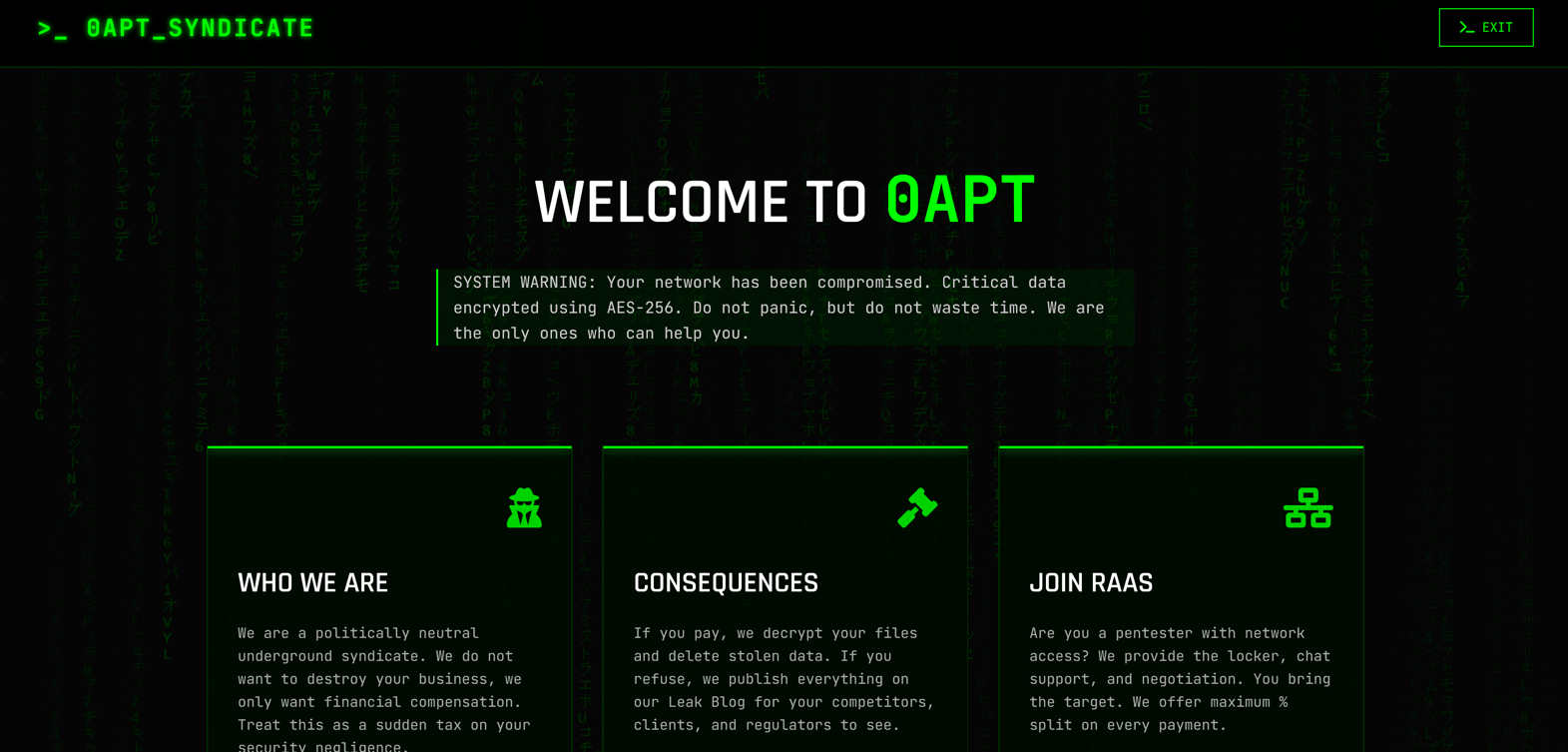
- 0APT emerged publicly around January 28, 2026, quickly listing hundreds of alleged victims on a dark web leak site, claiming a global, politically neutral criminal syndicate.
- The group targets a broad range of sectors—critical infrastructure, healthcare, finance, manufacturing, and logistics—appearing opportunistic and volume-focused rather than specialized.
- 0APT claims to use hybrid encryption (AES-256 plus Salsa20) and a high-volume “Wall of Shame” leak site to pressure victims into paying ransoms.
- Technical analysts found multiple anomalies—prevalence of 0-byte leaked files, low-quality/AI-generated code, and developer comments in Hindi/Urdu—undermining the group’s credibility.
- Operational tradecraft includes Session Messenger for negotiations and a Tor-based leak site, emphasizing anonymity and psychological pressure over demonstrable technical exfiltration.
- Defensive guidance stresses “Verify then React”: validate leaked data, check internal logs for outbound exfiltration and encryption events, patch internet-facing services, enforce MFA, and segment critical assets like SCADA.
MITRE Techniques
- [T1595.002 ] Vulnerability Scanning – Used to find opportunistic targets at scale with automated tools; quote: ‘likely leveraging automated vulnerability scanners to identify weak points in diverse infrastructures.’
- [T1486 ] Data Encrypted for Impact – Claimed use of hybrid cryptography to encrypt victim data as extortion leverage; quote: ‘they purportedly utilize AES-256 … often supplemented by the Salsa20 algorithm to increase speed when processing large data streams or backups.’
- [T1102 ] Web Service – Use of third‑party/decentralized messaging and web services for attacker communications and leak publication; quote: ‘0APT prefers Session Messenger for all negotiations’ and ‘Wall of Shame on their Tor leak site.’
- [T1041 ] Exfiltration Over C2 Channel (Network Exfiltration) – Allegations of stolen data and guidance to check for massive outbound traffic indicate attempted or claimed data exfiltration; quote: ‘verify internal network logs for evidence of large-scale data exfiltration (e.g., massive outbound traffic) … before assuming a breach has occurred.’
Indicators of Compromise
- [Victim Organizations ] Named alleged targets used as indicators/listing context – Solstice Energy Grid, Mayo Clinic, and other high-value organizations.
- [Dark Web Leak Site / Domain ] Leak publication and negotiation platforms – Tor-based “Wall of Shame” leak site (Tor .onion) and DLS leak site references.
- [File Samples ] Evidence from provided leaks indicating possible fabrication – 0-byte dummy files found in leaked data samples (many empty files).
- [Source Code Artifacts ] Development artifacts pointing to regional origin – developer comments in Hindi/Urdu found in leak site source code.
- [Communication Channel ] Attacker negotiation platform – Session Messenger cited as the preferred channel for negotiations and OPSEC.
Read more: https://socradar.io/blog/dark-web-profile-0apt-ransomware/