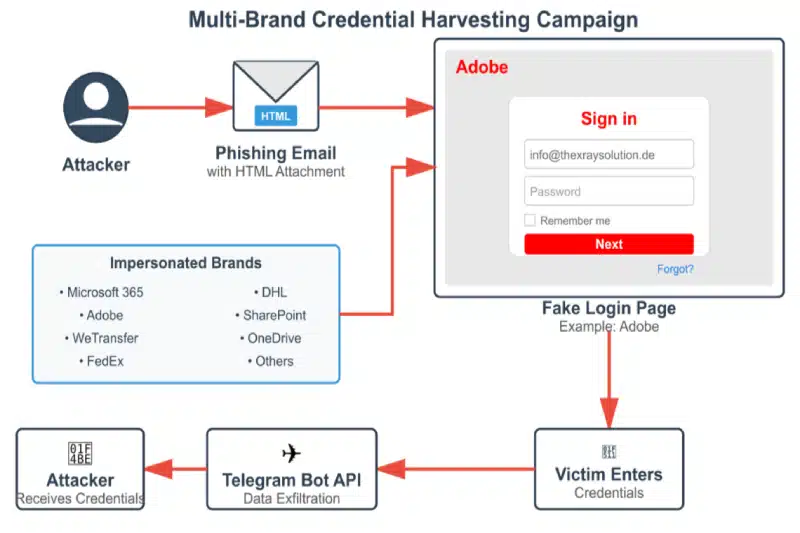
Cybersecurity researchers at Cyble have uncovered a sophisticated phishing campaign in Central and Eastern Europe that uses malicious HTML attachments to steal credentials without relying on external hosting servers. The attack employs convincing fake login pages and embeds JavaScript to exfiltrate data via Telegram bots, bypassing traditional security measures. #PhishingCampaign #CredentialTheft #TelegramBots #HTMLAttachments #CRIL
Keypoints
- The campaign targets organizations across multiple industries in Central and Eastern Europe, including manufacturing, government, and energy sectors.
- Attackers use HTML attachments with embedded JavaScript that impersonate trusted brands like Adobe, Microsoft, FedEx, and DHL to deceive victims.
- The malware employs advanced obfuscation techniques, including CryptoJS AES encryption and anti-forensics measures like disabling developer tools.
- The operation uses Telegram bots to transmit captured credentials, making detection more difficult for security systems.
- Organizations should scrutinize HTML email attachments and monitor network traffic to Telegram API endpoints for signs of compromise.
Read More: https://thecyberexpress.com/phishing-telegram-bots-steal-credentials/