Microsoft Security Copilot augments Microsoft Defender capabilities to help security teams investigate web shell and post-compromise incidents by analyzing obfuscated or encoded scripts and accelerating triage. Defender coverage and prebuilt/hunting queries target cron-based persistence, PHP webshells (e.g., index.php), base64-encoded payloads, and hosting-control-panel abuse to detect and block threats. #WebShell #MicrosoftSecurityCopilot
Keypoints
- Microsoft Security Copilot can assist analysts in decoding and interpreting obfuscated or heavily encoded scripts to speed incident triage and reveal attacker tradecraft.
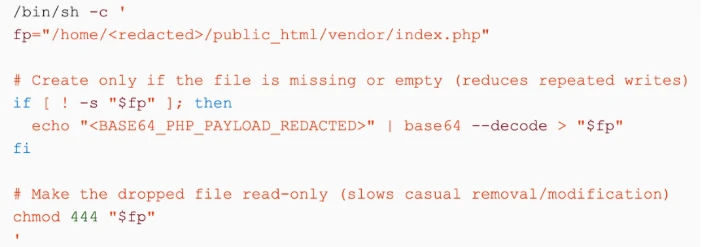
- Attackers in this campaign used exposed web applications and hosting environments (e.g., cPanel/jailshell) to gain access and deploy server-side tooling such as PHP webshells.
- Persistence was achieved via web-accessible PHP files (for example, index.php) and scheduled cron jobs, including short-interval (one-minute) recurring tasks.
- Obfuscation and inline encoded payloads (high-entropy strings, base64 blobs) were used to evade detection and were decoded at runtime (e.g., echo
| base64 -d > ). - Microsoft Defender for Endpoint and Defender Antivirus detect suspicious script execution, cron job creation, modified web files/permissions, and blocked active WebShell and Obfuse samples.
- Microsoft provides prebuilt Security Copilot promptbooks and Defender XDR advanced-hunting queries (DeviceProcessEvents-based) to investigate web server spawning shells, base64 PHP writes, tee-based writes, cPanel abuse, and combined high-risk patterns.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Attackers gain access through exposed web applications or hosting environments to introduce server-side tooling (‘Attackers gain access through exposed web applications or hosting environments and use that access to introduce server-side tooling that blends into the web stack.’)
- [T1505.003 ] Server Software Component: Web Shell – A PHP webshell placed in a web-accessible location to enable long-term access via HTTP requests (‘A PHP webshell is placed in a web-accessible location and designed to remain dormant during normal traffic, enabling long-term access through web requests.’)
- [T1027 ] Obfuscated/Encrypted File or Information – Payloads and scripts are obfuscated or encoded (high-entropy strings, base64) to evade inspection (‘Payloads and scripts are obfuscated or encoded (for example, high-entropy strings and base64-encoded blobs) to reduce inspection and evade simple content-based detections.’)
- [T1140 ] Deobfuscate/Decode Files or Information – Attackers decode inline payloads at runtime using commands like base64 -d to reconstruct PHP content on disk (‘Attackers decode inline payloads at runtime, such as echo
| base64 -d > to reconstruct PHP content on disk with minimal interactive footprint.’) - [T1105 ] Ingress Tool Transfer – Additional files or second-stage scripts are retrieved using ingress utilities such as curl or wget and written into web directories (‘Additional files or second-stage scripts are retrieved using file ingress utilities such as curl or wget, often writing directly into web directories or application paths.’)
- [T1059.004 ] Command and Scripting Interpreter: Unix Shell – Web-facing workloads spawn shell interpreters (sh, bash, dash) to execute attacker-provided commands from webshell logic (‘Web-facing workloads (for example, php-fpm, apache2, nginx) spawn shell interpreters (sh, bash, dash) to execute attacker-provided commands from webshell logic or injected requests.’)
- [T1053.003 ] Scheduled Task/Job: Cron – Persistence established via cron jobs, including those created by hosting tooling like cPanel and one-minute recurring loops (‘Persistence is established via cron, including jobs created by hosting tooling (for example, cPanel) and recurring execution patterns (including short intervals such as one-minute loops).’)
- [T1222.002 ] File and Directory Permissions Modification – File or directory permissions are modified to allow write/execute access in web paths to maintain persistence artifacts (‘File or directory permissions are modified to enable write/execute access in web paths or to ensure persistence artifacts remain accessible to the compromised runtime context.’)
Indicators of Compromise
- [File names ] web-accessible and server-side script artifacts – index.php, other .php files
- [Process / Service names ] initiators of suspicious activity – php-fpm, httpd (and other web servers like apache2, nginx)
- [Command-line patterns ] evidence of encoding/decoding and file writes – ‘echo
| base64 -d > ‘, use of ‘base64’ and ‘tee’ to write .php files - [Malware / detection names ] blocked active samples identified by Defender – ‘WebShell’, ‘Obfuse’
- [Scheduled tasks ] persistence via cron entries and recurring execution patterns – creation of cron jobs by hosting control panels (cPanel/jailshell), and repeated 1-minute cron patterns