This article analyzes fundamental architectural flaws in Apache HTTP Server, revealing new classes of “Confusion Attacks” that exploit semantic ambiguities among internal data structures to bypass security controls. The research uncovers multiple vulnerabilities, exploitation techniques, and practical impacts on Apache HTTP Server, urging administrators and developers to carefully examine and patch their systems. #ApacheHTTPServer
Keypoints
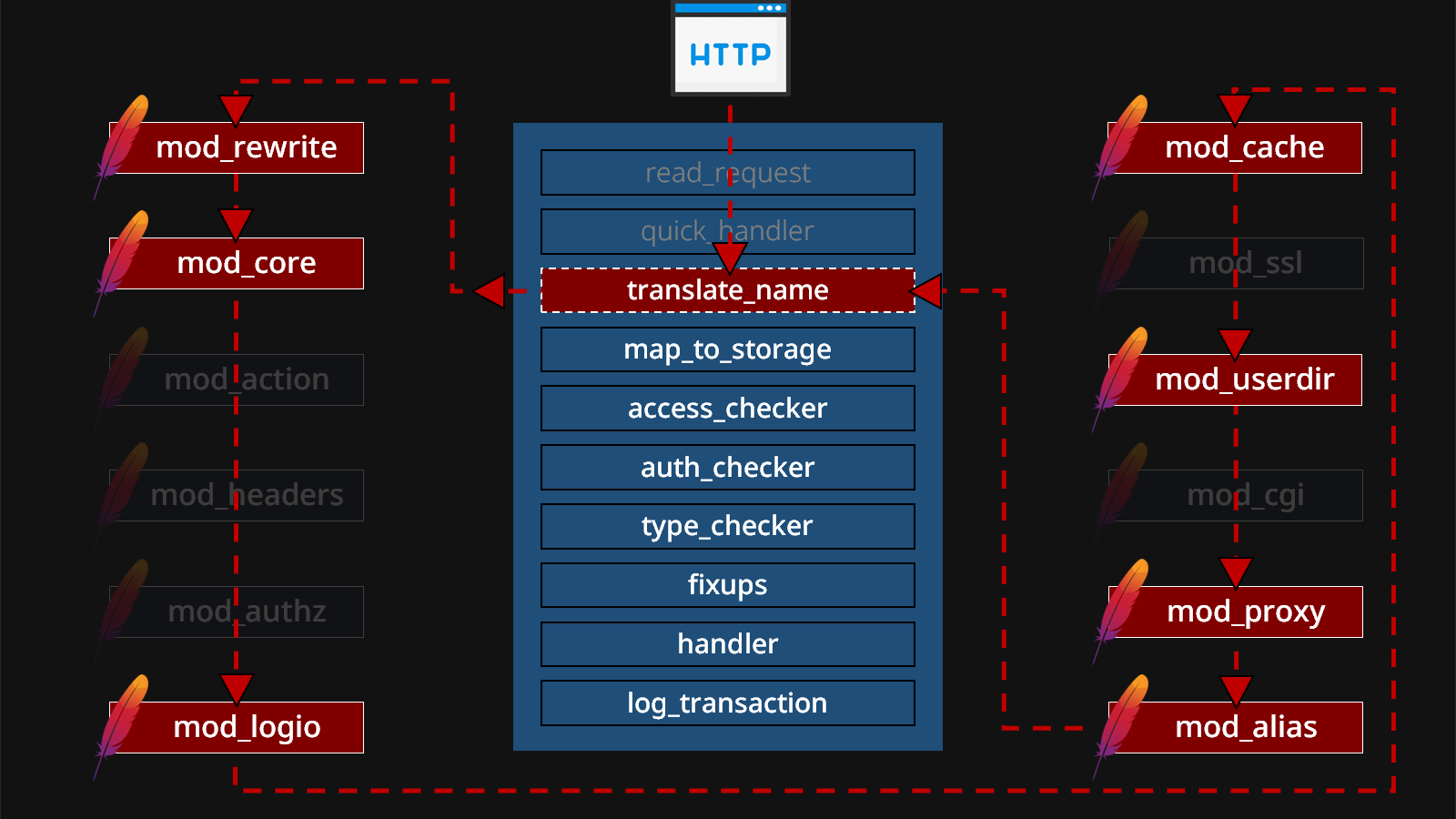
- Apache HTTP Server’s modular design relies on hundreds of loosely coordinated modules sharing a massive structure, leading to inconsistent interpretations of key fields such as filename, DocumentRoot, and handler.
- Three types of Confusion Attacks were identified: Filename Confusion (truncation and ACL bypass), DocumentRoot Confusion (arbitrary file access and local gadget manipulation), and Handler Confusion (handler overwriting and arbitrary handler invocation).
- These attacks exploit discrepancies in how modules treat fields like r->filename and r->content_type, allowing bypasses of authentication, access controls, information disclosure, XSS, SSRF, and remote code execution (RCE).
- Nine new CVEs were reported and patched in Apache HTTP Server 2.4.60, addressing vulnerabilities such as Windows UNC-based SSRF, mod_proxy encoding issues, and unsafe RewriteRule behaviors.
- Unsafe RewriteRules can be manipulated to access the entire filesystem, leak server-side source code, perform local file inclusion (LFI), SSRF, and escalate to RCE using local symbolic links or gadgets within default OS directories.
- Handler Confusion leverages legacy code that conflates media type with handler semantics, enabling attackers to overwrite handlers, induce double responses, or trigger internal server redirects to invoke arbitrary module handlers.
- Mitigations have been actively released (e.g., by Akamai) but patching remains complex because of backward-compatibility issues in existing deployments.
MITRE Techniques
- [T1505] Server Software Component Exploitation – Exploited inconsistencies in Apache HTTP Server’s modular design and internal data fields to bypass controls (‘…different components interpret r->filename or r->content_type inconsistently causing ACL bypass and handler confusion…’).
- [T1105] Ingress Tool Transfer – Leveraged local gadgets and symbolic links in OS directories to access and manipulate server-side scripts and configurations (‘…accessing /usr/share/doc/phpinfo.php or symbolic links allowing escape from /usr/share…’).
- [T1559] Inter-Process Communication – Utilized mod_proxy and FastCGI communication with backend services (like PHP-FPM) for authentication bypass and remote command execution (‘…proxy:fcgi://127.0.0.1/… allowing crafted requests to bypass authentication and execute code…’).
- [T1176] Browser Session Hijacking – Exploited cross-site scripting (XSS) through OS-provided files via unsafe RewriteRules (‘…LibreOffice help files manipulated to achieve XSS…’).
- [T1499] Exploit Public-Facing Application – Targeted Apache HTTP Server vulnerabilities like CVE-2024-38472 (Windows UNC SSRF) and CVE-2024-39573 (RewriteRule SSRF) to conduct remote exploits (‘…using UNC paths to coerce NTLM authentication and SSRF to attacker-controlled servers…’).
- [T1189] Drive-by Compromise – Demonstrated the risk of modular misuse whereby attacker-controlled URL parameters combined with legacy behaviors resulted in source code disclosure and RCE (‘…mod_security error causing content-type overwrite revealing PHP source code…’).
- [T1221] Template Injection – Invoked arbitrary module handlers via CGI server-side redirects and controlled headers to run malicious payloads (‘…mod_cgi internal redirects using crafted Location and Content-Type headers to invoke handlers leading to RCE…’).
Indicators of Compromise
- [File Names] vulnerable RewriteRule examples and CGI scripts – phpinfo.php, admin.php, adminer.php, proxy.php, magpie_debug.php, pearcmd.php (used in SSRF and RCE demonstrations)
- [CVE Identifiers] – CVE-2024-38472 (Windows UNC SSRF), CVE-2024-39573 (RewriteRule SSRF), CVE-2024-38477, CVE-2024-38476, CVE-2024-38475, CVE-2024-38474, CVE-2024-38473, CVE-2023-38709 (HTTP response splitting)
- [HTTP Requests] crafted URLs with encoded question marks or CRLF injection – examples such as /admin.php%3Fooo.php, /upload/1.gif%3fooo.php, /cgi-bin/redir.cgi?r=http://%0d%0aLocation:/ooo%0d%0aContent-Type:server-status%0d%0a
- [Symbolic Links] notable local links leveraged for privilege escalation – /usr/share/cacti/site/ -> /var/log/cacti/, /usr/share/solr/data/ -> /var/lib/solr/data, /usr/share/redmine/instances/ -> /var/lib/redmine/