Check Point Research found China-linked hackers, including the Camaro Dragon group, targeting Qatar with conflict-themed lures that deliver backdoors like PlugX and loaders that lead to Cobalt Strike deployment. The campaign abuses DLL hijacking in Baidu NetDisk and hides a Rust-written loader inside NVDA components to hit Qatar’s military and energy sectors during heightened regional tensions. #CamaroDragon #PlugX
Keypoints
- China-linked actors, including Camaro Dragon, began targeting Qatar on 1 March 2026, timed with Operation Epic Fury.
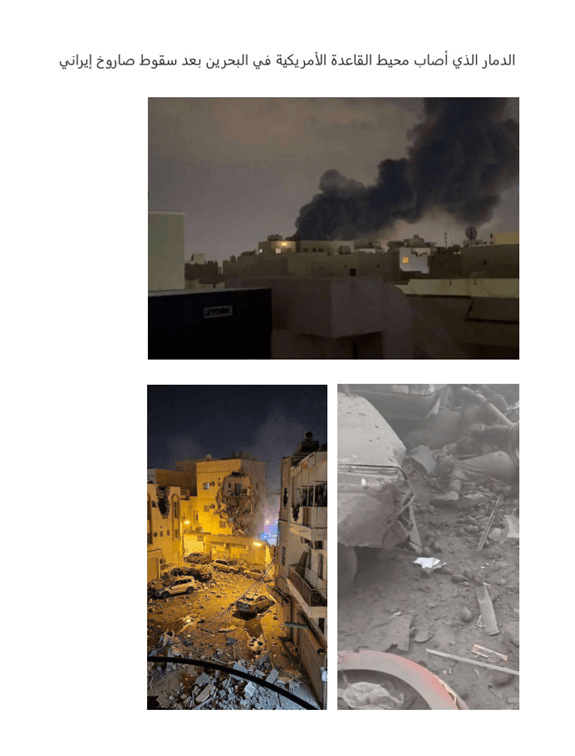
- Attackers used news-themed lures, such as fake photos and crisis headlines, to entice victims into opening malicious files.
- The infection chain used DLL hijacking in Baidu NetDisk to deploy the PlugX backdoor for data theft and surveillance.
- A password-protected ZIP delivered a Rust-written loader concealed in NVDA components to ultimately plant Cobalt Strike in energy sector networks.
- Other state-linked groups like MuddyWater were also active, deploying a new strain dubbed DinDoor against U.S. and Israeli targets amid the conflict.
Read More: https://hackread.com/china-hackers-qatar-backdoor-fake-war-news/