This video explains the importance of strategic prioritization when managing limited resources and how to determine which tasks to focus on first. It emphasizes the concept of strategic refusal to effectively allocate resources. #Strategy #Prioritization
Category: Youtube
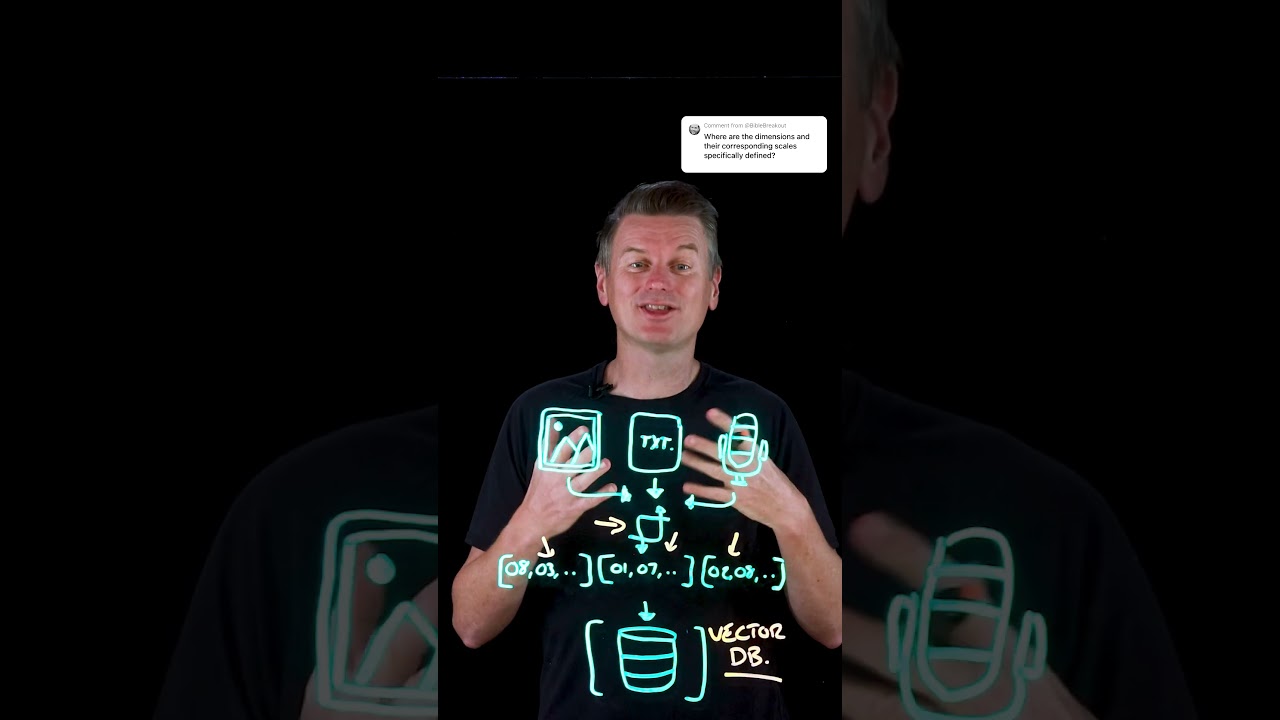
This video explains how vector databases store data as high-dimensional vectors created through embedding models, enabling semantic similarity searches. It discusses how these vectors lack predefined dimensions and are interpreted holistically rather than through individual attributes. #VectorDatabase #EmbeddingModels

This update discusses recent developments in the CVE program, including funding concerns and the emergence of the European Vulnerability Database (EUVD) by ENISA. The EUVD was established to improve vulnerability management within the framework of the EU’s NIS-2 cybersecurity directives, complementing the CVE program. #CVE #EUVD #ENISA

This episode of Behind the Binary podcast features Microsoft security researcher Thomas Roachchia, discussing the future of cybersecurity, AI, and data visualization. The episode also covers the unprotect project, focusing on malware analysis and anti-analysis techniques. #CyberSecurity #AI #DataVisualization #MalwareResearch
This video discusses the evolution of AI benchmarking, emphasizing the shift towards evaluating AI agents in a more comprehensive way. It suggests combining general reasoning tests with domain-specific performance metrics to better assess AI capabilities.
This video discusses the persistent challenges in cybersecurity, highlighting issues like human error, ransomware, and third-party vulnerabilities. It advocates for a new, risk-driven approach starting at the executive level to improve cybersecurity effectiveness.
This video discusses recent cybercriminal activity involving data breaches at Coinbase and ransomware gangs like Lockbit, highlighting the dangers of hacking and social engineering. It also covers the risks of paying ransoms, with examples from ransomware incidents affecting schools and companies.
This video emphasizes the importance of handling Personally Identifiable Information (PII) with utmost care to prevent breaches. It highlights recent incidents where startups, despite being resource-constrained, faced significant security failures.
This episode of Security Weekly covers the latest cybersecurity news, including recent vulnerabilities, legal updates, and the impact of AI on education and industry. The host discusses emerging threats, policy changes, and technological debates shaping the cybersecurity landscape.
This video explains why certain IP addresses, specifically those in the range 224 to 239, cannot be assigned to a laptop’s network interface. It also covers the concept of multicast addresses and the related IP address classifications based on RFC standards.
This episode discusses the global competition in AI development, highlighting Europe’s position and Mistral’s recent advancements. It also explores AI infrastructure investments in Saudi Arabia, evolving AI benchmarks, and the future of personalized generative advertising.
This episode covers recent security news including Android Lockdown Mode, vulnerabilities in routers and firmware, and tech from the latest firmware exploits to AI-powered reverse engineering. The hosts discuss the evolving landscape of cybersecurity threats, vulnerabilities in hardware and software, and the importance of resilient infrastructure and standards in the industry.
A former Disney employee maliciously accessed company servers, altering restaurant menus by removing allergen warnings, adding profanity, and renaming items with obscene language. He was sentenced to three years in prison for his actions, highlighting the serious consequences of such cyber misconduct.
This video explores the emergence of agentic AI, systems capable of setting goals, making decisions, and acting autonomously. It emphasizes the importance of effective governance to manage the increased risks associated with advanced AI capabilities.
This podcast emphasizes the critical importance of understanding how to secure systems in cybersecurity roles. It covers practical skills, resources, and the role of AI in improving system security and defense strategies.
