North Korea’s BlueNoroff has run a financially motivated campaign targeting cryptocurrency executives by luring them into fake Zoom meetings populated with AI-generated avatars and stolen webcam footage to deliver malware. Arctic Wolf found attackers exfiltrating victims’ webcam video to create increasingly convincing deepfake meetings and using typo‑squatted links and a fake Zoom SDK update prompt to achieve rapid compromise and credential and wallet theft. #BlueNoroff #ArcticWolf
Keypoints
- BlueNoroff targets cryptocurrency executives with fake Zoom meetings using AI avatars and stolen webcam footage.
- Attackers siphon victims’ webcam feeds in real time to build a self-reinforcing deepfake production pipeline.
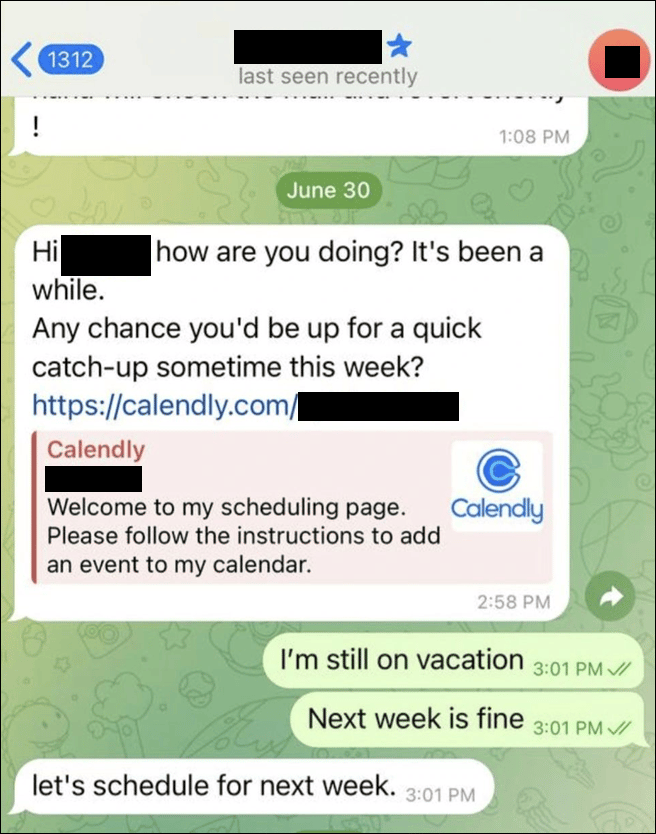
- Initial lures include compromised Telegram accounts, Calendly invites, and typo‑squatted calendar links that replace legitimate meeting URLs.
- A fake Zoom SDK update prompt installs payloads that enable persistence, credential harvesting, wallet theft, and Telegram session theft within minutes.
- Organizations should verify meeting requests via secondary channels, restrict webcam and microphone access, and monitor for credential, clipboard, and PowerShell abuse.