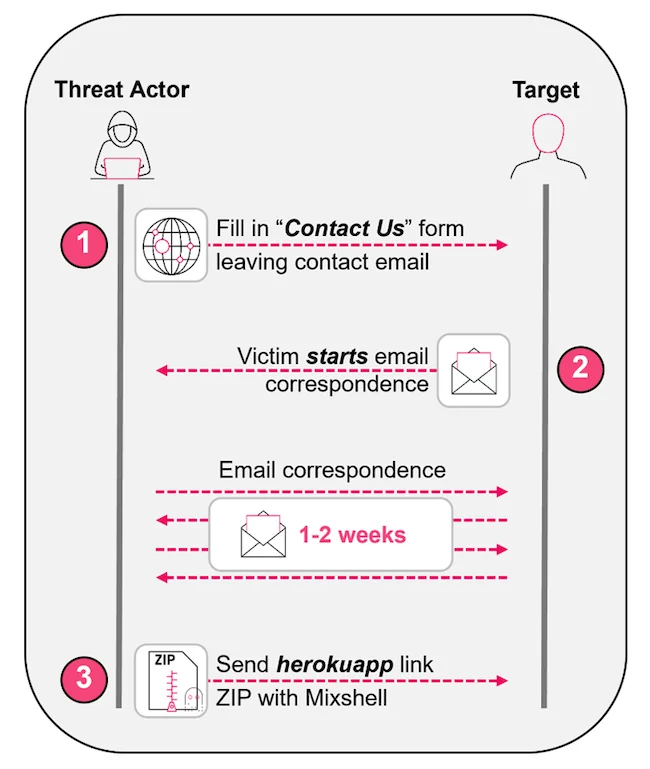
A sophisticated phishing campaign targeting industrial and supply chain companies uses trusted contact forms and professional communication to deceive victims. The attackers deliver malicious ZIP archives with PowerShell scripts, employing DNS TXT tunneling for command and control. #MixShell #Herokuapp
Keypoints
- The campaign is conducted by financially motivated threat actors aiming to infect organizations with a custom backdoor called “MixShell.”
- Attackers utilize legitimate-looking domains and long-term engagement strategies to build trust with victims.
- Malicious files are delivered through subdomains of herokuapp.com after establishing credibility via email or contact forms.
- Recent phishing emails incorporate AI-driven operational change themes, increasing their relevance and perceived importance.
- The campaign predominantly targets U.S. organizations across multiple sectors, including enterprise and SMB levels.
Read More: https://www.helpnetsecurity.com/2025/08/29/phishing-manufacturing-supply-chain/