APT Sidewinder ran widespread spear-phishing campaigns impersonating government and defense portals in Bangladesh, Nepal, and Turkey, using Netlify/Pages.dev-hosted fake Zimbra and secure-portal pages to harvest credentials. Centralized credential collection domains mailbox3-inbox1-bd.com and mailbox-inbox-bd.com (resolving to 146.70.118.226) indicate reused backend infrastructure and redundancy. #Sidewinder #mailbox3-inbox1-bd.com
Keypoints
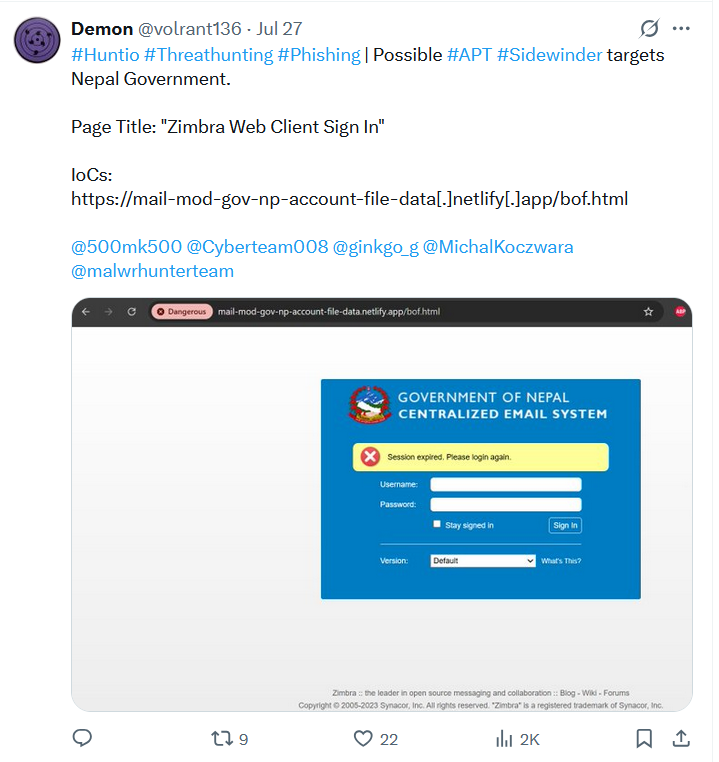
- Sidewinder impersonated government/defense agencies across Bangladesh, Nepal, and Turkey using realistic Zimbra and portal login lures.
- Phishing front-ends were hosted on free static platforms (Netlify, Pages.dev) to rapidly deploy convincing credential-harvesting pages.
- Multiple distinct phishing URLs all POSTed harvested credentials to centralized endpoints mailbox3-inbox1-bd.com and mailbox-inbox-bd.com.
- Credential collection scripts (/2135.php, /idef.php, /dgdp12.php, etc.) were reused across different lures, indicating template-based kits.
- Both collection domains resolve to IP 146.70.118.226 (hosted by M247 Europe SRL), showing shared hosting/infrastructure reuse and redundancy.
- Targeted organizations included DGDP, DGFI, BAF, Bangladesh Police, Roketsan, ASELSAN, and IDEF-related entities.
- Detection and mitigation recommendations include blocking spoofed domains, enforcing MFA, and alerting on Zimbra-like POSTs to external domains.
MITRE Techniques
- [T1566] Phishing – Sidewinder used spear-phishing messages with weaponized documents and malicious links to lure victims into fake login pages (“…phishing campaigns mimic official communication to trick victims into entering credentials…”).
- [T1222] Web Service – Abuse of legitimate web hosting (Netlify, Pages.dev) to host credential-harvesting pages (“…front-end domains are hosted on free services like Netlify and Pages.dev, commonly abused…”).
- [T1078] Valid Accounts (Credential Harvesting) – Harvested credentials via cloned Zimbra/login forms that POST to attacker-controlled endpoints (“…prompting users to enter credentials that were POSTed to mailbox3-inbox1-bd[.]com…”).
- [T1588] Obtain Infrastructure – Reuse of centralized collection domains and backup endpoints (mailbox3-inbox1-bd.com, mailbox-inbox-bd.com) and shared IP 146.70.118.226 indicating infrastructure acquisition and reuse (“…both resolves to the same IP address 146.70.118.226…”).
Indicators of Compromise
- [Domain] credential exfiltration endpoints – mailbox3-inbox1-bd.com, mailbox-inbox-bd.com
- [IP Address] hosting for collection domains – 146.70.118.226 (M247 Europe SRL; resolves for both mailbox domains)
- [URLs] phishing front-ends (examples) – mail-mod-gov-np-account-file-data.netlify.app/bof.html, mail.gov.bd.account.file.updatemind52.com/CeqKyQXz (and 12 more phishing URLs)
- [HTTP Paths/Files] reused POST scripts – /2135.php, /idef.php, /dgdp12.php (used across multiple phishing lures)
Read more: https://hunt.io/blog/apt-sidewinder-netlify-government-phishing