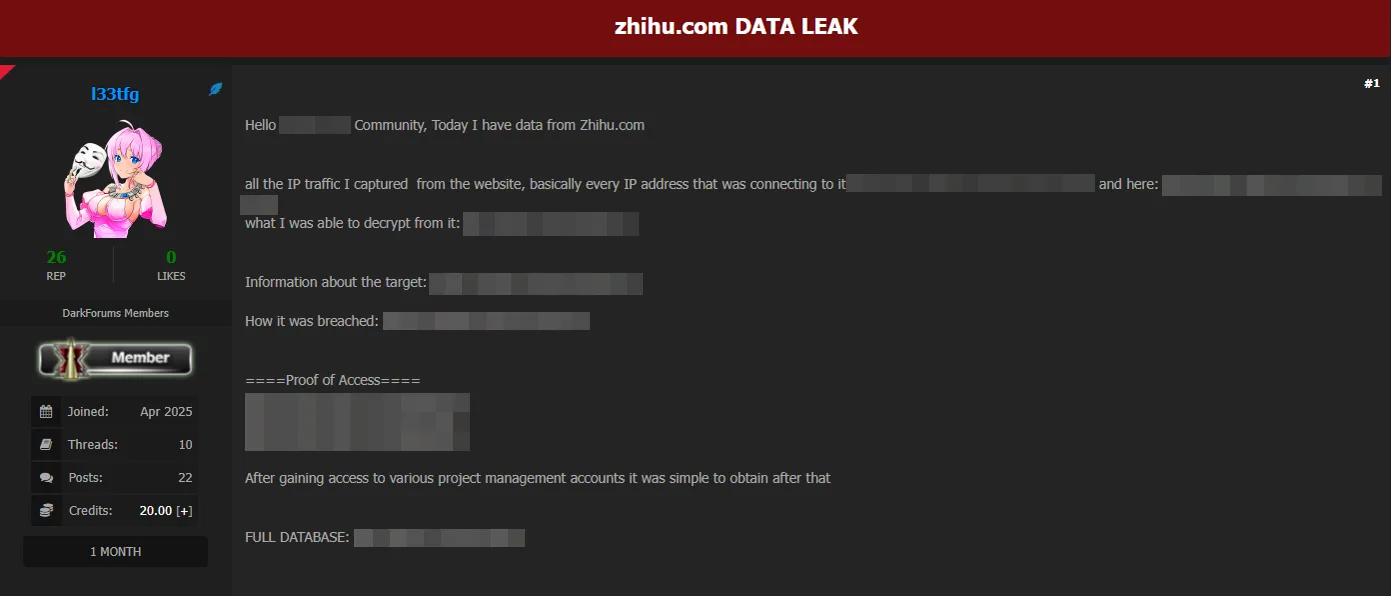
The attacker described their methods for breaching a website, including capturing and decrypting IP traffic and accessing project management accounts. They provided links to files, decrypted data, images as proof, and a full database for download. #IPTrafficDecryption #DataLeakage
Keypoints
- The attacker managed to decrypt specific information by intercepting IP traffic from the target website.
- Access to project management accounts enabled the attacker to extract sensitive data.
- Evidence includes files with captured network traffic, decrypted information, and proof images.
- The attacker claims to have shared the entire database through a direct link.
- External links reveal details about the breach’s target systems and breach methodology.
Read More: https://dailydarkweb.net/alleged-data-breach-impacts-prominent-chinese-qa-platform-zhihu/