The article analyzes an adaptive phishing email that spoofed an internal sender and delivered an active HTML attachment which emulates a login page to harvest credentials. The stolen credentials and contextual metadata (public IP, hostname, timestamp) were exfiltrated to an attacker-controlled Telegram bot using the Telegram Bot API. #TelegramBotAPI #DMARC
Keypoints
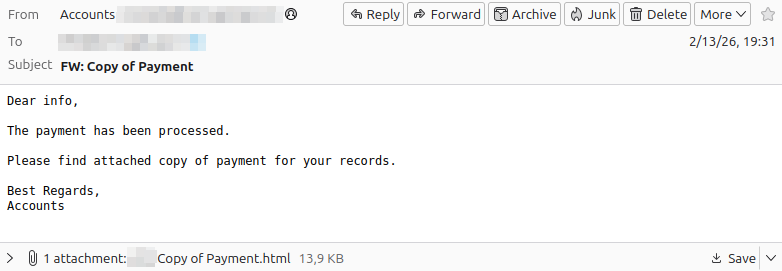
- The phishing message impersonated an internal address by spoofing the sender while being sent from external, unauthorized SMTP infrastructure.
- The attachment was an HTML file containing JavaScript that rendered a fake login form to collect email and password inputs.
- The HTML page prefilled the victim’s email via a hidden field, enabling targeted attacks against specific recipients or domains.
- The JavaScript was lightly obfuscated (document.write(unescape(…))) and collected contextual data such as public IP, approximate geolocation, hostname, timestamp, and attempt count.
- Collected credentials and metadata were exfiltrated via the Telegram Bot API using a BOT_TOKEN and CHAT_ID embedded in the page’s code.
- The page used client-side CAPTCHA and staged “Login failed” messages followed by redirection to a legitimate site to reduce suspicion after interaction.
- Mitigations recommended include strict SPF/DKIM/DMARC enforcement and restrictive policies for active attachments like HTML files.
MITRE Techniques
- [T1566 ] Phishing – Use of an email with a malicious HTML attachment and sender spoofing to induce user interaction; ‘The message has a subject related to a supposed payment and contains an attached HTML file.’
- [T1204 ] User Execution – Reliance on the user to open the attached HTML and submit credentials via the form; ‘The file is an HTML page with JavaScript integrated. Once opened in the browser, it behaves like a small application.’
- [T1027 ] Obfuscated Files or Information – JavaScript obfuscation used to hinder analysis and evade simple pattern detection; ‘The main script is encapsulated in a call document.write(unescape(…)).’
- [T1082 ] System Information Discovery – Collection of environment and contextual information (public IP, geo data, hostname, timestamp, attempt counter) before exfiltration; ‘the script attempts to gather some information, like public IP and approximate geographic data.’
- [T1567 ] Exfiltration Over Web Service – Exfiltration of credentials and metadata via HTTP requests to the Telegram Bot API using embedded bot token and chat ID; ‘the code contains a BOT_TOKEN, a CHAT_ID and the Telegram Bot API endpoint.’
Indicators of Compromise
- [File ] Credential-stealing HTML attachment used as the delivery vector – example: attached .html login page (generic HTML attachment containing JavaScript).
- [Domain ] External API endpoint used for exfiltration – example: api.telegram.org (Telegram Bot API endpoint).
- [Secrets / Credentials ] Embedded bot and chat identifiers in the page code used to receive exfiltrated data – example: BOT_TOKEN, CHAT_ID.
- [Email Headers / Sending Infrastructure ] Spoofed sender visible vs. actual relay in SMTP headers indicating external sending servers – example: ‘Received’ header showing external relay (specific IPs not provided in article).
- [Code Pattern ] Lightweight obfuscation and script patterns useful for detection – example: document.write(unescape(…)), hidden form field prefill with recipient email.